An attacker can inject script into the feed via input field, resulting in a cross-site scripting vulnerability. BlueSpiceFoundation is an open source desktop collaboration software. BlueSpiceFoundation extension is enabled by default in BlueSpice server. An attacker needs to get user to visit a malicious wikipage on BlueSpice server. Attackers can use social engineering to persuade users to click malicious links. Attackers can also leverage default installation or user account activities to exploit this vulnerability. The following are some examples of social engineeringend user to click malicious link in an email, user to click on malicious link in BlueStack forum, user to click on malicious link in BlueStack social media profile. End users should be careful while clicking links they receive in email or other mediums.
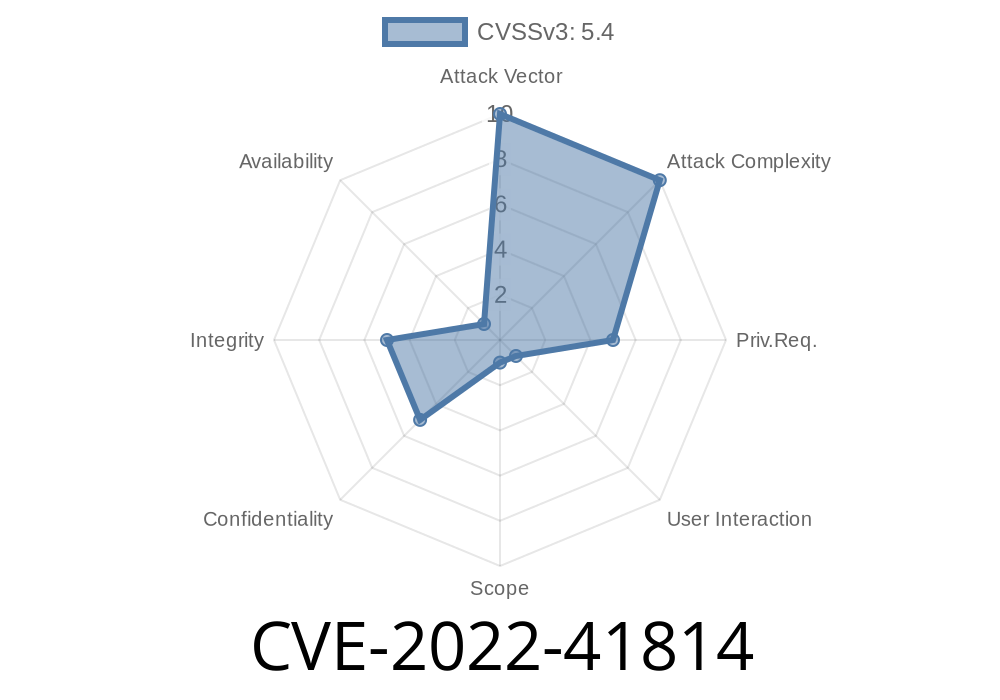
Vulnerability details
Cross-site scripting vulnerability is present in extension, which may allow an attacker to send a malicious script to end users.
An attacker can send a malicious script to end users via input field.
Potential benefits of this BlueSpiceFoundation vulnerability
This vulnerability can result in the following benefits to an attacker:
- Can identify and exploit vulnerable computers that are running BlueSpiceFoundation
- Can get admin privileges to a remote computer running BlueSpiceFoundation
- Can use this vulnerability to attack other systems on the network, to exfiltrate data and gain access to confidential data
- This vulnerability is only exploitable by an authorized user. The attacker needs both local and remote login rights.
Timeline
Published on: 11/15/2022 15:15:00 UTC
Last modified on: 11/16/2022 19:42:00 UTC