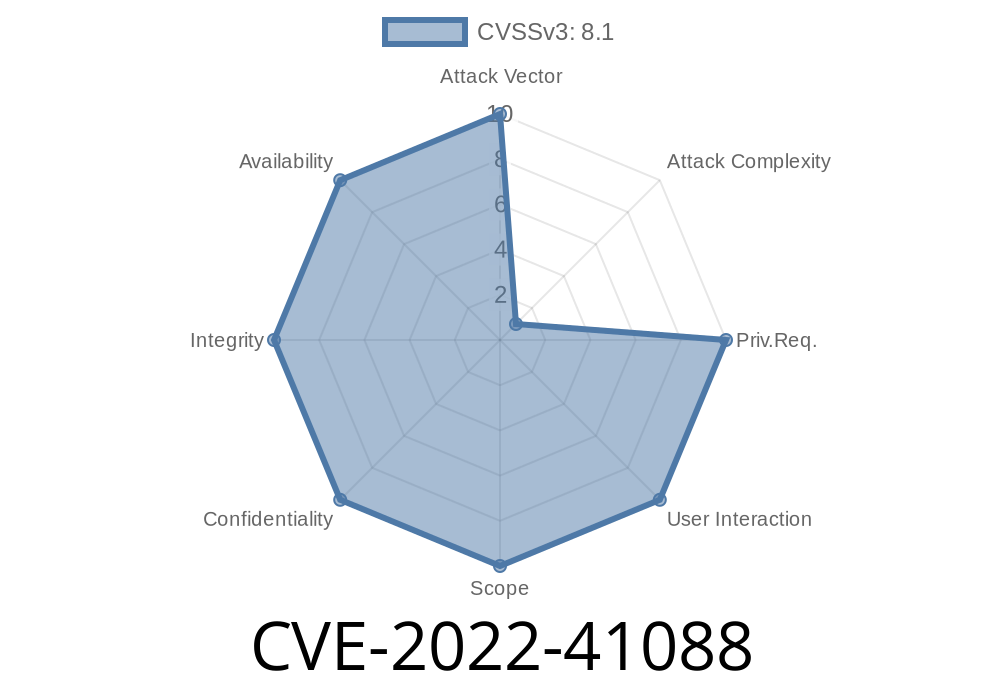
In the constant cat-and-mouse game of cybersecurity, new vulnerabilities surface all the time. One such critical vulnerability is CVE-2022-41088, a remote code execution (RCE) flaw in the Windows Point-to-Point Tunneling Protocol (PPTP). While vulnerabilities in PPTP aren't new, what makes this flaw particularly concerning is its potential impact and the fact that it is unique compared to other 2022 PPTP flaws like CVE-2022-41039 and CVE-2022-41044.
This post will break down CVE-2022-41088 in plain American English, explain how it can be exploited by attackers, walk you through a typical attack scenario, and arm you with concrete mitigation steps.
What Is CVE-2022-41088?
On November 8, 2022, Microsoft addressed CVE-2022-41088. This flaw lets attackers run malicious code remotely on vulnerable Windows devices using PPTP, a legacy VPN protocol still supported for compatibility in several Windows editions.
The vulnerability exists because of how Windows PPTP server handles certain crafted packets. An unauthenticated attacker can send special requests to a victim server, potentially allowing them to execute arbitrary code with SYSTEM privileges.
Official Microsoft advisory:
Microsoft Security Update Guide: CVE-2022-41088
How Does the Exploit Work?
PPTP uses GRE (Generic Routing Encapsulation) and the TCP port 1723 to establish a connection. Microsoft patched CVE-2022-41088 after discovering the way the service processes malformed PPTP control messages can corrupt memory, paving the way for code execution.
Key characteristics
* No authentication required.
* Entirely remote.
* Targets systems exposing PPTP services on the internet.
Discover Vulnerable Servers:
The attacker scans the internet for systems with TCP port 1723 open—this indicates PPTP is running.
Send Malicious Packet:
By crafting a specially malformed PPTP control message, they exploit the flaw. This is often done using a script/program to target the service.
Here’s an annotated sample Python pseudocode demonstrating malicious packet sending using scapy
from scapy.all import *
import socket
# Target details
target_ip = "192.168.1.100"
pptp_port = 1723
# Create a malformed PPTP packet (the exploit details are not disclosed for ethics)
malformed_pkt = b'\x00\x00\x00\xff' # placeholder for actual malicious payload
# Establish TCP connection and send the packet
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((target_ip, pptp_port))
sock.sendall(malformed_pkt)
sock.close()
print("[+] Malicious PPTP control packet sent")
> Note: This PoC doesn’t real exploit the issue, but illustrates the basic process. Real exploitation requires exact knowledge of the vulnerable part of the protocol, often protected by NDAs or responsible disclosure until fixes are widespread.
Why It's Different from CVE-2022-41039 and CVE-2022-41044
While all three affect PPTP, each CVE relates to unique bugs or weaknesses in how PPTP control/data messages are processed by Windows.
- CVE-2022-41039 and CVE-2022-41044 address other bugs in related PPTP code paths, but the conditions required and exploit methods vary.
- CVE-2022-41088's uniqueness lies in *how* the memory corruption is triggered and the specific malformed PPTP packet sequence used.
> For detailed technical comparison:
> * CVE-2022-41039 advisory
> * CVE-2022-41044 advisory
Apply Microsoft Updates:
Patch immediately: November 2022 Security Update
Restrict Access:
Block TCP 1723 and GRE (protocol 47) at your firewall unless absolutely needed, and only allow trusted IPs.
More Resources
- Microsoft Security Advisory: CVE-2022-41088
- PPTP Protocol Reference (Microsoft)
Final Thoughts
Remote code execution bugs in legacy protocols like PPTP are dangerous because they’re often overlooked and exposed on the public internet by accident or inertia. If your organization uses PPTP or you’re responsible for Windows network security, act fast. Patch, monitor, and retire PPTP where possible.
CVE-2022-41088 is a wake-up call: Legacy technology is more risk than convenience.
*Stay safe, and remember—patch early, patch often!*
Timeline
Published on: 11/09/2022 22:15:00 UTC
Last modified on: 11/10/2022 00:33:00 UTC