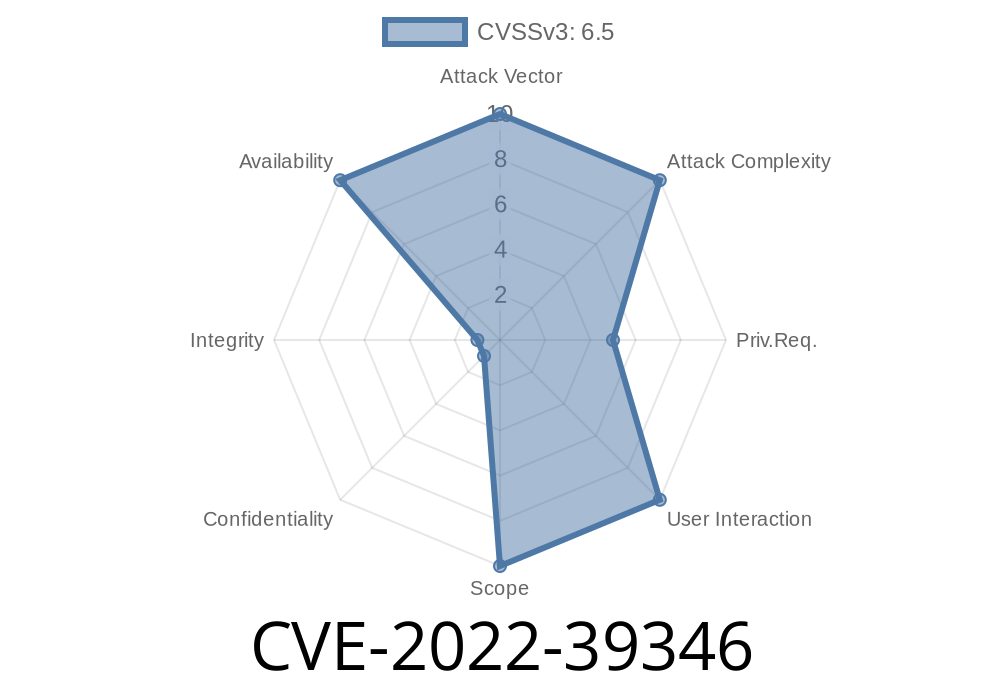
Nextcloud has become a popular open-source personal cloud server solution, trusted by millions to securely manage files, photos, and much more. But in late 2022, a significant vulnerability was discovered that could allow *any* registered user—even just a regular one—to bring your server to its knees. This bug is tracked officially as CVE-2022-39346.
Let’s break down what this vulnerability actually is, how it can be exploited, and what you should do to stay safe. We’ll even peek into what went wrong, with code snippets and all.
Before we dive into the bug, here’s a quick refresher
Nextcloud Server is an open-source cloud file hosting system that you can install on your own server. It rivals Dropbox or Google Drive, but you keep total control. With user accounts, groups, sharing, and a web interface—Nextcloud is a core part of many private and enterprise operations.
What Went Wrong?
The bug is simple at its heart. In Nextcloud, each user can set a display name that represents them throughout the app instead of just a username. The problem: Nextcloud didn’t properly restrict how long or big this display name could be.
This meant a user could set their display name to something extremely long—tens of thousands of characters, or more. When such an oversized display name is used (for example, viewed on the users’ page or shown in a notification), Nextcloud tries to handle and display it—*sending, storing, and rendering this huge string in the database and on web pages*.
Result: Ordinary users could easily overload Nextcloud’s database and web server, using up memory and CPU, ultimately crashing the service (Denial of Service).
Exploit Details: How an Attacker Can Crash Your Server
Let’s look at a demo of how a malicious user could exploit this vulnerability. The following example uses the user settings page or the API to set a crazy-long display name.
Step 1: Create a Gigantic Display Name
If you’re already logged in as a user, you can set your own display name via the user settings page or using the internal API.
Example using cURL (API)
# Replace USER and PASSWORD with your credentials
# Replace nextcloud.example.com with your server address
curl -u USER:PASSWORD \
-X PUT \
-d '{"displayname":"AAAAAAAA...(x100000 times)...AAAA"}' \
-H "Content-Type: application/json" \
https://nextcloud.example.com/ocs/v2.php/cloud/users/USER
*The "displayname" field here is filled with thousands and thousands of "A" characters.*
Or use the web UI
Just paste a huge string into the Display Name field on your profile page.
The server accepts the huge display name.
- Any page or API endpoint that needs to read or display your display name now must handle a gigantic string.
- For lists of users, notifications, collaboration features, and even sharing dialogs—the backend (and often the frontend browser) will lag or outright crash.
- Result: Every single page load or user operation that tries to interact with your profile can destabilize or bring down the server for everyone. If multiple malicious users perform this, the effect multiplies.
Sample Code Snippet: Insecure Input Validation
Here’s a simplified example of what the vulnerable code might have looked like (not the real Nextcloud source, but representative):
// ... Inside user update handler
$displayName = $_POST['display_name'];
// Vulnerable: no check on max length!
updateUserInDB($userId, $displayName);
A secure version *should* limit the length, for example
$displayName = $_POST['display_name'];
// Fix: restrict display name to 64 characters
if (mb_strlen($displayName) > 64) {
throw new Exception("Display name too long!");
}
updateUserInDB($userId, $displayName);
The fix is delightfully simple: *validate your inputs*, especially user-controllable text like names.
No Workarounds, Only Upgrades
According to Nextcloud’s official advisory:
> There are no known workarounds for this issue.
24..3 or higher
If you’re unable to upgrade, seriously consider disabling new user registrations and limiting access until you upgrade.
Reference Links
- CVE-2022-39346 on GitHub
- NIST National Vulnerability Database
- Nextcloud Server Repository
Conclusion
The CVE-2022-39346 bug shows how even simple things—like user display names—can seriously threaten web application safety when not handled right. If your Nextcloud is running an old version, upgrade it right now!
*If you run any app or platform, always validate incoming user input, especially for fields that seem harmless—attackers are always looking for the simplest way to bring your house down.*
Timeline
Published on: 11/25/2022 19:15:00 UTC
Last modified on: 12/13/2022 02:24:00 UTC