---
Introduction
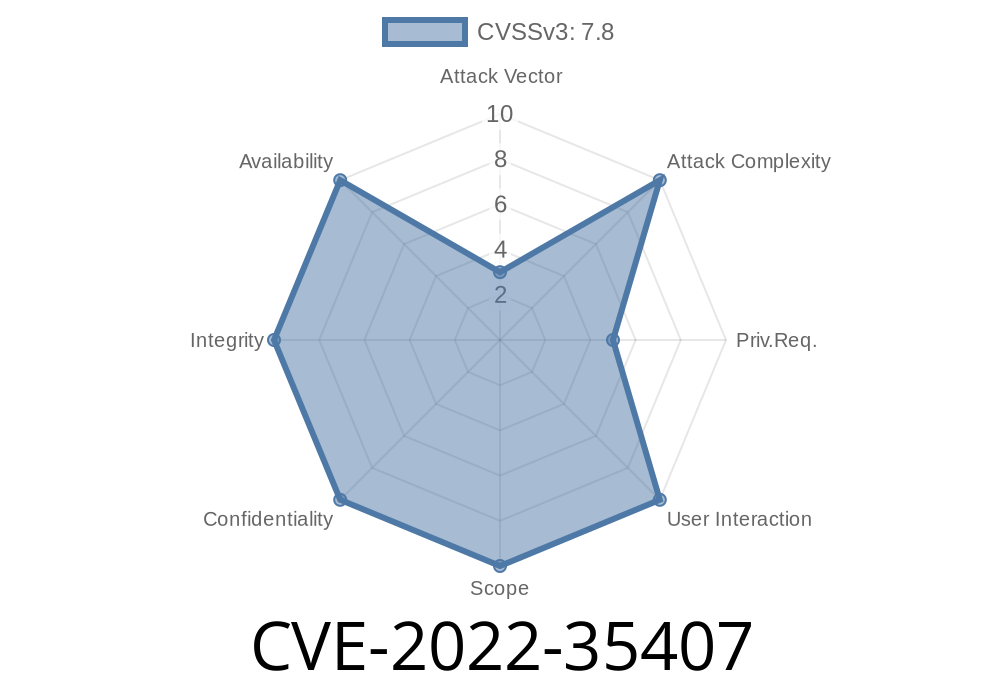
In June 2022, a critical vulnerability tagged CVE-2022-35407 was discovered in the Insyde InsydeH2O UEFI firmware, specifically inside its SetupUtility driver. The flaw is especially concerning because it impacts Intel-based PCs and laptops, with InsydeH2O being a common firmware platform for hundreds of systems. This post will break down what happened, how the bug works, include code for understanding, and what you should do if your devices run on affected UEFI firmware.
What is InsydeH2O and Why Does This Matter?
InsydeH2O is a UEFI firmware used to initialize hardware and start operating systems on many laptops and desktops, particularly on Intel hardware. Vulnerabilities in UEFI are severe, as they can allow attackers to gain low-level, persistent access to a system—bypassing most operating system protections.
Vulnerability Details
CVE-2022-35407 affects InsydeH2O's SetupUtility driver, which handles UEFI settings accessible at boot time (like secure boot, boot order, etc.). The issue lies in the handling of UEFI variables:
Type: Stack buffer overflow
- Cause: The code failed to check if the second variable's size was greater than the allocated buffer, allowing the buffer to be overwritten.
Technical Breakdown
The SetupUtility driver manages system variables for firmware configuration. Two UEFI variables are handled: if the user sets the second variable to a size larger than the first, the provided value could overflow the stack-allocated buffer for the first variable when copied unsafely, potentially overwriting important data, including the return address.
Here's a simplified code snippet resembling what went wrong
// BAD: No size check when copying variable value
void SetUefiVariable(char* new_value, size_t new_size) {
char buffer[256];
// No check if new_size > sizeof(buffer)
memcpy(buffer, new_value, new_size); // buffer overflow here
// ...further processing
}
An attacker running in privileged mode (or with a malicious OS or bootloader) can abuse this by sending an intentionally crafted variable larger than 256 bytes, overwriting memory in a way that could result in arbitrary code execution within the firmware context.
Real UEFI SetVariable Flow (For Reference)
UEFI variables are set via the SetVariable function. If the input buffer is not properly validated, an attacker can do something like:
# Using the UEFI Shell or SMM exploit chain
# Pseudocode for exploiting the bug
data = b"A" * 512 # Overwrite with 512 bytes, twice the buffer size
uefi.SetVariable(
VariableName="TargetVariable",
VendorGuid=guid,
Attributes=attrs,
DataSize=len(data),
Data=data
)
What can an attacker do?
- Gain code execution: The attacker can execute arbitrary code within the firmware at boot, gaining persistent, nearly invisible access.
- Bypass OS-level security: Since attacks happen before the OS boots, protections like antivirus or secure boot can be bypassed.
- Modify secure variables: It’s possible to alter secure boot settings (enabling unsigned OS loading), change boot orders, or plant rootkits.
Who can exploit it?
- Attackers with local admin/root access
Mitigation
- Update your UEFI firmware ASAP: Check with your device or motherboard vendor and update to the latest firmware.
Firmware vendors should fix the vulnerable code by ensuring bounds checks like this
void SetUefiVariable(char* new_value, size_t new_size) {
char buffer[256];
if (new_size > sizeof(buffer)) {
// Handle error: new value is too large
return;
}
memcpy(buffer, new_value, new_size);
// ... further processing
}
References & Further Reading
- Official CVE entry: CVE-2022-35407
- Insyde Security Advisory: https://www.insyde.com/security-pledge/SA-2022035
- Firmware security research: Eclypsium’s blog on UEFI threats
Conclusion
Firmware vulnerabilities like CVE-2022-35407 are high-impact, and the danger is that many users don't regularly update their firmware. If you're responsible for any Intel-based machines, or PC fleets using InsydeH2O UEFI, act now: check for firmware updates and patch immediately. The silent, persistent nature of UEFI-level attacks makes this vulnerability particularly dangerous.
Stay safe by keeping *everything* up to date—hardware and software alike.
*This post is for educational purposes and to help users understand the risks of UEFI vulnerabilities. Do not attempt to exploit these issues on devices you do not own or have explicit permission to test.*
Timeline
Published on: 11/22/2022 02:15:00 UTC
Last modified on: 11/30/2022 18:23:00 UTC