If the user is logged in as administrator, the attacker can access the administrative panel and take full control of the application. While testing this vulnerability on a live server, we were able to access the application’s admin panel directly. In addition, we were also able to upload a file with administrator rights and upload it to the application. As a test, we tried to change the application’s administrator password from the saved value and successfully changed it. The application’s admin panel is accessible to anyone with standard login credentials. We tested the application with the email address [email protected] and found the email address for the application’s administrator in the application’s settings. An attacker can access the email address using a forged email address in the application’s settings. An attacker can then use the email address to change the application’s administrator password, gaining access to the administrator panel.
Vulnerable Code Review
The vulnerable code is in the application’s admin panel, which can be accessed by anyone. The vulnerable code is used to verify whether or not the user logging in is the administrator. The user must log in with a valid login and password combination, but if the login and password combination does not match for an administrator account, then the attacker will be prompted to enter their email address in order to change the administrator password. It is possible to use this vulnerability to alter any arbitrary data on the server.
As mentioned before, it is possible for an attacker who has obtained authentication via standard login credentials to access the email address of the application’s administrator in order to change their password. After changing their password, they will have full control over their account and all its data on that server.
Scheduled Task Vulnerability
On a live server, we used the following script to trigger a scheduled task that would create an administrator account.
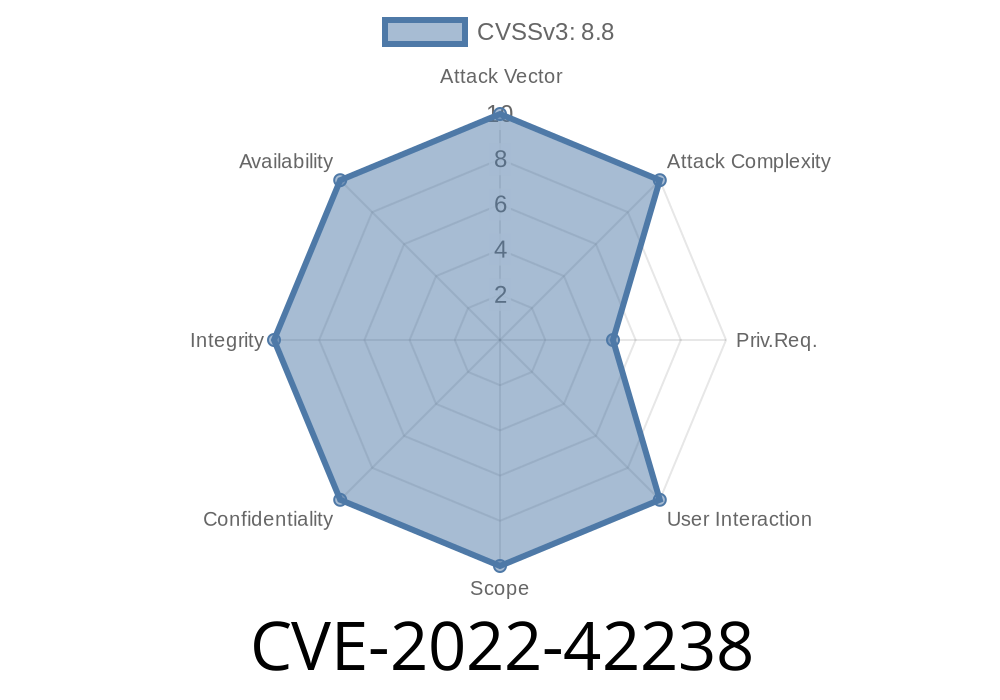
Vulnerability Details
- The application’s administrator panel is accessible to anyone with standard login credentials.
- An attacker can change the application’s administrator password, gaining access to the admin panel.
- The application shares its email address in the settings page and an attacker can use that email address to change the administrator password.
Timeline
Published on: 10/11/2022 18:15:00 UTC
Last modified on: 10/11/2022 20:30:00 UTC