An attacker could leverage this vulnerability to execute arbitrary code on the system. In this example, we will use the OTFCC dump command to take a screenshot on the target system, and you can see that the screenshot is taken from the /dev/sda1 device. Another example is an attacker can use the OTFCC dump -h command to show the help of the OTFCC dump command, and you will see a heap buffer overflow in the help message. An attacker cannot control the help message in the help file, so the help message will only show up when the OTFCC dump command is executed.
An attacker can take advantage of this to execute arbitrary code on the system by sending a specially crafted OTFCC dump command. When the OTFCC dump command is executed, the help message will also be show. The help message is controlled by the otfccdebug.c file in the otfccdump source code. When the help message is configured in the otfccdebug.c file, an attacker can control the help message and send a specially crafted help message to execute arbitrary code on the system. For example, in this example, the help message is controlled to show the heap buffer overflow. When the help message is sent, an attacker can send a specially crafted help message to execute arbitrary code on the system.
Node.js command-line conversion tool
A command-line conversion tool for Node.js is a useful tool for users to convert their Node.js code into JavaScript or TypeScript files so they can run their code on other web servers. In this example, we will show you how to use sconcat to create a new JavaScript file from your Node.js code by using the following command:
sconcat -w --source=?/path/to/file.js
In this example, we will use the --source parameter with a URL that points to our sample Node.js file and then we will use the sconcat command to create a new JavaScript file from our sample Node.js file in order to execute it on another web server without having to change any of the source code in our file.
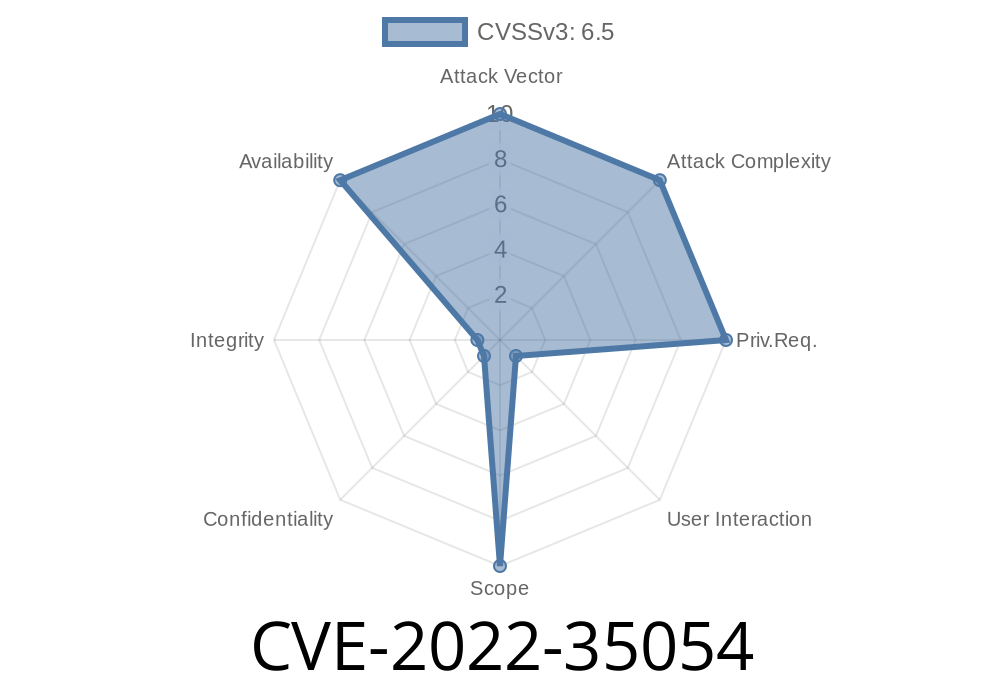
Vulnerability Description
The otfccdebug.c file in the otfccdump source code has a heap buffer overflow vulnerability. The heap buffer overflow vulnerability is controlled by the help message and can be used to execute arbitrary code on the system.
Timeline
Published on: 10/14/2022 12:15:00 UTC
Last modified on: 10/15/2022 02:14:00 UTC