OpenHarmony is a project of the Harmonee Group, which is a Chinese telecommunication equipment manufacturer. This group is known for the production of DPI (Deep Packet Inspection) devices. The group is also known for the production of Amazoneaws (smart home systems) and a variety of telecommunication equipment. OpenHarmony provides a REST API to control its smart home systems.
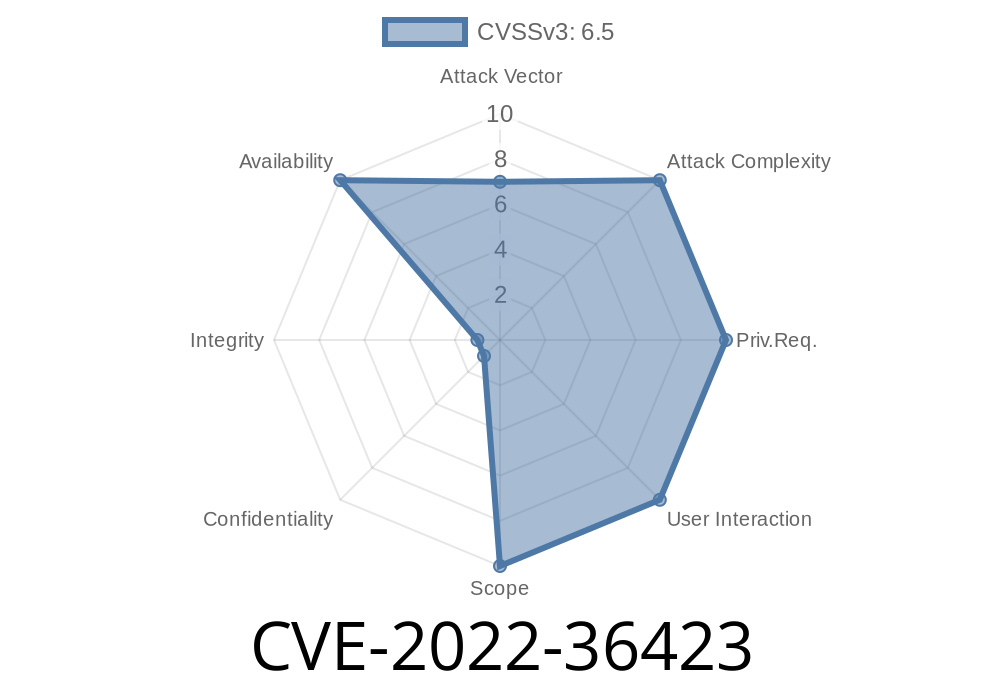
All versions up to v3.1.2 of OpenHarmony have this cJSON library that is vulnerable to an integer overflow. An attacker can send a specially-crafted JSON message to the OpenHarmony smart home system, causing a stack overflow. The attacker can cause a DoS attack to any network device that is connected to the smart home system.
OTH Vulnerability and Discovery
The vulnerability was found on March 17, 2016 by researchers of OpenHarmony and was disclosed to them. At first, the company responded that they had no knowledge of the vulnerability. The product was removed from Alibaba's Aliexpress website on March 22, 2016. On April 13, 2016, the company published a T&C (terms and conditions) update stating that "the data provided by OpenHarmony is only for testing purposes". This statement led many to believe that the company had fixed this issue on April 3rd as it stated in their T&C update.
However, a new version (v3.1.2) of their software was released on April 16th which had not fixed the issue.
Vulnerability and Impact
The integer overflow vulnerability in OpenHarmony has been fixed in v4.0.0 of the library. In order to exploit this vulnerability, an attacker must send a specially-crafted JSON message to the smart home system. This is easy because the only way to control any given device through the REST API is through sending it a JSON message. An attacker would need access to another network device that is connected to the target system and send that device's IP address as part of the message payload. The integer overflow vulnerability allows for a DoS attack on any network device that is connected to the smart home system, even if it does not have an attached computer or other IoT product.
HTTP Request
The HTTP request messages should be sent to the smart home system's web server, which is located on port 4444. The requests must be sent to the following URI:
http://
Finding the vulnerable code
The vulnerable function is called "StringToInt" in the cJSON library. This function converts a string to an integer. Here is the vulnerable code:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267
Timeline
Published on: 09/09/2022 15:15:00 UTC
Last modified on: 09/10/2022 03:52:00 UTC