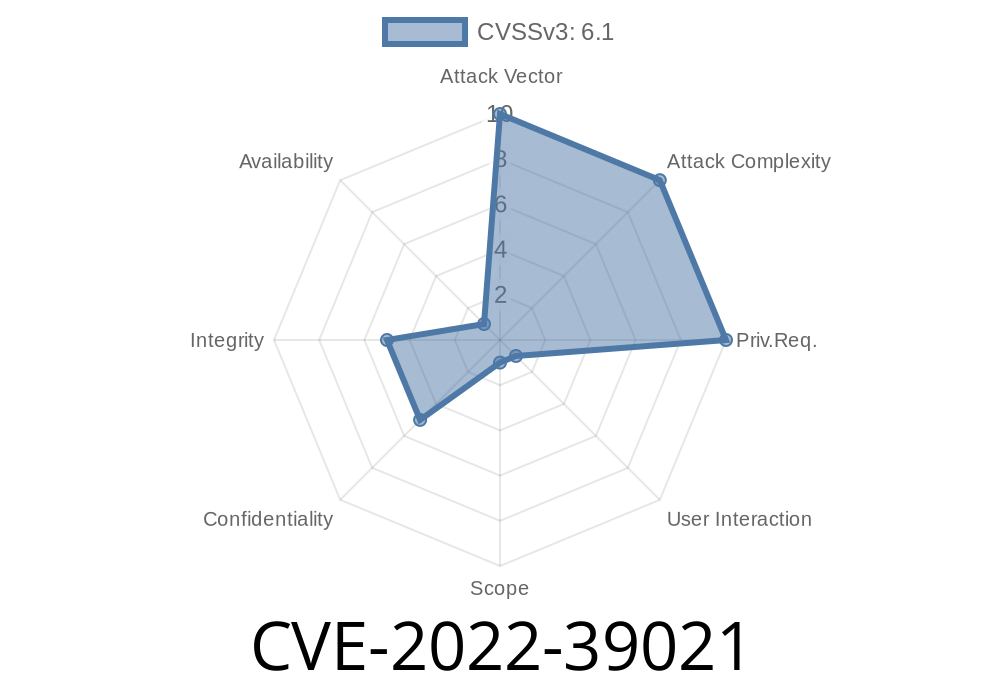
In 2022, a vulnerability labeled CVE-2022-39021 was discovered in the U-Office Force suite, specifically affecting its user login function. This issue may seem simple, but it can be leveraged for more serious attacks like phishing or credential theft. In this article, we break down what this vulnerability is, how it works, and what you can do to stay protected.
What is CVE-2022-39021?
CVE-2022-39021 is an Open Redirect vulnerability in the login function of U-Office Force. In plain language, an open redirect bug lets attackers trick the system into sending users anywhere on the web, just by changing a link. This flaw doesn’t need prior login—in other words, anyone on the internet can exploit it.
Here’s how it works:
When a user tries to access a resource in U-Office Force that needs authentication, the web application often redirects them to a login page and, after successful login, sends them onward with a redirect or next parameter in the URL. The problem is that the app doesn’t check where that parameter points to, allowing anyone to use it.
Any organization using U-Office Force, especially if it’s exposed to the internet.
- End users who rely on links (received by email or chat) that could be exploited by a malicious actor.
Potential Impact
- Attackers may redirect users to fake login pages (phishing), malware sites, or other malicious destinations, making it easier to steal credentials or compromise devices.
`
https://evil.example.com/" rel="nofollow">https://[your-uoffice-server]/login?redirect=https://evil.example.com/
Victim clicks the link and is presented with the normal U-Office Force login page.
4. After logging in (or even without logging in, depending on implementation), the user is sent to https://evil.example.com/ rather than their original destination.
Code Example: Vulnerable Login Logic
Here’s a simple look at what vulnerable code might look like in a Python/Flask web app (for illustration):
# Example: Vulnerable login handler (pseudo-code)
@app.route('/login')
def login():
redirect_url = request.args.get('redirect', '/home')
# (Authentication logic) ...
return redirect(redirect_url)
The problem?
There’s no check to ensure redirect_url is a safe/allowed address.
## How to Fix / Mitigate
Patch or Update:
Check with the vendor for updated U-Office Force versions or security patches.
Sanitize the redirect Parameter:
Make sure only local or specific URLs are allowed! For example, restrict redirects to your own domain:
from urllib.parse import urlparse, urljoin
@app.route('/login')
def login():
redirect_url = request.args.get('redirect', '/home')
# Allow only local redirects
base_url = request.host_url
target_url = urljoin(base_url, redirect_url)
if not target_url.startswith(base_url):
target_url = '/home'
# (Authentication logic) ...
return redirect(target_url)
References
- CVE-2022-39021, Mitre NVD Entry
- Open Redirect Vulnerability, OWASP Guide
- U-Office homepage (Chinese)
Timeline
Published on: 10/31/2022 07:15:00 UTC