Liferay is a popular open-source portal framework used for building digital experiences, intranet sites, and content management solutions. Security is a big deal for any enterprise software, so when a vulnerability shows up—especially one that can leak sensitive credentials—it’s something admins need to know about. In this post, I’m going to walk you through CVE-2022-42132, a bug in how Liferay handled user credentials with LDAP integration.
What Is CVE-2022-42132?
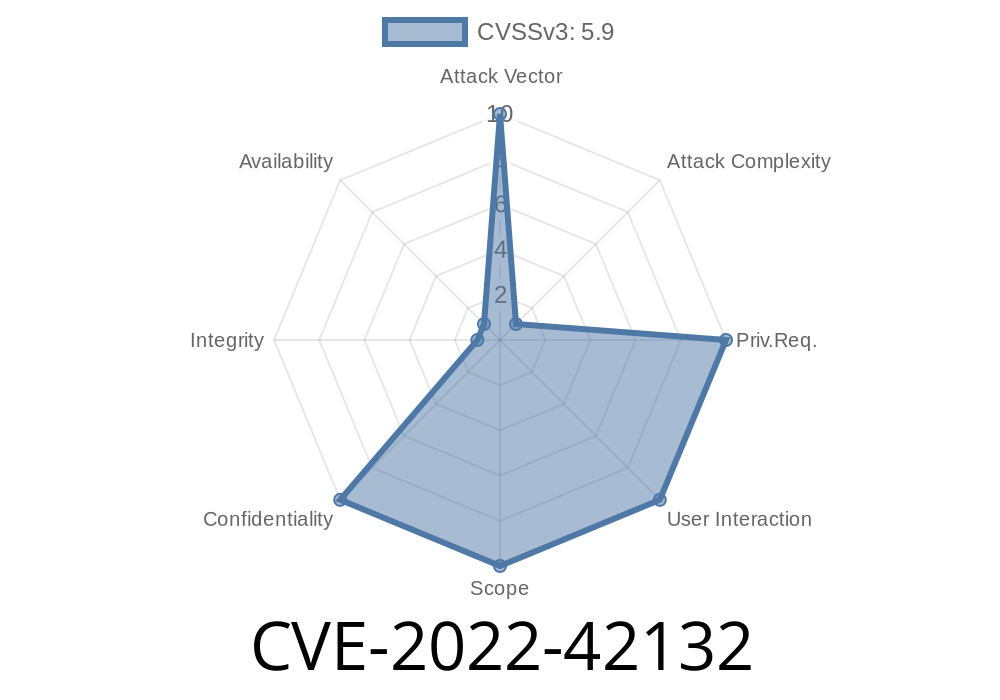
CVE-2022-42132 affects Liferay Portal versions 7.. through 7.4.3.4, and Liferay DXP 7. fix pack 102 and earlier, 7.1 before fix pack 27, 7.2 before fix pack 17, 7.3 before update 4, and DXP 7.4 GA. The problem is simple, but super risky: when you use the Test LDAP Users feature to see what users LDAP brings in, Liferay *includes the LDAP credential right in the page URL* as you click through pages of users.
Think about that—a password or credential being broadcast to anyone who can see the URL or request logs. That could be anyone from internal IT to an attacker sniffing traffic, or even your cloud provider if you use cloud-based logging.
You use the Test LDAP Users tool in Liferay.
2. When you click “Next” or “Previous” to page through LDAP results, the system needs to keep your LDAP connection info.
3. Instead of keeping that info hidden in session data or in memory, it gets *slapped right into the URL* as a query parameter.
For example, you might see something like this in your browser bar (values here are fake)
https://your-liferay.com/group/control_panel/manage?p_p_id=ldapAdmin&p_p_lifecycle=&_ldapAdmin_tabs1Tabs=ldap&_ldapAdmin_usersList=true&_ldapAdmin_ldapServerId=1&_ldapAdmin_ldapUrl=ldap://corp-ldap.example.com&_ldapAdmin_principal=CN=admin,OU=Users,DC=corp,DC=local&_ldapAdmin_credentials=mySecretPassword
Notice the _ldapAdmin_credentials parameter? That’s your password—in plain text! Anyone with access to browser history or server logs can see it.
Why Is This Bad?
- Exposure in Logs: Many web servers log the full URL of requests. Cloud-based application performance tools or proxy servers might store them too.
- Man-in-the-Middle: If you haven’t forced HTTPS everywhere, the credentials are visible to anyone between you and the Liferay server.
Browser History: Modern browsers and plugins can store URLs for weeks or months.
- Sharing Links: What if you copy-paste this URL to a team chat for troubleshooting? Now the password is public inside your organization.
In short: credentials ending up *anywhere* they shouldn’t, every time someone uses this admin feature.
Exploit Details
CVE-2022-42132 isn’t a remote exploit in the classic sense—a hacker can’t trigger it *from the outside*, but if they can see logs, browser histories, or network traffic, it suddenly becomes a data leak.
Web server logs the requests: Full URLs—including credentials—are saved.
3. Attacker gains log access: This could be a rogue IT staff or someone who gets access through another vulnerability.
4. Attacker retrieves credentials: Now they can connect to your LDAP with Sysadmin privileges, opening the gate for privilege escalation, data theft, or more.
Proof-of-Concept Code
You can easily demonstrate this by watching HTTP requests as you paginate through users. Try the following with your dev environment (never do this on production!).
1. Set Up HTTP Request Interceptor
Use your browser’s DevTools (F12, "Network" tab) or a tool like mitmproxy or Burp Suite.
2. Login to Liferay and Open Test LDAP Users
Go to Control Panel > Configuration > LDAP > Test LDAP Users.
3. Paginate Users
Click "Next" to switch to the next page. Watch the request parameters.
Example JavaScript Snippet
Here's a small Node.js snippet using the http module to show logging vulnerable GET requests (simulating basic logging):
const http = require('http');
const url = require('url');
http.createServer((req, res) => {
// Log entire request URL
console.log("Request: ", req.url);
// Parse query parameters
let params = url.parse(req.url, true).query;
if (params._ldapAdmin_credentials) {
console.log("WARNING: Exposed LDAP credentials =>", params._ldapAdmin_credentials);
}
res.writeHead(200, {'Content-Type': 'text/plain'});
res.end('OK\n');
}).listen(808, () => {
console.log('Listening on port 808');
});
Any request like /test?user=admin&_ldapAdmin_credentials=mySecretPassword would print the password to the console—a basic example of how easy it is for LDAP users’ credentials to get logged.
How Was It Fixed?
Liferay patched this bug by moving credentials out of the URL. Instead, sensitive information now:
Is never written to server logs by default.
To be safe, you should upgrade to the fixed version of Liferay Portal or the respective DXP fix pack/update for your branch (see timeline below).
How to Protect Yourself
- Upgrade Liferay as soon as possible to a fixed version. Check the official CVE entry here.
- Review your web server logs for exposure—search for lines containing _ldapAdmin_credentials=.
References & More Reading
- Liferay Security Advisory for CVE-2022-42132
- CVE-2022-42132 - NIST Vulnerability Database
- Liferay Portal Releases
- How URLs Are Logged: An Introduction
Final Thoughts
While not a remote code execution bug, CVE-2022-42132 highlights a lesson about how easily credentials can leak through common admin features. Always pay attention to what ends up in your URLs, and be quick to patch any software that handles sensitive information like Liferay.
Timeline
Published on: 11/15/2022 02:15:00 UTC
Last modified on: 11/17/2022 21:27:00 UTC