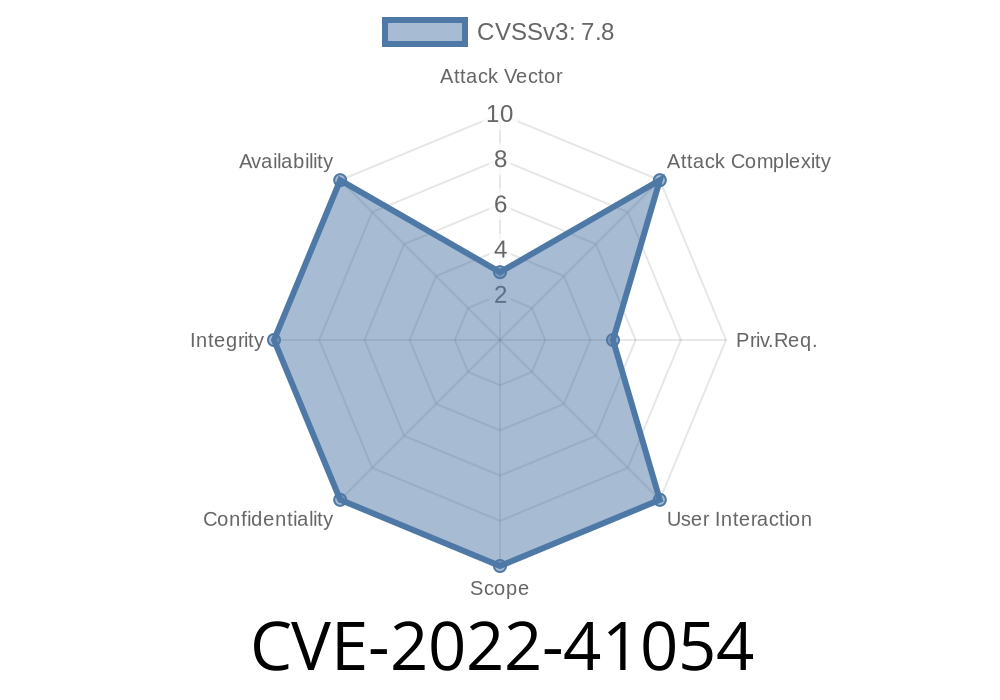
In November 2022, Microsoft patched a newly discovered vulnerability affecting its Resilient File System (ReFS) on Windows. Named CVE-2022-41054, this flaw allows local attackers to gain elevated privileges, potentially turning basic user access into full system control. In this deep dive, we’ll unpack what makes this bug tick, review some code patterns related to it, and explain how attackers can take advantage of the vulnerability.
*Original advisory:*
Microsoft Security Response Center - CVE-2022-41054
What is Windows Resilient File System (ReFS)?
Launched with Windows Server 2012, ReFS is Microsoft’s next-gen file system focusing on reliability and data integrity. While NTFS is still the default for most Windows installations, ReFS gets used in enterprise environments and data centers due to features like auto-healing, virtualization, and protection against data corruption.
Technical Description
CVE-2022-41054 is an elevation of privilege (EoP) vulnerability. Here’s how Microsoft describes it:
> _“An elevation of privilege vulnerability exists in Windows Resilient File System (ReFS) due to improper handling of objects in memory.”_
Translation: an unprivileged attacker with local access can trigger the bug to gain higher privileges—often SYSTEM—by exploiting the way ReFS handles certain operations.
How Does This Bug Work? The Exploit Path
Attackers exploiting CVE-2022-41054 typically leverage Windows ReFS volume handling and manipulation. The vulnerability arises due to insecure memory operations (think buffers and pointers) within the ReFS driver. A maliciously crafted request or file operation can force ReFS to mismanage memory—typically leading to privilege escalation.
Attacker gains basic user (or a less privileged process) access.
2. Crafts a special ReFS volume or file, or performs malicious I/O operations.
Exploits the driver to execute code as SYSTEM—essentially getting full control.
_This is not a “drive-by” attack. You must have some level of access to the system already. Think: malware on a local user account, or code run within a restricted sandbox._
Where’s the Code?
Since this is a kernel-level bug in a proprietary file system driver (ReFS.sys), there’s no open source code to point at directly. However, public exploit developers and security researchers often use open handles to communicate with the driver.
Here’s a simplified example of what an attacker might try, using pseudo code in C to open a ReFS volume and send a custom IOCTL request:
#include <Windows.h>
#include <winioctl.h>
#include <stdio.h>
// Special IOCTL used for ReFS - placeholder value, real researcher finds correct code
#define IOCTL_REFS_SPECIAL x90062037
int main() {
HANDLE hVolume = CreateFileW(
L"\\\\.\\E:", // Target ReFS volume
GENERIC_READ | GENERIC_WRITE,
FILE_SHARE_READ | FILE_SHARE_WRITE,
NULL,
OPEN_EXISTING,
,
NULL);
if (hVolume == INVALID_HANDLE_VALUE) {
printf("Failed to open ReFS volume\n");
return 1;
}
BYTE inBuffer[512] = { /* crafted malicious input here */ };
DWORD returned;
BOOL ok = DeviceIoControl(
hVolume,
IOCTL_REFS_SPECIAL, // Vulnerable code path
inBuffer,
sizeof(inBuffer),
NULL,
,
&returned,
NULL);
if (!ok) {
printf("DeviceIoControl failed: %lu\n", GetLastError());
} else {
printf("Potential exploit sent.\n");
}
CloseHandle(hVolume);
return ;
}
Note: In real exploits, the details of the IOCTL code and craft data would be discovered and weaponized against the specific vulnerable driver version.
Conceptual Attack Steps
1. Mount (or access) a ReFS volume—either physical or virtual/hard drive.
Smuggle data that causes the ReFS.sys driver to mishandle memory.
4. Escalate privileges using arbitrary code execution, typically through kernel callback functions or by overwriting privileged tokens.
For more technical details, see
- Google Project Zero - Windows Kernel Exploitation
- HackerOne Research on Windows IOCTL Bugs
Why Is This Dangerous?
- Local privilege escalation means any bug in your antivirus, browser, or third-party software that allows a write to disk could get chained with CVE-2022-41054 for full takeover.
Attackers only need standard user access—no need for admin rights up front.
- Servers and storage nodes using ReFS are particularly juicy targets because they often hold sensitive files and data.
Update Windows Immediately: Microsoft released patches for this issue in November 2022.
Windows Updates and Patch Details
- Monitor privileged access and file systems: Watch for signs of abnormal ReFS volume mounting or IOCTL activity.
- Limit access: Don't give users or apps unnecessary permissions to mount or manage filesystems—especially on servers.
Conclusion
CVE-2022-41054 reminds us: even advanced file systems can have old-school privilege escalation bugs. While exploitation requires local access, chaining this vulnerability with other software flaws can give attackers the keys to the kingdom—especially on critical storage infrastructure.
For more info:
Microsoft Security Update Guide – CVE-2022-41054
*Stay patched. Stay safe. Defend your data, one update at a time.*
Timeline
Published on: 11/09/2022 22:15:00 UTC
Last modified on: 11/15/2022 16:18:00 UTC