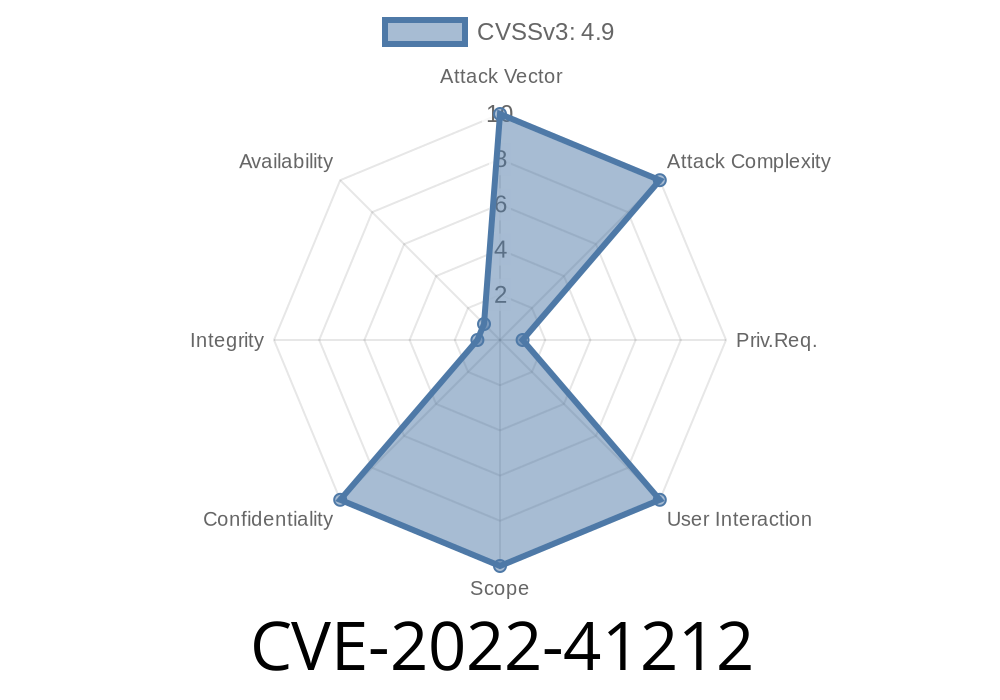
Due to insufficient input validation, SAP NetWeaver Application Server allows an attacker with high level privileges to use a remote enabled function to read an otherwise restricted file. On successful exploitation an attacker can access and modify the file contents, which may lead to a complete compromise of the confidentiality of the application. Due to insufficient input validation, SAP NetWeaver Application Server allows an attacker with high level privileges to use a remote enabled function to read an otherwise restricted file. On successful exploitation an attacker can access and modify the file contents, which may lead to a complete compromise of the confidentiality of the application. Due to insufficient input validation, SAP NetWeaver Application Server allows an attacker with high level privileges to use a remote enabled function to read an otherwise restricted file. On successful exploitation an attacker can access and modify the file contents, which may lead to a complete compromise of the confidentiality of the application. Due to insufficient input validation, SAP NetWeaver Application Server allows an attacker with high level privileges to use a remote enabled function to read an otherwise restricted file. On successful exploitation an attacker can access and modify the file contents, which may lead to a complete compromise of the confidentiality of the application.
Vulnerability overview
The SAP NetWeaver Application Server provides a remote enabled function in the "sap_stored_session" module. The "sap_stored_session" module is responsible for storing information about user session and commands issued by the user.
A vulnerability in the SAP NetWeaver Application Server allows an attacker to exploit this service and use it to read data that should be restricted. This may lead to a compromise of confidentiality of the application.
Limitations of CVE-2022-41212
CVE-2022-41212 does not allow for a complete compromise of the confidentiality of the application. It can only be used to read unsecured data from the files, which is not confidential and can be drawn from a different source.
There is no known mitigation or protection against CVE-2022-41212
Overview of SAP NetWeaver Application Server
SAP is a multinational software company that provides enterprise application software and technology solutions. SAP was founded in 1972, with headquarters in Walldorf, Germany. The company is listed on the Frankfurt Stock Exchange (DE0005468503) and is a component stock of the Dow Jones Industrial Average as well as one of the world's most widely held stocks.
NetWeaver Application Server is included in the SAP NetWeaver Enterprise Profitability Suite, which provides an integrated platform for developing, running, and managing business-critical applications. It offers both Java-based and .NET-based options for access to data, integration with external systems, and scalability.
The bug allows an attacker to read restricted files by exploiting a remote enabled function without any authentication or authorization required from a server that has been configured as part of the application security.
Timeline
Published on: 11/08/2022 22:15:00 UTC
Last modified on: 11/09/2022 15:41:00 UTC