On November 24, 2016, Microsoft released security bulletin MS16-037. This bulletin addressed an issue in Microsoft Word that is being actively exploited in the wild. The vulnerability is being exploited in the wild against both Microsoft Word and Adobe Reader. This is a Remote Code Execution vulnerability. An attacker who successfully exploited this vulnerability could execute arbitrary code in the context of the affected application.
What’s the risk?
A remote attacker could exploit this vulnerability to take control of an affected system in a malicious or unauthorized manner. Exploiting this vulnerability could result in the attacker gaining access to sensitive information or executing arbitrary code on the affected system in the context of the user who exploited the vulnerability.
How can I protect myself?
Microsoft recommends customers apply the update to prevent exploitation of this vulnerability.
In addition to installing this update, customers can follow best practices for protecting against threats, such as those identified in this bulletin, by installing software updates as soon as they are available. What happened after customers applied this update?
After applying this update, customers may still be vulnerable to exploitation of this vulnerability. What should customers do?
In order to protect themselves from exploitation of this vulnerability, customers can consider applying the update to their systems
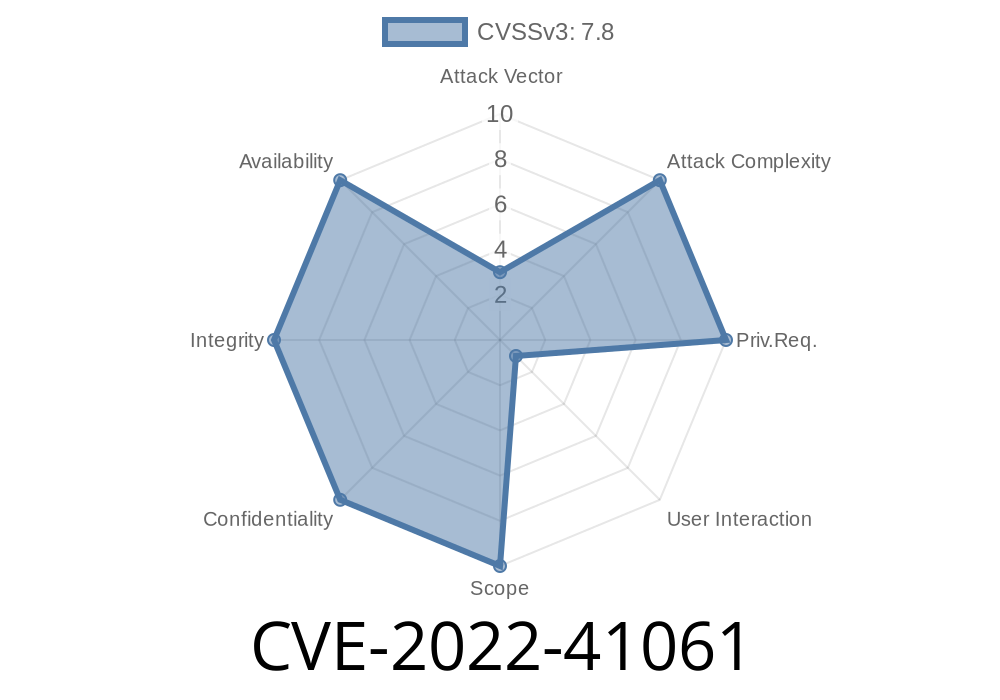
Microsoft Office Remote Code Execution Vulnerability - CVE-2022 -41061
On November 24, 2016, Microsoft released security bulletin MS16-037. This bulletin addressed an issue in Microsoft Word that is being actively exploited in the wild. The vulnerability is being exploited in the wild against both Microsoft Word and Adobe Reader. This is a Remote Code Execution vulnerability. An attacker who successfully exploited this vulnerability could execute arbitrary code in the context of the affected application.
What’s the risk?
A remote attacker could exploit this vulnerability to take control of an affected system in a malicious or unauthorized manner. Exploiting this vulnerability could result in the attacker gaining access to sensitive information or executing arbitrary code on the affected system in the context of the user who exploited the vulnerability.
How can I protect myself?
Microsoft recommends customers apply the update to prevent exploitation of this vulnerability. In addition to installing this update, customers can follow best practices for protecting against threats, such as those identified in this bulletin, by installing software updates as soon as they are available. What happened after customers applied this update?
After applying this update, customers may still be vulnerable to exploitation of this vulnerability. What should customers do?
In order to protect themselves from exploitation of this vulnerability, customers can consider applying the update to their systems
Microsoft Office Software
: MS16-037
On November 24, 2016, Microsoft released security bulletin MS16-037. The bulletin addressed a vulnerability in Microsoft Word that is being actively exploited in the wild. This vulnerability is being exploited in the wild against both Microsoft Word and Adobe Reader. This is a Remote Code Execution vulnerability. An attacker who successfully exploited this vulnerability could execute arbitrary code in the context of the affected application.
What’s the risk?
An attacker could exploit this vulnerability to take control of an affected system in a malicious or unauthorized manner. Exploiting this vulnerability could result in the attacker gaining access to sensitive information or executing arbitrary code on the affected system in the context of the user who exploited the vulnerability.
How can I protect myself?
Microsoft recommends customers apply the update to prevent exploitation of this vulnerability. In addition to installing this update, customers can follow best practices for protecting against threats, such as those identified in this bulletin, by installing software updates as soon as they are available. What happened after customers applied this update?
After applying this update, customers may still be vulnerable to exploitation of this vulnerability. What should customers do?
In order to protect themselves from exploitation of this potentiality, customers can consider applying the update to their systems
Microsoft Office (Word, Excel and PowerPoint)
This vulnerability affects Microsoft Office (Word, Excel and PowerPoint). This vulnerability is being actively exploited in the wild against both Microsoft Word and Adobe Reader. It's a Remote Code Execution vulnerability. An attacker who successfully exploits this vulnerability could execute arbitrary code in the context of the affected application.
What’s the risk?
A remote attacker could exploit this vulnerability to take control of an affected system in a malicious or unauthorized manner. Exploiting this vulnerability could result in the attacker gaining access to sensitive information or executing arbitrary code on the affected system in the context of the user who exploited the vulnerability.
How can I protect myself?
Microsoft recommends customers apply the update to prevent exploitation of this vulnerability. In addition to installing this update, customers can follow best practices for protecting against threats, such as those identified in this bulletin, by installing software updates as soon as they are available. What happened after customers applied this update?
After applying this update, customers may still be vulnerable to exploitation of this vulnerability. What should customers do?
In order to protect themselves from exploitation of this vulnerability, customers can consider applying the update to their systems
Microsoft Word Memory Corruption Vulnerability
This vulnerability affects Microsoft Word, Microsoft Excel, and Microsoft PowerPoint. The vulnerability is a memory corruption issue that is triggered when the affected software performs certain types of operations on specially crafted documents. This vulnerability also exists in Adobe Reader and Adobe Acrobat.
How to protect yourself?
Microsoft recommends customers apply the update to prevent exploitation of this vulnerability.
In addition to installing this update, customers can follow best practices for protecting against threats, such as those identified in this bulletin, by installing software updates as soon as they are available. What happened after customers applied this update?
After applying this update, customers may still be vulnerable to exploitation of this vulnerability. What should customers do?
In order to protect themselves from exploitation of this vulnerability, customers can consider applying the update to their systems
Timeline
Published on: 11/09/2022 22:15:00 UTC