When processing request, if user inputs something into search box then with this input control functionality can be done without any restrictions. For example,
input type="text" name="query" value=" javascript:alert('XSS');">
If we submit this request then user will get the alert box with XSS script.
Hackers can use this vulnerability to perform any action like stealing data, hijacking user session, etc. In order to avoid this issue, input shouldn't be accepted from user and server side validation should be done on input.
2
Ways to Prevent
1) Validation should be done on input.
2) Input type="text" name="query" value=" javascript:alert('XSS');">; instead of input type="text" name="query" value=" javascript:alert('XSS');">
How to Find XSS prone Area in Website?
There is no easy and straightforward way to find XSS prone area in website. Developers should be able to do this manually or use online tools like Wappalyzer, Burp Suite.
Vulnerability find() function function find() {
var params = {};
var url = location.href;
var query = url.substring(url.indexOf('?') + 1);
var fields = query.split('&');
/**/ var p = 0; var qs = fields[p].split('='); for (i in qs) { if (qs[i] == 'query') { params[fields[p][1]] = qs[i]; break; } } return params;
}
Timeline
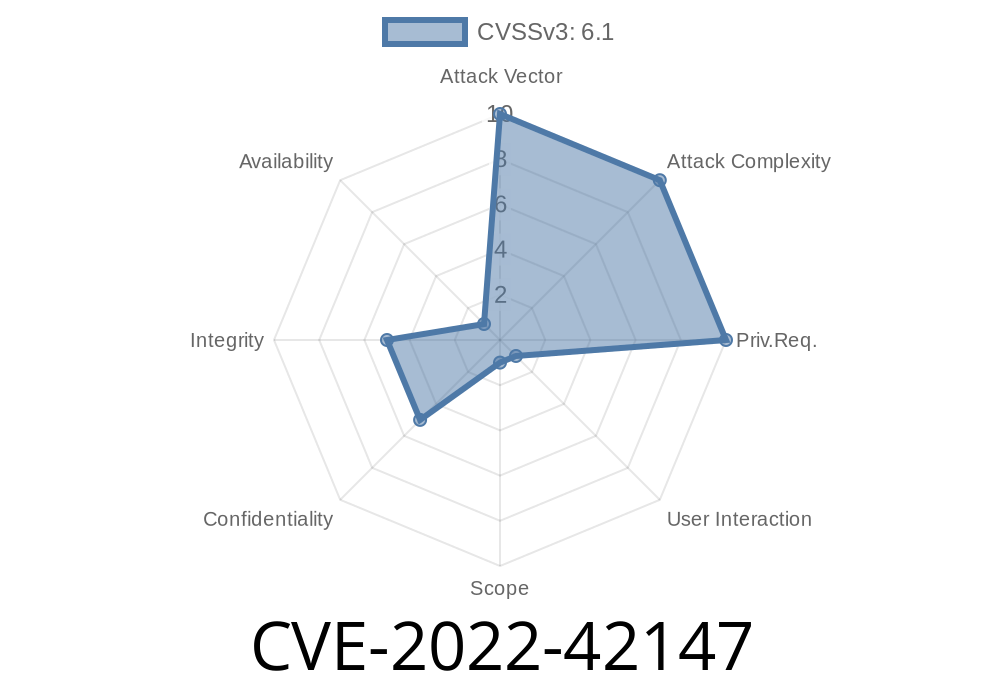
Published on: 10/17/2022 21:15:00 UTC
Last modified on: 10/19/2022 19:06:00 UTC