When installing a new app that requires OAuth 2.0, the user has to accept the terms and conditions of the app by tapping on a consent button. If the consent flow is not received, the user is prompted with a message stating: “This app uses Facebook login. You gave this app permission to access your data.” The consent process also involves entering authorization codes sent by the user on their behalf to the app, which are then exchanged for a token. When installing a new app, users are advised to double-check the app's consent screen and the website where the consent is received.
What you can do to prevent CVE-2022-39222?
A lot of apps use Facebook login, and the app's consent flow is a major point of concern for app users and developers. As a developer, it should go without saying that you should make sure your consent screen is correct. If there are any errors in your consent screen, you have to fix them before you can release the app.
The biggest issue with this vulnerability is that it often goes unnoticed because the user doesn't receive an error message. Most users will be too busy trying to sign in to their account or install the app to notice errors on their device. If your consent screen isn't making sense, then your users may have clicked “allow” because they don't know what they're clicking on. Developers should take precautions against this problem by implementing an error message like "oops! something went wrong" if a user clicks "allow."
Additionally, permissions should only be granted when the user has explicitly opted-in to allow these permissions beforehand. This means asking for permission upfront instead of waiting until later when it's too late for users to change their mind about granting access.
How do I use the CVE-2022-39222?
If you are installing an app that uses OAuth 2.0, it’s important to double-check consent flows and the website where the consent is received. After logging into your mobile device, go to Settings>Accounts>Facebook Apps>Manage Apps and tap on “AddApp.” If you see Facebook App Installer in this list of apps, tap on it to open the app's installation screen and read through the terms and conditions.
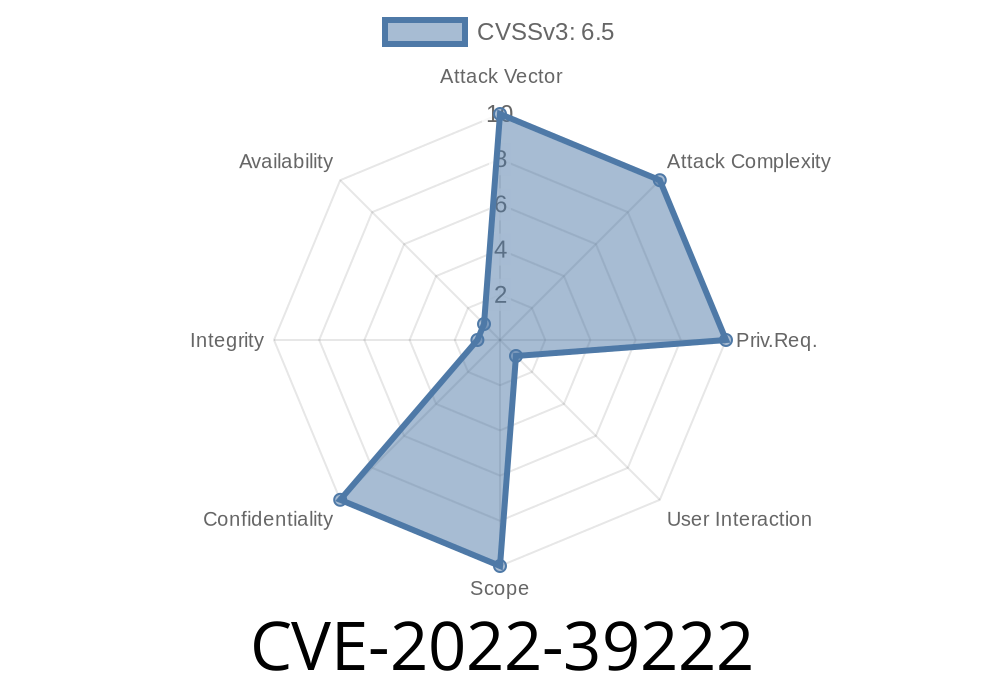
Vulnerability overview
Vulnerable apps are those that require users to enter the consent flow in order to install the app. Once installed, the app is granted an OAuth 2.0 token by Facebook and can use this token to access any user's information on Facebook. This includes information such as their likes, posts, friends list and more.
This vulnerability affects all apps that require users to enter consent in order to install them or access their data. In other words, every single app that uses OAuth 2.0 is vulnerable if it requires a user-given consent flow before installation can be completed.
How to Bypass Consent Screen in Android Apps?
When installing an app that requires OAuth 2.0 on the Android platform, the user has to accept the terms and conditions of the app by tapping on a consent button. If the consent flow is not received, the user is prompted with a message stating “This app uses Facebook login. You gave this app permission to access your data,” and they have to enter authorization codes sent by the user on their behalf to the app, which are then exchanged for a token. When installing an app on Android devices, users are advised to double-check the app's consent screen and website where they will be asked for their consent.
Timeline
Published on: 10/06/2022 18:16:00 UTC
Last modified on: 10/07/2022 17:19:00 UTC