Table of Contents
What is CVE-2022-41215?
CVE-2022-41215 is a critical security flaw discovered in SAP NetWeaver ABAP Server and ABAP Platform, one of the most widely used business application platforms in the world. This vulnerability lets an unauthenticated attacker redirect SAP users to any website, including malicious pages, just by tricking them to click a crafted link. This can happen because the SAP software does not properly check user-supplied URLs.
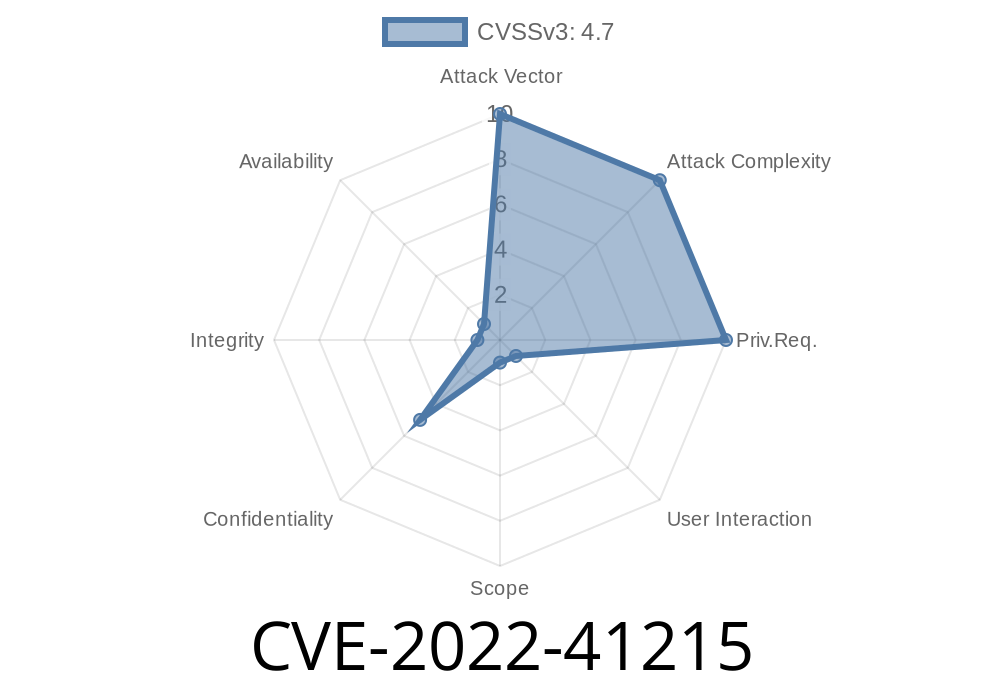
Severity: High
- SAP Security Note: 3242933
- CVSS Score: 8.1 (High) [[NIST NVD reference]](https://nvd.nist.gov/vuln/detail/CVE-2022-41215)
How the Vulnerability Works
Normally, SAP applications allow redirection after successful login or logoff. For example, after you enter your credentials, you might be redirected to your default page. The page might use a URL parameter like redirectURL to know where you need to go.
However, prior to SAP's patch, the server did not sufficiently validate the redirectURL parameter. This meant you could create a link that points to an external, malicious site, and SAP would happily forward users there.
A generic endpoint example would look like
https://sap.example.com/sap/bc/ui5_ui5/someapp/index.html?redirectURL=https://evil.com
A normal, well-configured app would see the redirect is going outside its domain and would block it. SAP, in this vulnerable version, did not.
The attacker simply sends an email or message like:
> "Dear employee, for urgent security update, log in here."
Once the user authenticates, they're sent straight to the attacker's page.
Malicious SAP login link
https://sap.example.com/sap/bc/ui5_ui5/someapp/index.html?redirectURL=https://evil.com
What the SAP backend did (over-simplified)
* ABAP pseudo-code
PARAMETERS: p_redirect TYPE string.
START-OF-SELECTION.
IF p_redirect IS SUPPLIED.
" BAD: No proper domain check!
SET HTTP-HEADER 'Location' VALUE p_redirect.
SEND HTTP RESPONSE WITH STATUS 302.
EXIT.
ENDIF.
END-OF-SELECTION.
Proper Validation (How it should be)
* Only allow our own domain!
IF p_redirect CP 'https://sap.example.com/*';.
SET HTTP-HEADER 'Location' VALUE p_redirect.
SEND HTTP RESPONSE WITH STATUS 302.
ELSE.
" Invalid redirect, fallback to safe local page
SET HTTP-HEADER 'Location' VALUE '/home'.
SEND HTTP RESPONSE WITH STATUS 302.
ENDIF.
Why is This Dangerous?
Open redirects are frequently abused in phishing and credential-theft attacks. SAP is often used by large organizations, making it an attractive target. Attackers can:
Chain with other vulnerabilities for deeper intrusions.
There is NO user warning – everything appears SAP-official until the moment of redirection.
Mitigation Steps
If you run SAP NetWeaver ABAP, patch immediately!
Apply SAP Note 3242933
SAP Security Patch Day – November 2022
References
- SAP Security Note 3242933 (requires SAP login)
- NIST CVE-2022-41215 entry
- SAP Patch Day (Nov 2022) Blog
- OWASP: Open Redirects and Forwards
In Closing
CVE-2022-41215 lets attackers exploit weak URL checks in SAP NetWeaver to redirect users to any website. If you use SAP, patch now and stay alert—such small web bugs can cause big business risks.
Timeline
Published on: 11/08/2022 22:15:00 UTC
Last modified on: 03/01/2023 15:36:00 UTC