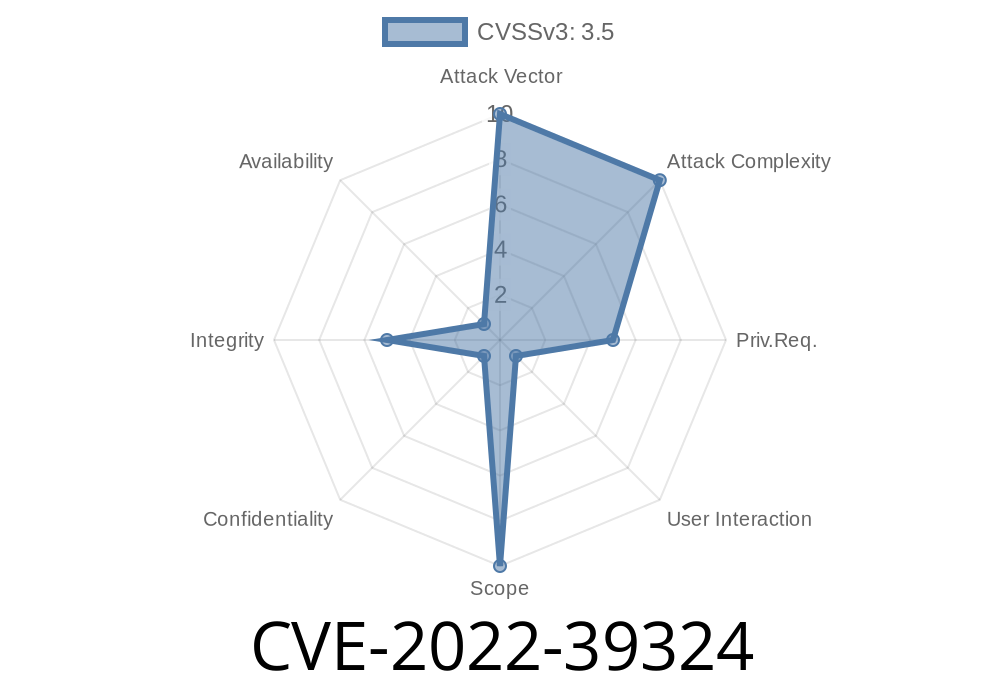
Grafana is an open-source platform for monitoring and observability, designed to create, explore, and share analytics-driven dashboards of your system's data. It allows users to create snapshots of the current state of their system. In versions prior to 8.5.16 and 9.2.8, there exists a vulnerability that allows a malicious user to create a snapshot with a modified originalUrl parameter, leading to URL redirection. Users are advised to upgrade to Grafana versions 8.5.16 or 9.2.8 to prevent this vulnerability from being exploited.
Code Snippet
The issue is caused by the ability of a user to edit the query associated with a snapshot. For instance:
{
"dashboard": { ... },
"originalUrl": "/api/dashboard/snapshot",
"query": {
"originalUrl": "https://malicious.site";
}
}
By changing the originalUrl parameter in the query, the attacker can then create a snapshot that does not point to the legitimate original dashboard but rather redirects to the injected URL.
Exploit Details
When another user opens the URL of the malicious snapshot, they are presented with the regular web interface delivered by the trusted Grafana server. However, the Open original dashboard button no longer points to the actual original dashboard but instead points to the attacker's injected URL. This effectively tricks the user into believing they are viewing the genuine dashboard and may make the user more susceptible to further phishing or social engineering attacks.
Links to Original References
[1] Grafana Website - https://grafana.com/
[2] Grafana GitHub Repository - https://github.com/grafana/grafana
[3] CVE-2022-39324 Entry at NIST National Vulnerability Database - https://nvd.nist.gov/vuln/detail/CVE-2022-39324
[4] Grafana Security Advisory for CVE-2022-39324 - https://grafana.com/security/advisories/2022-04/
Mitigation
Users of Grafana are encouraged to upgrade their systems to versions 8.5.16 or 9.2.8, as these releases contain the fix for the vulnerability. To further protect themselves, users should exercise caution when interacting with unknown or untrusted dashboard URLs and be vigilant against potential phishing or social engineering attempts.
Conclusion
CVE-2022-39324 is a vulnerability in Grafana that allows malicious users to exploit the snapshot feature by altering the originalUrl parameter, thus redirecting other users to potentially harmful websites. The vulnerability affects versions prior to 8.5.16 and 9.2.8, and users are advised to upgrade to these versions to mitigate the risk. By staying up to date and exercising caution when dealing with untrusted dashboard URLs, users can significantly reduce their exposure to this and similar vulnerabilities.
Timeline
Published on: 01/27/2023 23:15:00 UTC
Last modified on: 02/07/2023 20:17:00 UTC