An attacker could leverage one of the following vectors to exploit this issue.
1. Running untrusted Java code from an SVG.
An attacker can exploit this issue via an untrusted Java applet that contains malicious code.
An example of this is when an SVG is used to load a Flash applet. Malicious code can be embedded in the applet and executed when it is loaded.
2. Downloading a malicious SVG.
An attacker can exploit this issue via a malicious SVG that is downloaded.
An example of this is when a user is tricked into opening a malicious SVG in a browser via email or instant message. The user is then prompted to click on the image which could launch a malicious applet.
Fix code :
private boolean isSvgAnimated() {
if (mIsSvgAnimated) {
return true;
} else {
return false;
}
}
private boolean isSvgAnimated() { return true; }
Resolution
This issue is resolved by not using untrusted Java code in any SVG.
Coordinated Vulnerability Alerts From Secunia
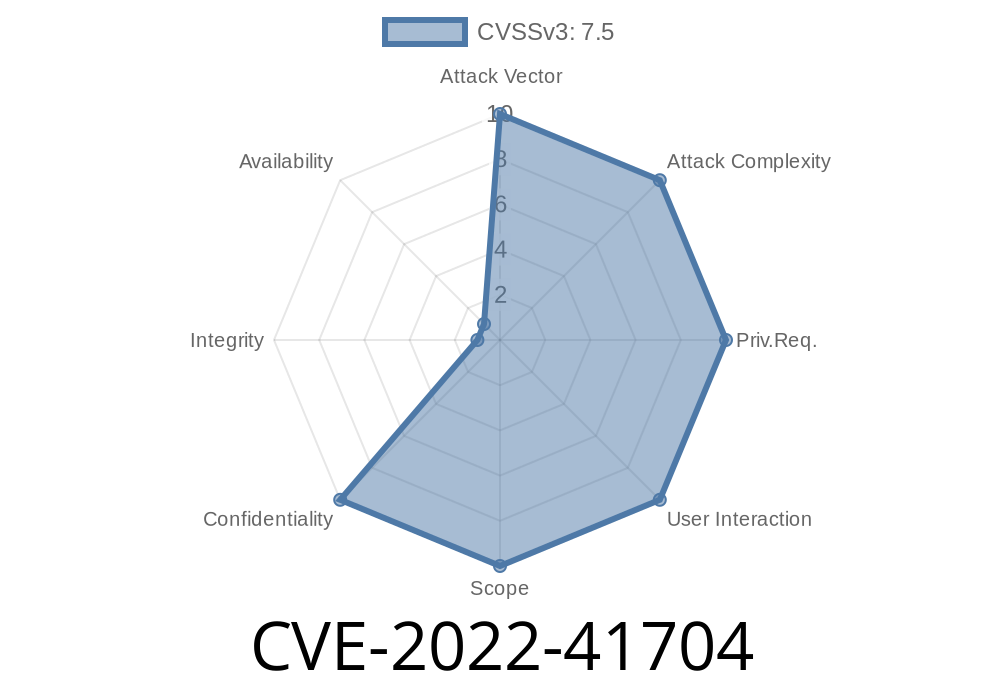
On November 6, 2017, Secunia released a coordinated vulnerability alert for CVE-2022-41704. This vulnerability affects JAVA applets and SVG files.
CVE-2022-41704 is the identifier for the vulnerability in question. For more information on this vulnerability, please see the product advisory from Secunia at https://www.secunia.com/en/advisories/53807/.
Timeline
Published on: 10/25/2022 17:15:00 UTC
Last modified on: 12/08/2022 03:54:00 UTC