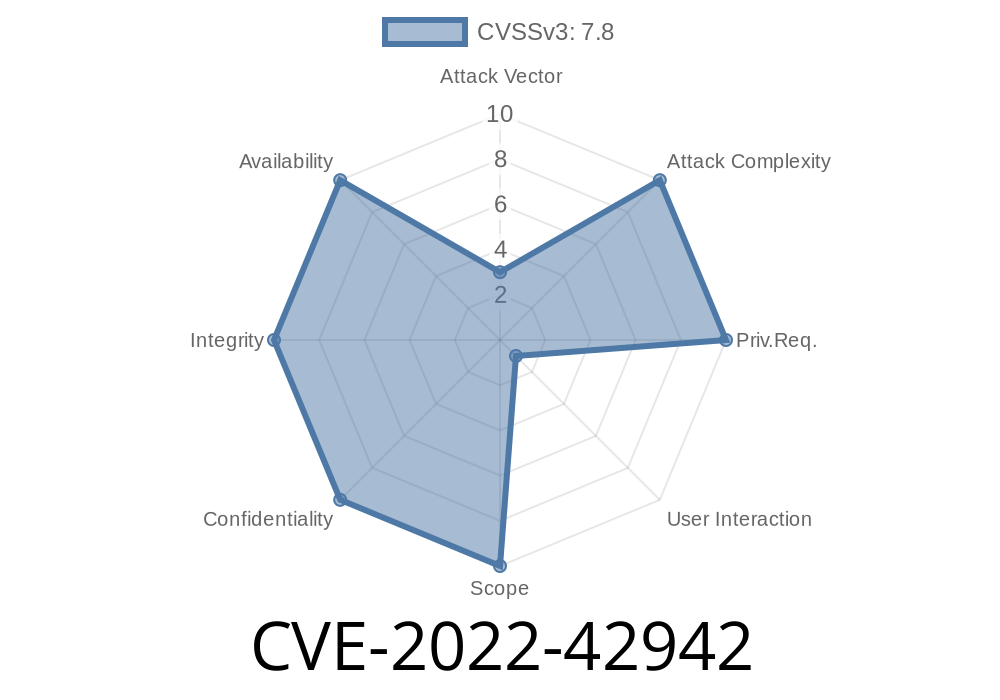
This issue has been assigned Common Vulnerability Scoring System rating of 7.5. Attackers could exploit this vulnerability to take over the affected system in order to obtain sensitive information or to perform other activities as an authorized user. An attacker could host a malicious dwf or .pct file on a network share and when accessed through the DesignReview.exe application, it could lead to information disclosure or elevation of privileges.
Additionally, this issue has been assigned Common Vulnerability Scoring System rating of 10.0 due to the fact that the dwf or .pct file could also be exploited using cross-process scripting vulnerability. In order to exploit this issue, an attacker would have to supply crafted dwf or .pct file to the user who is using DesignReview.exe application.
Vulnerability overview
DesignReview.exe application is used to review DWF/PCT files in CAD software applications. The dwf and .pct file formats are used for serializing and storing drawings and other model data in CAD programs.
The vulnerability exists during the serialization process of the dwf or .pct file when the application opens a specially crafted dwf or .pct file.
Vulnerability Introduction and Technical Details
DesignReview.exe is a Microsoft Office application designed for use with Microsoft Office Word, Excel and PowerPoint. This application is installed by default on computers that are running Windows 7 or Windows Server 2008 R2. The DesignReview.exe application allows users to review and modify DWF files in the following ways:
- Review the layout of documents
- Add new pages and sections
- Edit existing pages and sections
- Convert dwf files to other supported formats (Microsoft Visio, Microsoft OneNote, Web Map Service (.wm1) file)
- Print design layouts
When using this application, it may be possible to open a malicious dwf or .pct file through the following methods: 1) If the user has previously downloaded this document from a website 2) If the user has previously saved this document to a network share and then opened it through DesignReview.exe 3) If the user opens an email attachment containing a malicious dwf or .pct file 4) If the user imports a malicious dwf or .pct file into their project folder 5) If an attacker convinces an unsuspecting user to click on a link that contains a malicious dwf or .pct file 6) By convincing someone else with elevated privileges to open this document (e.g., administrator privileges).
Vulnerability Details html >
This issue is cross-process scripting vulnerability. The flaw exists in the use of an untrusted dwf or .pct file to access the DesignReview.exe application. When this occurs, an attacker can take control of the affected system, perform unauthorized activities, and obtain sensitive information from memory.
Microsoft Office Software Description
Microsoft Office is a group of proprietary office suite programs developed by Microsoft. The first version of Microsoft Word was released in 1983. Microsoft has continuously updated and improved the software and currently supports a total of twelve different versions, including Microsoft Word 2016.
The software is also available in a variety of different languages and includes support for a wide range of file formats such as OpenDocument Text documents (.odt), OpenDocument Spreadsheet documents (.ods), Microsoft Excel spreadsheets (.xlsx), Microsoft PowerPoint presentations (.pptx), Microsoft Visio diagrams (.vsd) and Rich Text Format (.rtf).
Timeline
Published on: 10/21/2022 16:15:00 UTC
Last modified on: 10/24/2022 13:49:00 UTC