Binutils is a crucial suite of tools used in compiling programs, and readelf is one such tool for displaying information about ELF (Executable and Linkable Format) files. In July 2022, CVE-2022-35206 was published, highlighting a null pointer dereference vulnerability in readelf, specifically in version 2.38.50. This post dives deep into what the vulnerability is, the affected code, how it could be exploited, and what it means for users and maintainers.
What Is CVE-2022-35206?
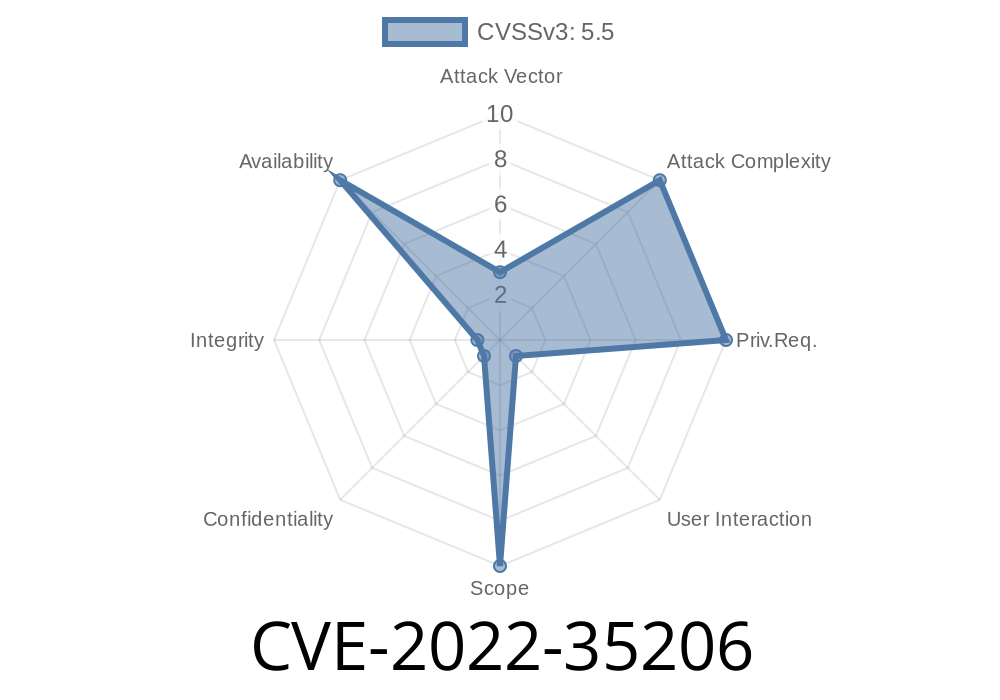
CVE-2022-35206 is a security issue caused by a null pointer dereference bug in the readelf tool, part of GNU Binutils. The bug is located in the function read_and_display_attr_value() within the file dwarf.c. If a specially crafted (typically malformed) ELF file is supplied to readelf, the program can crash by attempting to access memory through a null pointer.
Where’s the Problem?
The specific problem occurs in how readelf reads and interprets DWARF debugging information inside ELF files. If the attributes or values within this information are structured in a way the code does not expect, some pointers that are meant to be initialized will remain null. If the code tries to read from or write to these pointers, it dereferences a null pointer, causing a crash (segmentation fault).
Let’s look at the critical function, simplified for clarity
void read_and_display_attr_value (unsigned attr, unsigned form) {
...
char *info = get_attr_info (attr, form); // this can return NULL on malformed input
...
printf("%s\n", info); // Dereferencing null if info == NULL
}
In the above, if the crafted ELF file confuses get_attr_info(), it may return NULL. The next line tries to print it anyway, causing a null pointer dereference — leading to a process crash.
Here’s a sketch of how you can trigger the bug
# Crash the vulnerable readelf by providing a malformed ELF file
readelf -w malcrafted.elf
*The contents of malcrafted.elf would need to be created with malicious or minimal DWARF data triggering the logic error (often via fuzzing or hex editing).*
Impact & Exploit Details
- Impact: This is a denial of service, meaning it crashes the tool. There’s no code execution, so it’s not a direct path to take over a system, but it's bad for automated systems processing ELFs or build servers.
- Exploitability: An attacker needs to craft a malicious ELF file with broken DWARF attributes. On platforms processing untrusted programs, this could allow an attacker to disrupt operations by dropping a bad file in a watched directory.
Real Exploit Scenario
Consider a CI/CD pipeline using readelf to inspect or validate uploaded artifacts. If an attacker uploads a malformed ELF file, the pipeline may crash at the analysis step, potentially stopping or delaying builds, or causing unhandled errors.
Fix & Mitigation
The maintainers released patches making sure that pointers are always checked for NULL before being dereferenced.
Example of Fixed Code
void read_and_display_attr_value(unsigned attr, unsigned form) {
...
char *info = get_attr_info(attr, form);
if (info != NULL) {
printf("%s\n", info);
} else {
printf("[Invalid attribute]\n");
}
}
Solution:
- Update Binutils: Get the latest version from the GNU Binutils download page.
- Patch in Place: Apply available patches in your distribution—most mainstream Linux distributions backported fixes.
References
- CVE Record at NIST
- Binutils commit diff (fix)
- Binutils Project Home
- OSS-Fuzz Issue
- Full source code for dwarf.c
Final Thoughts
CVE-2022-35206 is a classic example of how even simple pointer checks can make software more robust. In open source development—especially for tools as foundational as Binutils—security fixes like this are crucial for everyone’s safety. If you use readelf in any automated workflow or regularly analyze third-party ELF files, make sure you’re running an updated version.
Stay secure, keep your tools patched, and remember: __always check pointers before using them!__
Timeline
Published on: 08/22/2023 19:16:00 UTC
Last modified on: 08/31/2023 00:36:00 UTC