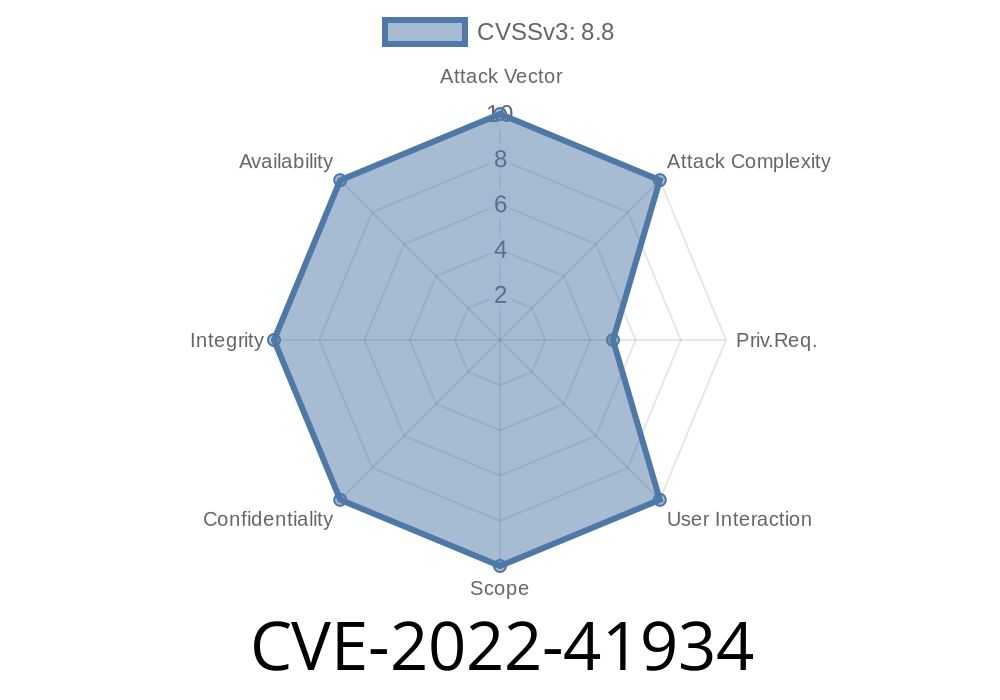
If you’re running an XWiki instance, here’s a serious heads-up: CVE-2022-41934 exposes a Remote Code Execution (RCE) vulnerability in XWiki’s core menu macro. This means that users with basic access can run system-level code in Groovy, Python, or Velocity—enough to take full control over your XWiki installation. Let’s break down what this means, how exploitation is possible, and most importantly, how to fix it.
What is XWiki?
XWiki is a powerful, Java-based, open-source wiki platform built for extensibility. Companies use it for everything from documentation to internal knowledge bases because it lets you run rich applications right on top of it.
Explaining CVE-2022-41934
- Vulnerability: Improper escaping of input in the "menu" macro lets malicious users inject executable code.
Who’s affected: Anyone running XWiki 11.6 or later—basically, almost everyone.
- Requirements: Just "view" rights on an accessible document is enough. This is a low bar—any logged-in user can pull this off.
Why is this dangerous?
The menu macro is widely used for navigation and is accessible from lots of commonly viewed documents. XWiki supports Velocity, Groovy, and Python scripting in macros. If content or parameters can slip through without being sanitized, attackers can inject and execute arbitrary server-side scripts.
Imagine this scenario
You’re a regular user, you can create or edit a document that uses the menu macro. Here’s a classic attack vector: inject malicious Velocity code right inside the menu macro’s field.
Insert the following somewhere the menu macro is parsed (even as a parameter)
{{menu macro="velocity"}}
#set($e = $xwiki.getClass().forName('java.lang.Runtime').getRuntime().exec('touch /tmp/hacked'))
{{/menu}}
*This payload will execute a command to create a file /tmp/hacked on the server.*
Links to External References
- Official CVE Entry
- XWiki Security Advisory
- Patch in Menu.MenuMacro Document (commit 2fc20891)
- Description on XWiki Issue Tracker
How Was it Patched?
XWiki maintainers patched this by properly escaping macro content and parameters to block malicious code from being parsed as server-side script.
14.4.3
If you’re running any of these or later, you’re safe.
For manual patching
You can grab the fixed Menu.MenuMacro document and update it in your instance.
Direct link to fixed source
- For XWiki 11.6–13.x, use commit 59ccca24a.
Monitor logs for suspicious menu macro usage or unexpected file creation.
3. Restrict user permissions where possible—limit document editing and macro usage to trusted users.
Takeaway
CVE-2022-41934 is nothing to take lightly. It’s easy to exploit, requires minimal access, and gives the attacker full control of your XWiki server. Patching is straightforward, so don’t wait—update your XWiki installation or apply the patch right now!
Stay safe!
*Exclusive post for security enthusiasts. Be sure to review your instance and check out the official fixes before someone else does.*
Timeline
Published on: 11/23/2022 20:15:00 UTC
Last modified on: 11/30/2022 17:30:00 UTC