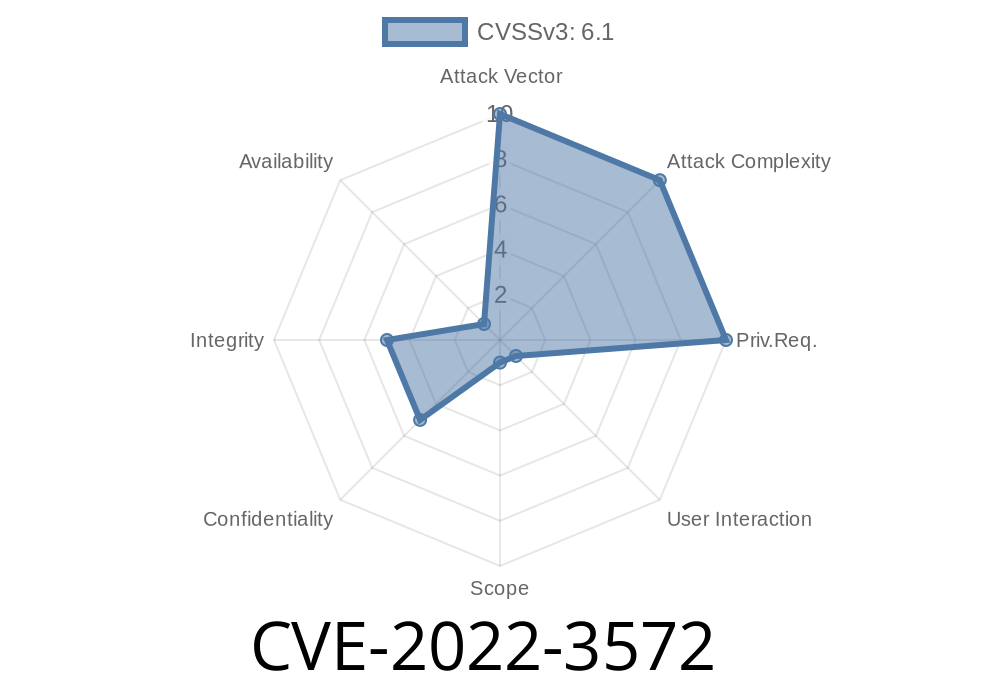
In June 2022, a serious security issue—CVE-2022-3572—was discovered in GitLab Community and Enterprise editions (CE/EE). This vulnerability impacts all versions from 13.5 up to—but not including—15.3.5, 15.4 prior to 15.4.4, and 15.5 prior to 15.5.2.
This post walks you through what was wrong, how it could be exploited, and offers insight into the risk for organizations that ran affected versions. We’ll include code snippets and practical detail, along with references for a deep dive.
What is CVE-2022-3572?
CVE-2022-3572 is a reflected cross-site scripting (XSS) bug in GitLab’s Jira Connect integration settings. By carefully crafting a malicious input, an attacker could trick logged-in users into executing arbitrary actions, potentially stealing their session, changing security settings, or worse.
Quick facts
- Impacted: GitLab CE/EE 13.5–15.3.4, 15.4–15.4.3, 15.5–15.5.1
How Did the Vulnerability Work?
The issue lived in the Jira Connect integration configuration. GitLab allowed users to set certain fields that were used unsafely in the web interface, failing to sanitize user input properly. If an attacker convinced a logged-in user (with appropriate permissions) to click on a specially crafted malicious link, JavaScript of the attacker’s choosing would run in the victim’s browser—as if the victim themselves had executed it.
Prepare a Malicious Link
The attacker would construct a URL to the Jira Connect integration configuration page, with a malicious value for a field (e.g., the “Context Path” or “Webhook URL”). This value might look like:
`
`
Here, the payload in context_path terminates an existing HTML attribute and injects a custom SVG that triggers alert(1) — the classic XSS test.
Social Engineering
The attacker needs a victim to visit this link while logged in to GitLab and with permissions to access that integration.
The Reflected XSS Triggered
If the vulnerable GitLab version rendered this field directly into the page without escaping, the injected script would execute in the context of the victim's session.
Suppose GitLab is hosted at https://gitlab.acme.com. The attacker sends this to a victim
https://gitlab.acme.com/groups/mygroup/-/jira_connect/subscriptions/new?context_path="/><svg/onload=alert('xss')>
On the vulnerable versions, submitting this input would trigger the JavaScript code.
Here’s a *simplified* version of how the unsafe code might’ve behaved
<!-- Pseudocode: Rendering the "context_path" field in HTML without escaping -->
<input name="context_path" value="<%= params[:context_path] %>">
If params[:context_path] contained "/><svg/onload=alert('xss')>, the rendered output becomes
<input name="context_path" value=""/><svg/onload=alert('xss')>">
The browser interprets this as a new SVG tag with an onload handler — instant JavaScript execution.
The fix was to properly escape user input. The fixed code would be
<input name="context_path" value="<%= h(params[:context_path]) %>">
Here, h() ensures the value is converted into harmless HTML, so scripts can’t break out of the attribute.
Users with access to Groups and Projects using Jira Connect integration.
Anyone with social engineering skills and access to craft a malicious URL could have targeted users.
Mitigation
Update immediately if you’re still on these GitLab versions. The safest path is to upgrade to at least 15.3.5, 15.4.4, or 15.5.2.
References and Further Reading
- GitLab Security Release: 15.5.2, 15.4.4, and 15.3.5
- NIST NVD Entry for CVE-2022-3572
- HackerOne - Write-up Example for this Vulnerability (external example)
- OWASP XSS Prevention Cheat Sheet
Takeaway
CVE-2022-3572 is a stark reminder: even trusted integrations like Jira Connect can hide XSS bugs waiting to be exploited. The fix was simple—escape all user-supplied input—but organizations must remain vigilant in patching and reviewing integrations.
*Stay safe, patch often, and treat every user input with suspicion—especially in developer tools like GitLab.*
*If you found this write-up useful, follow us for more deep dives into real-world CVEs and fixes!*
Timeline
Published on: 01/26/2023 21:15:00 UTC
Last modified on: 02/01/2023 17:17:00 UTC