---
Introduction
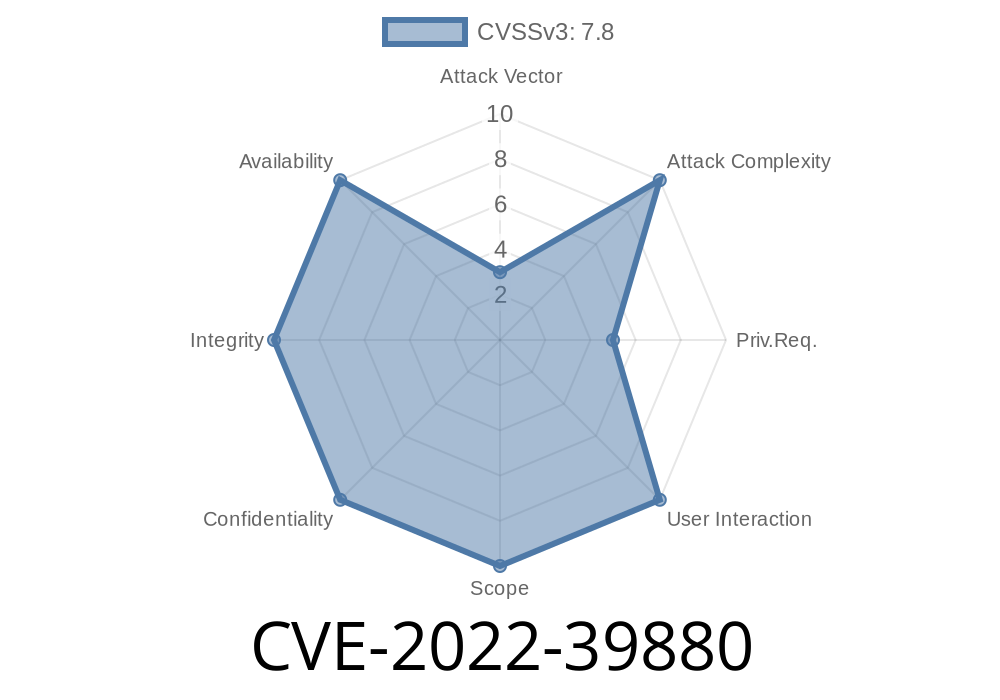
In the constant battle to protect user data and device security, every vulnerability counts. One such important vulnerability is CVE-2022-39880, found in Samsung's DualOutFocusViewer application. While the name might sound daunting, the issue boils down to a common weakness: improper input validation. This vulnerability affects certain Samsung devices prior to the SMR Nov-2022 Release 1, allowing a local attacker to run any code they want—potentially taking control over the device.
In this exclusive walkthrough, we’ll break down what went wrong, how it can be exploited, and what you can do to stay safe. We’ll link to the original sources for reference and show you some code examples to help you understand the risk.
What is DualOutFocusViewer?
Samsung’s DualOutFocusViewer is a system-level application that handles special image viewing modes (think: those fancy background blur effects in photos). Since it handles image data, it interacts with files and user inputs, making it a sensitive target.
About CVE-2022-39880
- CVE-ID: CVE-2022-39880
Type: Improper input validation
- Impact: Local privilege escalation / arbitrary code execution
- Original Advisory: Samsung Mobile Security - SVE-2022-26560
Vulnerability Details
Improper input validation means the app doesn’t properly check the data it’s given. If a local attacker feeds it bad input, the app might do something dangerous, like running code that the attacker supplied.
Example Scenario
Imagine the app reads an image file from the device’s storage, but fails to check exactly what’s in the file. If the app loads and executes content based on data inside the image (like a script or code), a hacker could trick the app into running malicious code disguised as an image.
Suppose the app contains code like this (simplified for illustration)
// BAD: Loads content from untrusted file path
String filePath = intent.getStringExtra("image_path");
if (filePath != null) {
processImage(new FileInputStream(filePath));
}
Here, the path comes from user input. There’s no check to see if the file really is a safe image, or if it contains dangerous payloads. This opens the door for a local app or user to point to a crafted file.
A safer approach would look like this
// GOOD: Validate input, restrict to app's directory, check file type
String filePath = intent.getStringExtra("image_path");
if (filePath != null && filePath.startsWith(context.getFilesDir().getPath())) {
if (isSafeImageFile(filePath)) {
processImage(new FileInputStream(filePath));
}
}
Where isSafeImageFile checks file signatures (magic numbers) and extensions.
Trick the App to Open the File
By abusing permissions or another vulnerability (like another app or script on the device), the attacker tricks DualOutFocusViewer into opening this file.
Achieve Code Execution
When DualOutFocusViewer processes the file, the embedded code executes with the app’s permissions. If the app has high privileges, this could lead to full device compromise.
Proof-of-Concept (Simplified Pseudocode)
# Simulate a malicious image payload
with open("exploit.dof", "wb") as f:
f.write(b"FAKEMAGIC") # Fake file header
f.write(b"\x90" * 100) # NOP sled
f.write(b"\xcc" * 20) # Malicious shellcode in real-world example
Then, leverage an IPC mechanism or a script to pass this file to the vulnerable app.
Original References
- Samsung Security Bulletin: November 2022
- CVE-2022-39880 - MITRE Database
> *Vulnerability was disclosed as SVE-2022-26560 and patched in SMR Nov-2022 Release 1. All users should upgrade as soon as possible.*
Conclusion
CVE-2022-39880 is a powerful reminder that even simple input validation mistakes can give attackers a way into your device. If you’re a user, always keep your device updated. If you’re a developer, always check and validate everything that comes from the user—even filenames and image data.
Share this post to help others stay informed! If you want more deep dives like this, let us know in the comments.
Timeline
Published on: 11/09/2022 22:15:00 UTC
Last modified on: 11/10/2022 15:17:00 UTC