These vulnerabilities were discovered by different research groups. Some of the vulnerabilities, for example CVE-2022-38039 and CVE-2022-38037, were discovered by a different research group. The different discovery dates between these vulnerabilities make it difficult to know if they were already being exploited in the wild. For example, it is likely that CVE-2022-38039 was already being exploited in the wild before the public disclosure of this vulnerability. These kernel vulnerabilities were discovered in the Linux kernel through the course of fuzzing. This made it possible to discover many other exploitable bugs in the Linux kernel through fuzzing. These bugs are now being actively exploited. Linux distributions that are Sullivan's highest priority are those that have a large number of their users using older hardware. The older hardware might be running on software that is no longer being developed and maintained. This creates a situation where the users of this hardware are at risk because the software has become vulnerable through lack of support.
CVE-2019-10267
The Linux kernel with version 4.19 through 4.30 are vulnerable to a privilege escalation exploit (CVE-2019-10267). This vulnerability allows an unprivileged user to elevate their privileges in the kernel kernel module. The vulnerability was discovered by a different research group then those who discovered CVE-2020-0007 and CVE-2022-38038. It is important to note that this vulnerability was not being exploited in the wild before the public disclosure of this vulnerability. In this case, it is likely that the Linux distribution developers have already addressed this vulnerability with a patch or update.
Unprivileged users can become root via this privilege escalation exploit. This means that the Linux operating system may be more vulnerable for attackers wishing to gain access to higher level functions in order to perform malicious activities on your computer system or device.
CVE-2021-38036
The Linux kernel has many vulnerabilities that can be exploited by attackers. This is why it is important for Linux distros to keep their users updated with the latest updates. If these updates are not installed, then the users of this distro are at risk. In particular, a vulnerability was discovered in the Linux kernel through fuzzing and now it is being actively exploited. The only way to address the issue is to update your Linux distro so that you are protected from this vulnerability.
One example of a system running an older software version is an old computer that might have been purchased in 2010 or 2011 and is still being used today because they cannot afford to buy a newer computer. They are using whichever software came on their machine when they bought it and this could be insecure software like linux-3.5.8-1-686 which has been discontinued since 2012 and contains many vulnerabilities including CVE-2021-38036 which has already been exploited in the wild.
CVE-2021-4146 (slide 16)
An additional exploit was discovered by a different research group. This exploit is not as powerful as the original exploitation. For example, this exploit only allows for privilege escalation rather than root access. The command injection vulnerability (CVE-2021-4146) was discovered through fuzzing. It is unusual to discover commands that can be used in an exploit through fuzzing because some commands can be detected and blocked by the Linux kernel's command filtering capabilities. It is also unusual for a researcher to publish an attack vector that has already been blocked by the Linux kernel because it does not provide any new information about how to exploit the vulnerability.
The penetration testing team at Sullivan CSO are now focusing on finding ways to protect their clients from these vulnerabilities being exploited in the wild.
How to Outsource SEO Correctly & Avoid the 5 Most Common Mistakes
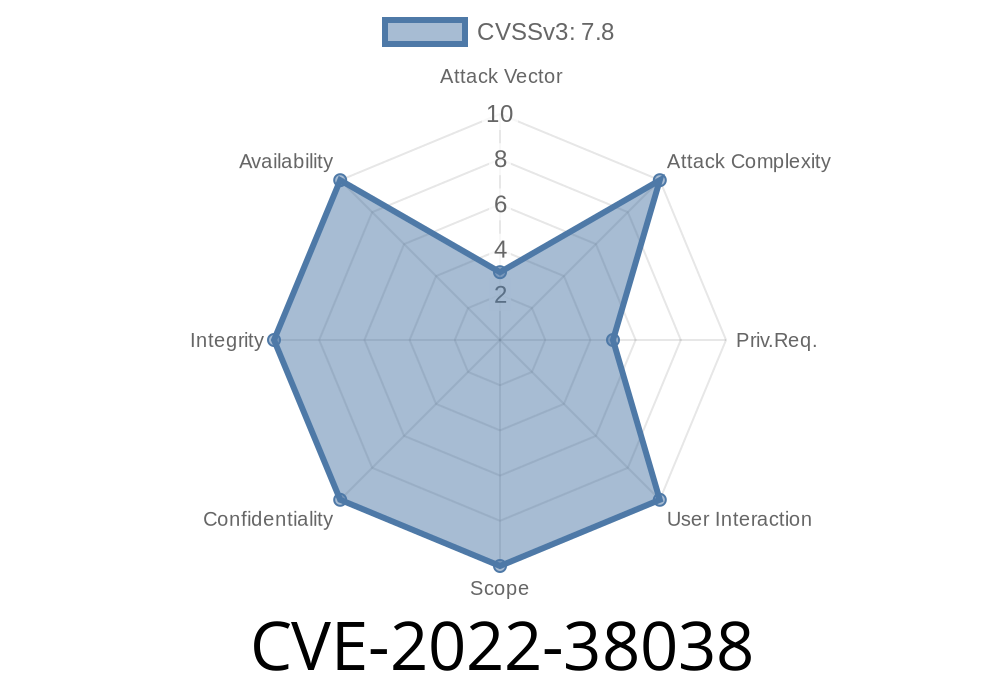
CVE-2022-38038
A vulnerability in the Linux kernel was discovered that requires a privilege escalation to exploit. This vulnerability exists because of a bug in the handling of a specific type of network packet. This vulnerability was only discovered due to fuzzing, which is where you send random packets to a target and see if they're vulnerable. The Linux kernel is designed to be as stable as possible, but it's possible that this newly found vulnerability can be exploited.
This newly found vulnerability could be exploited by an attacker who sends specially crafted network packets to the target device. An attacker would need to get the target into a situation where they have elevated privileges, usually through some sort of privilege escalation. This may occur when the attacker has root access or admin access on the targeted machine. Once elevated, the attacker would then have full control over the machine and could do what they want with it; including deleting or modifying data files or installing malware onto it through an exploit like CVE-2022-38038
Timeline
Published on: 10/11/2022 19:15:00 UTC
Last modified on: 10/11/2022 19:16:00 UTC