or by having the victim clone a malicious repository as a submodule from any source. Cloning a repository with the `--recurse-submodules` option has the same risk as cloning a repository with the `--recurse-submodules` option. When performing a remote clone (where the source and target of the clone are on different machines), Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source. When performing a remote clone (where the source and target of the clone are on different machines), Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source.
Addition of malicious remote repository
A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source. When performing a remote clone (where the source and target of the clone are on different machines), Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source.
Git Commands - Remote Execution
The `git clone` command does not support the `--recurse-submodules` option. The `git clone` command does not support the `--recurse-submodules` option.
In short, when cloning a repository with the `--recurse-submodules` option, Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source. In short, when cloning a repository with the `--recurse-submodules` option, Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source.
Remote Code Execution
Git is vulnerable to remote code execution when cloning a repository that has a symbolic link pointing at sensitive information on the victim's machine. Remote code execution could be achieved by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source.
When performing a remote clone (where the source and target of the clone are on different machines), Git copies the contents of the source's `$GIT_DIR/objects` directory into the destination by copying them. A malicious actor could convince a victim to clone a repository with a symbolic link pointing at sensitive information on the victim's machine. This can be done either by having the victim clone a malicious repository on the same machine, or by having them clone a malicious repository as a submodule from any source.
Timeline
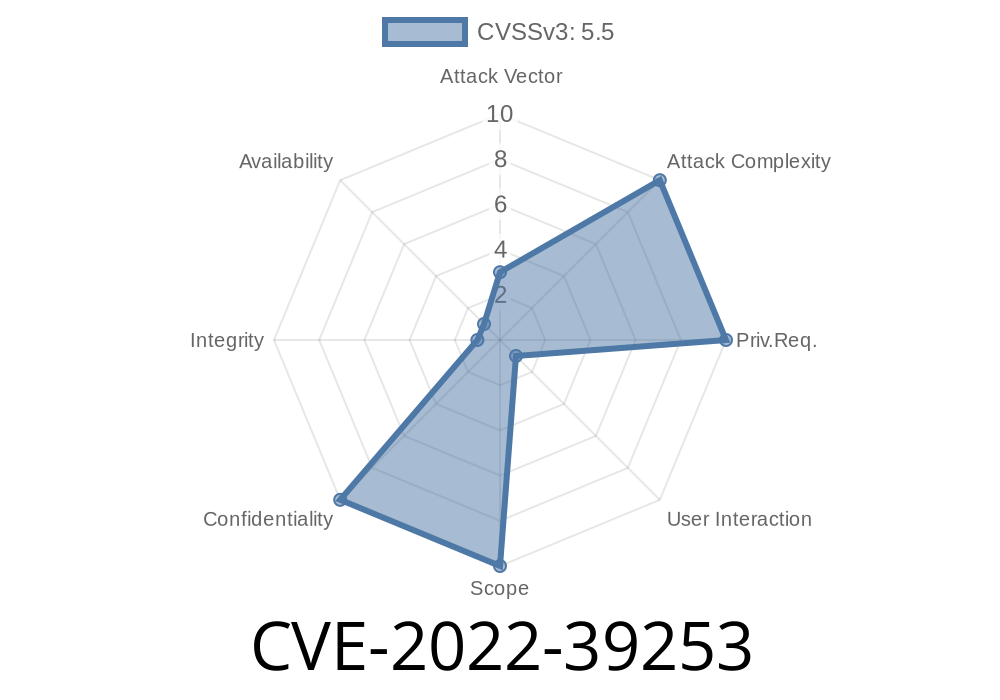
Published on: 10/19/2022 11:15:00 UTC
Last modified on: 11/14/2022 15:15:00 UTC
References
- https://github.com/git/git/security/advisories/GHSA-3wp6-j8xr-qw85
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/VFYXCTLOSESYIP72BUYD6ECDIMUM4WMB/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/UKFHE4KVD7EKS5J3KTDFVBEKU3CLXGVV/
- https://support.apple.com/kb/HT213496
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/OHNO2FB55CPX47BAXMBWUBGWHO6N6ZZH/
- http://seclists.org/fulldisclosure/2022/Nov/1
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/C7B6JPKX5CGGLAHXJVQMIZNNEEB72FHD/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/JMQWGMDLX6KTVWW5JZLVPI7ICAK72TN7/
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-39253