On the Android mobile operating system, Element supports Android 4.1 or later. On Android, Element is accessed through the Google Play Store. Element iOS is not distributed through the App Store. Element runs on a limited number of mobile devices, with the most widely supported being the iPhone. Element is not available on Android-based devices.
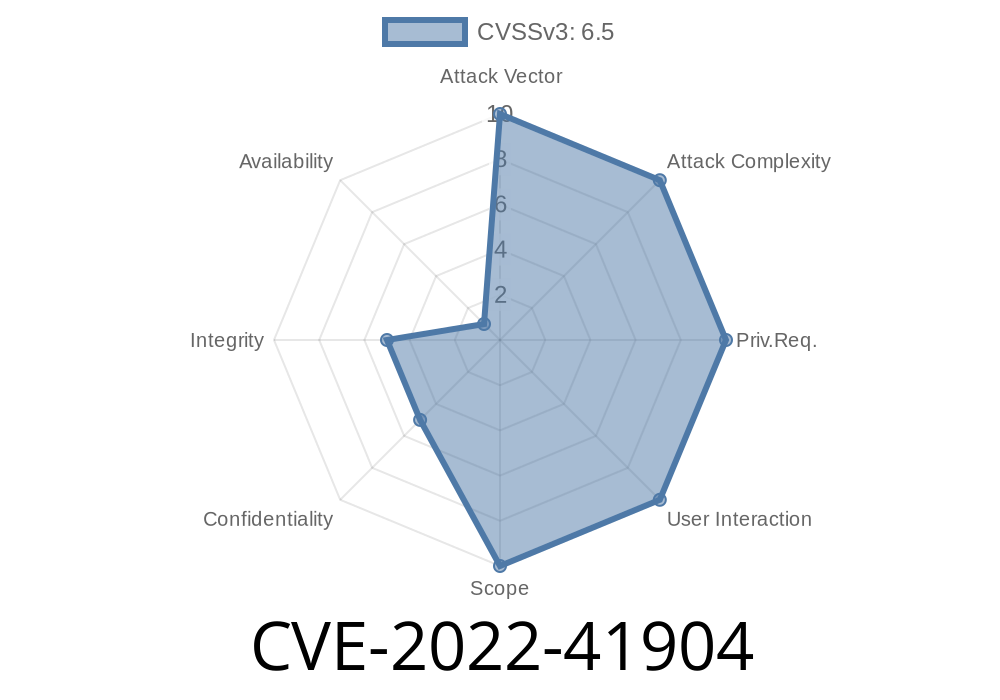
Products and services affected by CVE-2022-41904
Element is not available on Android-based devices.
Element is not available on Android-based devices.
Overview of Services
Element provides various services and functions for people to communicate over their mobile devices. These services and functions include group chat, the ability to share pictures and videos in a group, voice calls, video calling, and text messaging.
The most popular service is the group chat service. This service allows people to create groups of up to 250 members, and has features like scheduled events, private or public chats, global chat rooms where you can see what’s happening around the world. Group chats have features like access control settings that allow you to set your privacy level; this means that only specific people in your chat can message you privately or publicly. For example, you could have a private chat with your assistant so that they can send important information without letting everyone else know what’s going on. Another popular function is the ability to share pictures and videos in a group; this lets your members upload images from their phones into the group chat automatically when they’re sent media content. They can also share images from other apps onto their group chats as well!
Google Play Store
Google Play Store is a mobile application store and digital media platform operated by Google. The service was first announced in March 2012, as part of Google's Play Store branding of their online services.
The Google Play Store has so far been available on the Android operating system, but will be expanded to other platforms like iOS, Windows 10 Mobile and BlackBerry 10 in the future.
Originally, the intent of the service was to allow developers' apps to rise to the top of searches more easily than on other app stores like Apple's App Store or Amazon's Appstore for Android. However, because apps submitted to these services undergo a rigorous screening process before they are published, developers can also use them to generate revenue from users through advertisements or paid upgrades.
Information disclosure
Regarding information disclosure, it is known that Element provides an API. The API allows application developers to access and control the following functions:
• Reading and writing documents in a user's personal folder
• Sending SMS messages to phone numbers and reading the status of SMS messages received
• Forcing the device into Airplane mode
• Changing the language of the device
The API is restricted to app developers only, who must agree not to reverse engineer or decompile the Element source code. In addition, app developers using the API for commercial purposes must agree not to distribute applications containing any of these functions without written permission from Element.
Vulnerability overview
A vulnerability in Element's Android application has been discovered.
This vulnerability allows an attacker to obtain any file on the device and then delete all other applications.
The attacker could then change the permissions of the deleted applications to run as root which would give them complete control over the device. This includes running applications without user interaction, installing malicious apps, and sending text messages from someone else's phone.
Element developer responses have been limited and unsatisfactory.
Timeline
Published on: 11/11/2022 19:15:00 UTC
Last modified on: 11/16/2022 16:56:00 UTC