If you’re running a WordPress site with forums powered by the Simple:Press plugin, there’s an important vulnerability you need to know about. CVE-2022-4027 reveals how attackers could inject dangerous scripts into your forum posts and put your community at risk. Let’s break down how this stored cross-site scripting (XSS) flaw works, walk you through some code, show how an attacker might exploit it, and give you all the sources you’ll need to stay safe.
What is CVE-2022-4027?
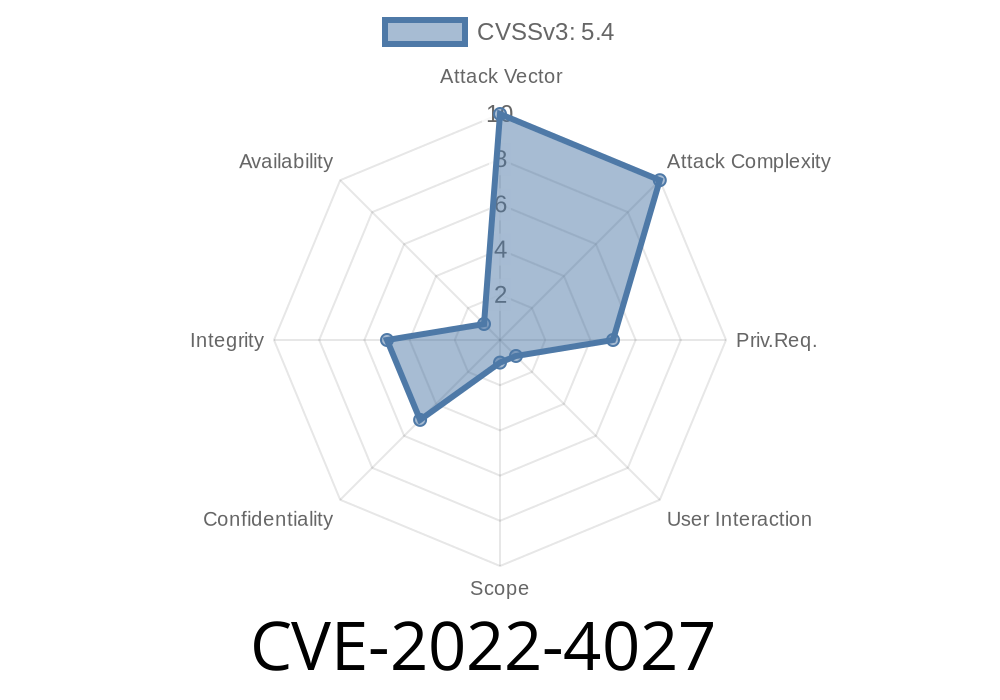
- CVE ID: CVE-2022-4027
- Vulnerable Plugin: Simple:Press (up to and including version 6.8)
Attack Vector: Unauthenticated user through forum responses using the postitem parameter
- Impact: Arbitrary JavaScript/HTML code can be injected using <object> or <embed> tags
How Does The Vulnerability Work?
When a user responds to a forum thread in Simple:Press, whatever content they submit in the response (the postitem parameter) is displayed to other users. The plugin failed to sanitize and escape this user input properly ― especially dangerous HTML tags like <object> and <embed>. This lack of filtering makes it easy for attackers to sneak in malicious code.
Key point:
*No authentication is needed ― anyone could inject malicious scripts that will run for every visitor who views the affected thread!*
Within the forum's reply function, the attacker submits the following "reply" as the forum post body
<object data="javascript:alert('XSS! Exploit by CVE-2022-4027')" type="text/html"></object>
Or with <embed>
<embed src="javascript:alert('XSS by CVE-2022-4027')" />
The code gets stored in the WordPress database as part of the reply.
- When any forum user (including admins or moderators) visits the forum thread, the HTML is rendered and the JavaScript executes, displaying a pop-up alert.
In a real-world scenario?
The script could steal cookies, hijack sessions, or load more dangerous malware.
Code Snippet: Vulnerable Code Example
The core of the vulnerability lies in missing or poor use of sanitize_text_field(), wp_kses(), or similar functions on submitted post data.
Simplified vulnerable PHP
// Vulnerable: No sanitization!
function sp_submit_forum_post() {
$post_content = $_POST['postitem'];
// Code to insert the comment into the database...
// $post_content is output with NO escaping:
echo $post_content;
}
A safe version would be
// Patched: Sanitize and escape!
function sp_submit_forum_post() {
$allowed_tags = array(
'a' => array('href' => array(), 'title' => array()),
'b' => array(),
'i' => array(),
// No <object> or <embed> allowed!
);
$post_content = wp_kses($_POST['postitem'], $allowed_tags);
echo esc_html($post_content);
}
`html
Submit your response.
4. When anyone, including administrators, visits that forum page and loads the malicious post, the browser executes your injected code.
Update Simple:Press immediately to the latest version (greater than 6.8).
2. If you’re customizing output, always escape and sanitize all user-supplied data using WordPress functions like esc_html(), sanitize_text_field(), and especially wp_kses() to whitelist safe tags.
References & Further Reading
- NVD Details: CVE-2022-4027
- WPScan Advisory
- Simple:Press Changelog
- WordPress Plugin Developer Handbook
Last Words
CVE-2022-4027 is a clear reminder: forums and comment fields need bulletproof sanitization. If you use Simple:Press, make sure you’re patched. Even if you don’t, review your handling of HTML posts—XSS is one of the oldest and deadliest web attacks.
Timeline
Published on: 11/29/2022 21:15:00 UTC
Last modified on: 12/01/2022 19:57:00 UTC