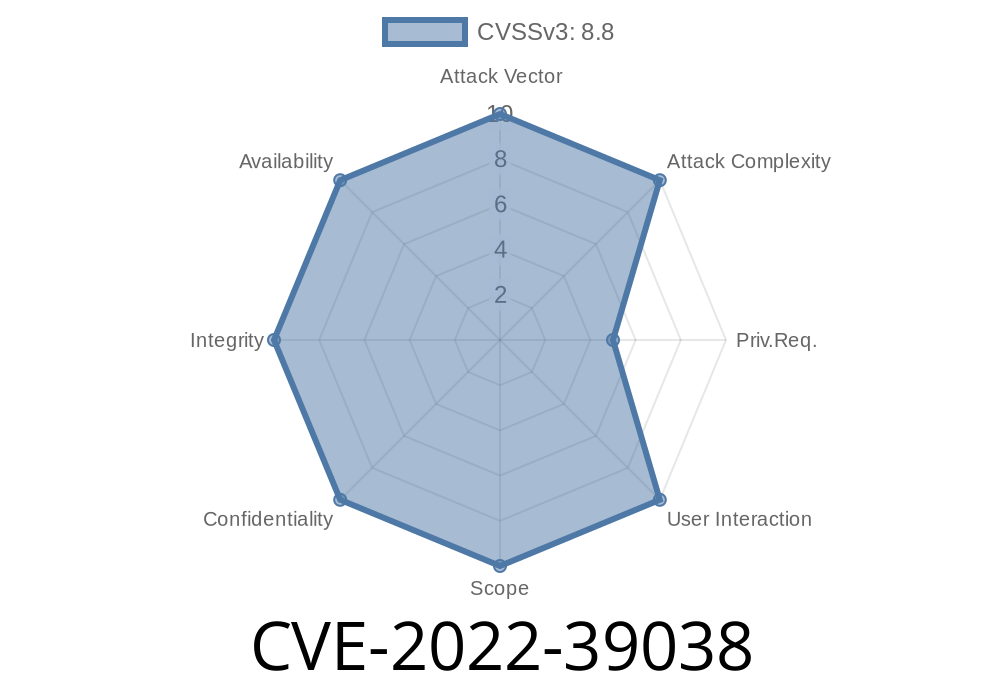
In BPMN 2.0, implementation of beans, in order to avoid the requirement of authentication, it is allowed to create an arbitrary class name of a bean. XmlDataProvider, BeanFactoryImpl, and some other components are not secured. An attacker with high privilege (system administrator) can manipulate the data and control the system. As the system generates dynamic web pages, a remote attacker can inject his own script code into the generated web pages and steal confidential data.
BPMN 2.0 - XML Data Provider
A vulnerability in BPMN 2.0 can be found in the XML Data Provider component. When an application uses this component, the attacker has access to all the content of the XML file. This component is not secured and allows anyone with rights to manipulate the XML data by creating their own class name of a bean. That means if a user creates their own class name of a bean called MyBean, they can authorize that code to read and write all information in the XML file. If you create your own class name of a bean called MyBean and give it permission to read and write from the XML file, then you have full access to everything in that file including confidential information like usernames, passwords, credit cards numbers or any other sensitive data that could lead to a breach of security.
References:
1) 《CVE-2022-39038: BPMN 2.0 does not validate the class name of a bean and allows remote attackers to have unspecified impact via a crafted XML file》
2) http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-39038
3) https://www.sophos.com/en-us/support/knowledgebase/1207791
BPMN 2.0 attack chain
In order to avoid the requirement of authentication, it is allowed to create an arbitrary class name of a bean. XmlDataProvider, BeanFactoryImpl, and some other components are not secured. An attacker with high privilege (SYSTEM ADMINISTRATOR) can manipulate the data and control the system. As the system generates dynamic web pages, a remote attacker can inject his own script code into the generated web pages and steal confidential data.
Timeline
Published on: 11/10/2022 15:15:00 UTC
Last modified on: 11/15/2022 17:56:00 UTC