In late 2022, security researchers discovered a vulnerability – now identified as CVE-2022-3807 – in the open-source multimedia framework Axiomatic Bento4. This vulnerability was tied to an incomplete fix for a previous issue (CVE-2019-13238), and it opens affected systems to a potential Denial-of-Service (DoS) attack via resource consumption. Here, we break down what went wrong, how the problem can be exploited, and what you need to know to stay safe.
What is Axiomatic Bento4?
Bento4 is a popular C++ toolkit for working with MP4 files and streams. Developers use it widely in video processing and streaming servers.
Details of CVE-2022-3807
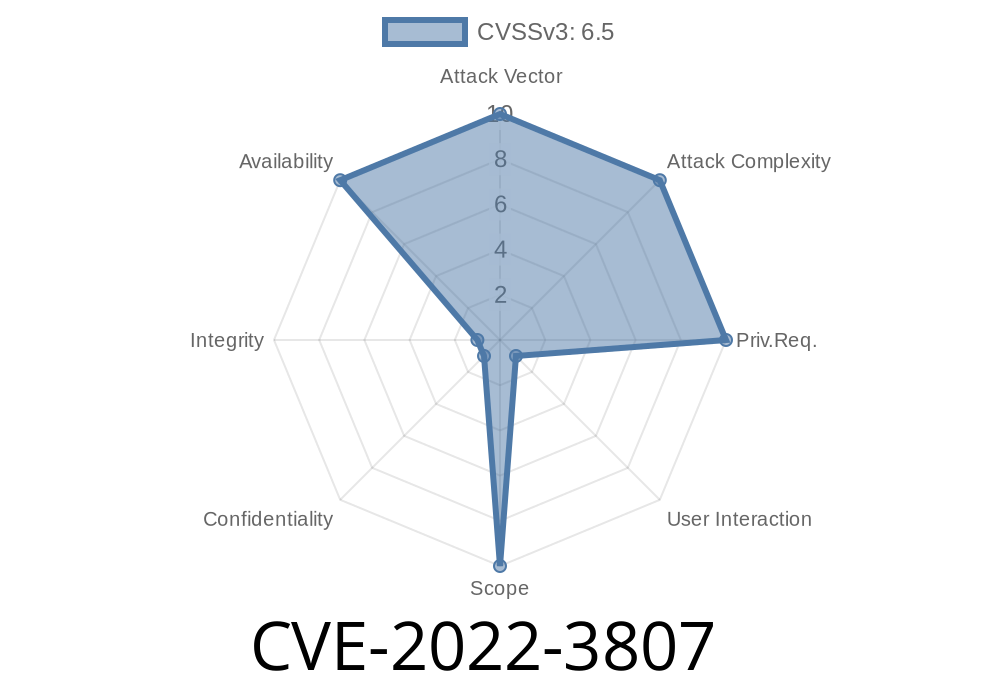
- Vulnerability Identifier: CVE-2022-3807
How Did This Happen?
Back in 2019, a resource usage problem (CVE-2019-13238) was found in Bento4. Developers released a patch, but it didn't fully close the vulnerability, leaving a loophole. Attackers figured out that by sending specially crafted MP4 files, they could trigger endless parsing loops or high memory consumption. This would tie up server resources, making the system slow or even unresponsive.
Exploitation: What Does the Attack Look Like?
The vulnerability can be exploited remotely by an attacker who sends a malicious MP4 to a web service using Bento4. The parsing of that file burns up system resources (like CPU or memory), leading to a possible denial of service situation.
Attacker's Steps
1. Create or download a malicious MP4 file (a PoC is public in the Bento4 issue tracker).
Code Snippet: How Would an MP4 Trigger the Problem?
Below is a simplified code snippet (C++) showing how an application using Bento4 might parse media files—notice how it doesn’t check for overly large or deeply nested boxes, leading to resource burns:
#include "Ap4.h"
int main(int argc, char** argv) {
if (argc < 2) return 1;
const char* filename = argv[1];
// Open the file (user could provide a malicious file!)
Ap4_File *file = new Ap4_File(new Ap4_FileByteStream(filename, Ap4_FileByteStream::STREAM_MODE_READ));
// Parse all movie boxes (no size/depth limit!)
Ap4_Movie* movie = file->GetMovie();
// Application continues, possibly locks up here if the file is malicious
// ...
delete movie;
delete file;
return ;
}
What’s missing?
A malformed MP4 file could send the parser into a loop or make it hog memory.
### How To Fix / Mitigate
- Upgrade: Keep Bento4 up to date. Check for patches on the official repo.
Add limits or timeouts in your application logic.
- Monitor systems for unusual spikes in memory/CPU when handling MP4 files.
References and Resources
- Vulnerability Database Entry: VDB-212660 / VulDB
- Bento4 GitHub Repository: github.com/axiomatic-systems/Bento4
- Original Issue/Exploit PoC: GitHub Issue #690
- CVE Entry: NVD CVE-2022-3807
Conclusion
CVE-2022-3807 is a solid reminder that incomplete patches can leave applications open to resource-based attacks. If you run or build on top of Bento4, check your version and patch early. Be wary of the files you process, and always keep resource controls in place when handling user input.
For further reading or questions, check the links above—or follow updates from the Bento4 maintainers. Stay safe!
Timeline
Published on: 11/01/2022 20:15:00 UTC
Last modified on: 11/03/2022 15:11:00 UTC