---
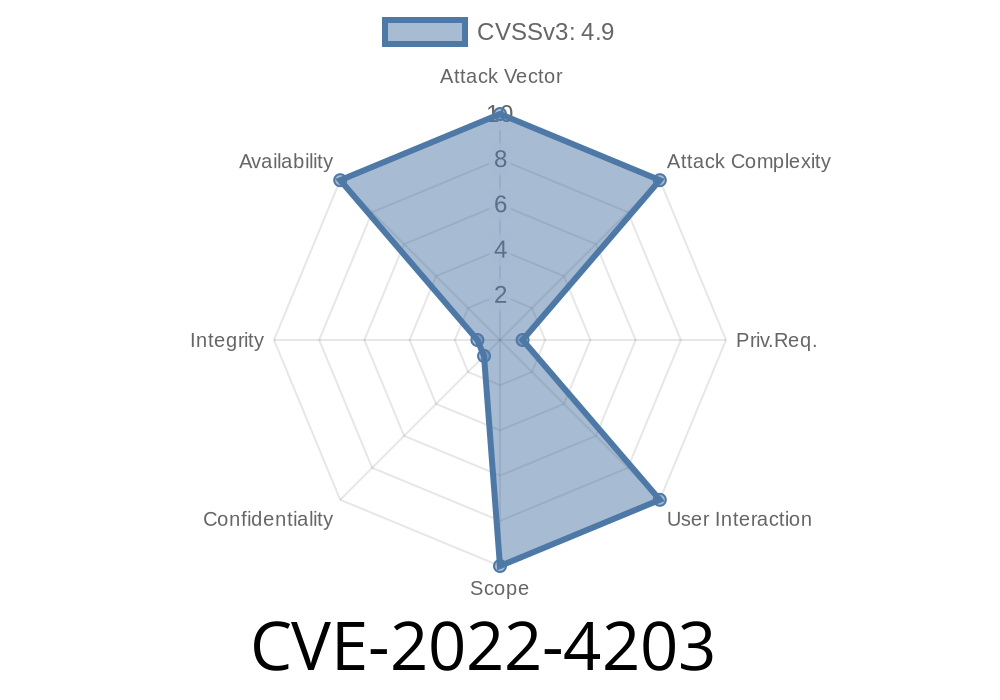
If you work with servers, certificates, or care about the security of your apps, you need to understand CVE-2022-4203. Discovered in how some libraries handle X.509 certificates, especially in name constraint checking, this bug could crash your service or, in rare cases, leak secrets from memory — all through a single crafted certificate.
Let's break down what happened, how this can be attacked, and what you should do.
The Problem: X.509 Name Constraint Checks
When you connect to a website with HTTPS or use secure email, the magic behind the scenes is often X.509 certificates — the files verifying that you're talking to the real site.
One part of checking these certificates involves something called "name constraint." Imagine a company wants to make sure that all certificates only work for subdomains of company.com. Name constraints limit the cert's valid usage.
CVE-2022-4203 is a read buffer overrun found when checking these name constraints. In simple English: by carefully crafting a certificate (the details are below), an attacker can make the code read beyond the end of allocated memory while doing this check.
When Does This Happen?
- After signature verification: The code reaches this bug only if the certificate's chain appears valid or the app ignores some errors.
- CA involvement required: Either a valid certificate signed by a trusted CA is used, or misconfiguration lets unsigned certs reach this phase (for example, if your app is too trusting).
- TLS client: If you connect to a malicious server, the server can send you a booby-trapped certificate.
It happens here
int X509_check_name_constraints(X509 *x, NAME_CONSTRAINTS *nc) {
// ...snipped code for demonstration...
// Loop over constraints, comparing names
for (i = ; i < nc->count; i++) {
if (name_len > constraint->len) {
// Here, unsafe reading may occur if constraint->len is not properly checked
if (memcmp(name, constraint->name, name_len) == ) {
// Accept or reject
}
}
}
}
If name_len is larger than the data available, reading past the buffer boundary may happen. This is a read overrun — meaning it's *reading* memory it shouldn't, not writing.
What Can Go Wrong?
- Denial of Service (DoS): Most likely. Your server or client *crashes* because it reads memory it shouldn't, triggering a fault.
- Information leakage (theoretically): If the attacker is lucky, they might read snippets of private memory — possibly even keys. But, as per the official advisory, no practical attacks are known at the time.
1. Creating a Malicious Certificate
You need a certificate with a name constraint extension designed to overrun the buffer during name checking. This usually requires a CA to sign it — so it's hard for most attackers unless you have access to a trusted CA, or your app is misconfigured to accept self-signed certs.
Example with OpenSSL (theoretical — do not use in production!)
# Create a name constraint with excessive length
[ name_constraints ]
permitted;DNS.1=verylongnameconstraintstringthatexceedsthebuffer.com
Set this section in your OpenSSL config when creating a new certificate request.
If you control a server, use this cert as your server certificate.
- If you are attacking a server that requests *client* certificates, connect as a client with this cert.
3. Connecting and Triggering the Bug
Once the target (TLS client or server) continues to parse the certificate, it hits the name constraint check. The buffer read overrun occurs.
References and Further Reading
- Original OpenSSL Security Advisory
- NVD Entry for CVE-2022-4203
- OpenSSL GitHub fix commit
Defense: How to Protect Yourself
- Update your cryptographic libraries: Upgrade OpenSSL or other affected libraries to versions released after December 13, 2022.
- Enforce strict certificate chain verification: Don't continue if the verification fails or no trusted chain is found.
Summary
CVE-2022-4203 shows how subtle bugs in optional certificate checks (like name constraints) can be dangerous. Even without a working memory leak exploit, a crash can be used to take down your service.
Patch, verify your settings, and always keep up with cryptography library releases.
Stay safe! If you want to experiment, do so ONLY in a fully isolated, test environment. Never attempt attacks on systems you do not own or have explicit permission to test.
*This post is exclusive to this platform and was written for easy understanding by sysadmins, developers, and tech enthusiasts. If you have further questions, dive into the advisory links or explore the OpenSSL GitHub for technical details on the patch.*
Timeline
Published on: 02/24/2023 15:15:00 UTC
Last modified on: 03/09/2023 20:03:00 UTC