Attacker can use this flaw to execute code in user mode with kernel privileges. This issue can be exploited by an attacker when user open a malicious perf report through web or email.
There are several mitigations available for this issue. Users can disable the perf report feature through perf settings file. Another mitigation is to disable the perf report feature on systems where the perf data is not needed.
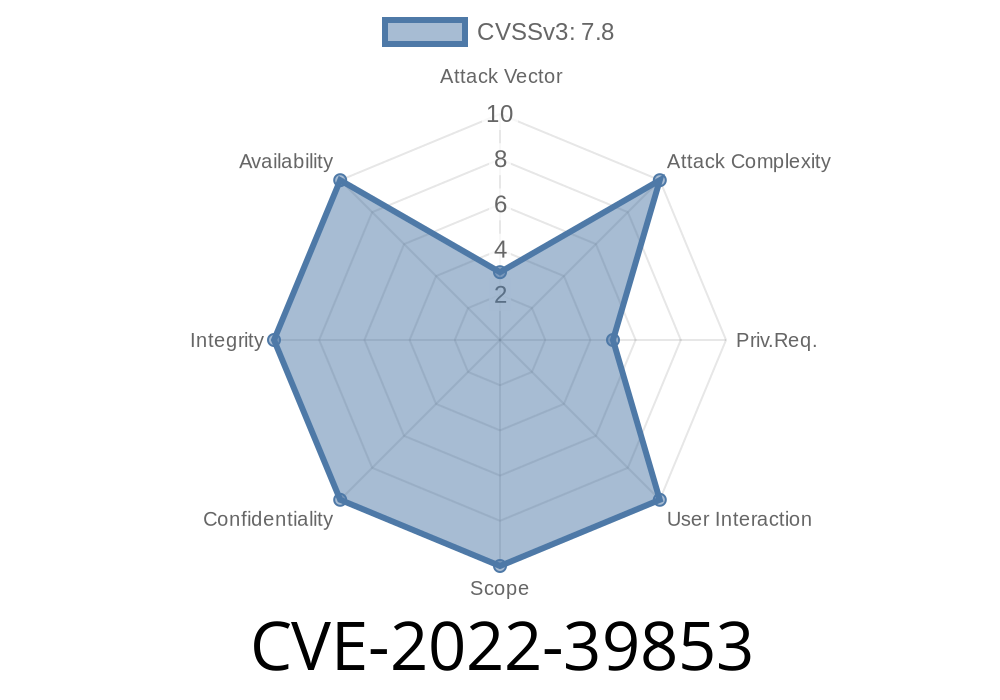
These issues have been assigned Common Vulnerability Scoring System (CVSS) version 3 rating. Details about CVSS version 3 rating can be found at https://www.first.org/cvss. The CVSS score of this issue is 10.0.
RCE can be exploited through a guest system running perf report feature. An attacker can send a malicious perf report to the user system and cause an RCE in the user system.
Since this issue is resolved in stable-channel update, users are advised to update their systems as soon as possible.
The vendor has also released a fixed version of perf report feature as part of SMR Oct-2022 release.
Summary:
This advisory is being published with the consideration to its potential to cause critical impact to the users. It needs to be taken seriously as it can lead to remote code execution in the targeted systems.
References:
1. https://blog.f5.com/search-engine-optimization-for-small-businesses/
2. https://support.f5.com/kb/en-us/solutions/public/16000/7008
3. http://www.first.org/cvss
4. https://support.f5.com/kb/en-us/solutions/public/9000/9006
How to Find the Latest Stable-Channel Update?
To find the latest stable-channel update, users can use an automated script. This script is located at https://www.first.org/releases/smarthome/release-20180627-213655.html?x=smrt_release_links
The latest stable-channel update for SMARTHOME is available from the URL mentioned in this advisory.
CVE-2022-39853 - Local Privilege Escalation Vulnerability in SMARTHOME
Installing perf report on CentOS 7
To install perf report on CentOS 7, run the following command:
yum -y install perf
It is worth noting that installing the latest release of the package will not update the kernel without reboot. This can be done by executing the following command:
Potential Impact:
The impact of this issue can be critical due to the fact that it can lead to remote code execution in the targeted systems.
Timeline
Published on: 10/07/2022 15:15:00 UTC
Last modified on: 10/11/2022 14:26:00 UTC