GLPI (Gestionnaire Libre de Parc Informatique) is a widely used free IT asset and service management software. It helps organizations keep track of computers, network devices, software licenses, and much more—all from a simple web interface. However, sometimes even great software can have security flaws. In 2022, a serious vulnerability—CVE-2022-39376—was discovered that put GLPI users at risk. In this article, we’ll explore what went wrong, how the exploit works, and what you should do to protect your systems.
What is CVE-2022-39376?
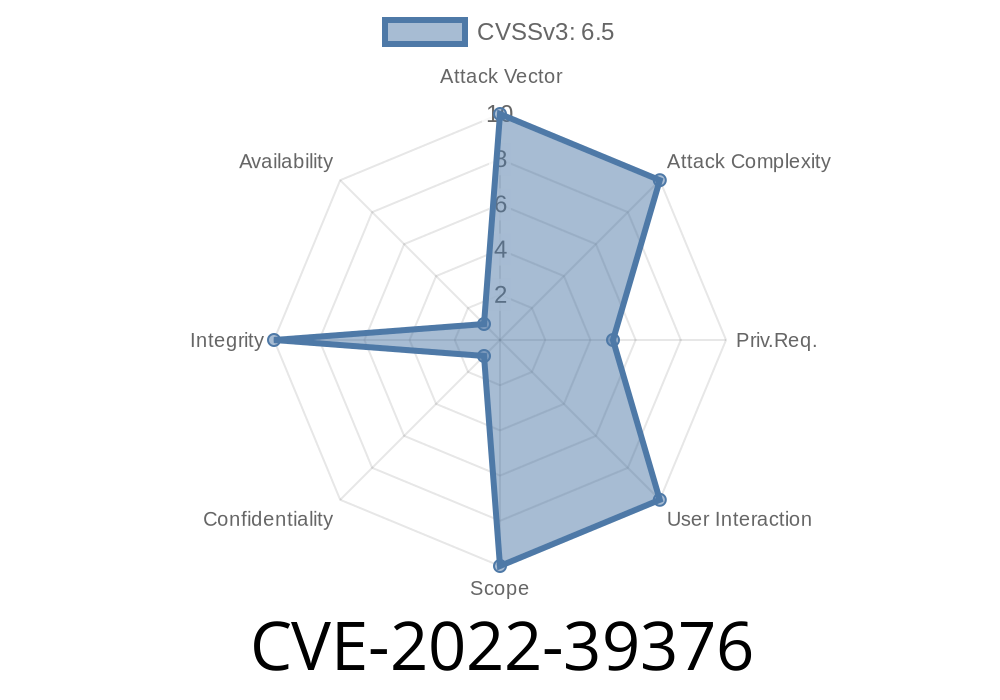
CVE-2022-39376 is a mail injection vulnerability present in GLPI before version 10..4. It allows attackers to manipulate “mailto” links by injecting malicious values through custom fields. This could trick users into sending malicious emails or expose them to phishing attacks.
Summary Table
| CVE | Software | Affected Versions | Patched Version | Exploit Type |
|-----|-----------|-------------------|-----------------|---------------------------|
| 2022-39376 | GLPI | < 10..4 | 10..4 | Mailto Link Injection/Phishing |
Let’s break it down
- GLPI allows users to enter values in *custom fields* for various assets (like computers, printers, tickets, etc).
- Those custom fields can later be used to generate dynamic links, such as *mailto* links for sending emails to asset owners or requesters.
- The vulnerable code didn’t properly escape or sanitize custom field values before adding them into HTML.
- An attacker could include special characters in a custom field value—such as Quotes, “?”, “&”, or even line breaks—which break out of the intended mailto link and allow the attacker to inject new parameters.
Suppose an asset’s custom field for “Responsible Person” email is set as
attacker@example.com?subject=Compromised&body=This+is+a+test
If GLPI uses this directly in a mailto link
<a href="mailto:attacker@example.com?subject=Compromised&body=This+is+a+test">Send Email</a>
That is already risky. But attackers could go further
attacker@example.com?body=NiceTry
CC=evil@example.com
Or use special characters to manipulate the mailto link and what happens when it’s clicked.
Exploit Details
Let’s see a step-by-step example—*for educational purposes only!*
Exploit Scenario
1. The attacker logs into GLPI (as a user or with limited access), creates a new asset or updates an existing asset’s custom field with a malicious value:
`
Here, %A represents a newline character, which may be interpreted differently by various email clients.
2. When an administrator or helpdesk clicks the “Send Email” button generated by GLPI, their email client opens with the attacker’s crafted address, and may include hidden “CC” or “BCC” fields, or even different body content.
3. This could trick the helpdesk into sending sensitive data or make phishing attempts easier, as the email gets sent to both the victim and the attacker.
Assuming you have access to a field like “Responsible Email”, enter this value
someone@example.com?subject=Fake%20Alert&body=Please%20approve%20this%20request.%ABCC:scammer@example.com
When the “mailto” link is generated, it can look like this in HTML
<a href="mailto:someone@example.com?subject=Fake%20Alert&body=Please%20approve%20this%20request.%ABCC:scammer@example.com">Contact</a>
When clicked, some mail clients can parse the BCC parameter and secretly email the scammer as well.
Conduct social engineering
Attackers don’t always need root access—abusing simple features sometimes leads to serious risks!
How to Stay Safe
The fix: The GLPI team patched this issue in version 10..4 by properly sanitizing the mailto link generation.
Upgrade immediately: Update GLPI to at least version 10..4.
- Monitor user inputs: Review who can edit custom fields, and limit untrusted access when possible.
References
- GLPI Security Advisory on GitHub
- GLPI 10..4 Release Notes
- NIST NVD Entry for CVE-2022-39376
Conclusion
CVE-2022-39376 reminds us that even trusted open source software like GLPI can harbor subtle, dangerous bugs. If your organization uses GLPI, update right away—don’t wait until someone discovers this the hard way! And remember, safe coding means always sanitizing what users can input, especially when building links or sending emails.
Timeline
Published on: 11/03/2022 16:15:00 UTC
Last modified on: 11/03/2022 19:11:00 UTC