XSS vulnerabilities can be exploited by attackers with low skill levels to execute malicious code on a user's browser or device. In order to exploit this issue, an attacker would need to submit a malicious payload via the Add function. Eramba GRC Software is vulnerable if any user creates a KPI as shown in the example below. Add function of Eramba GRC Software c2.8.1 allows users to create arbitrary KPI values. In this example, we will demonstrate how to create a KPI value of ‘XSS’. This is a simple demonstration of adding a XSS payload to create a XSS attack vector: - Create a new KPI value (e.g. XSS) and assign it to the KPI Title field. - Create a new KPI value (e.g. XSS) and assign it to the KPI Description field. - Add a new value to the KPI.
The Add Function of the Eramba GRC Software
The Add function is exposed to users via the /cgi-bin/add_kpi.php page and takes an arbitrary number of parameters, some of which are optional as shown in the example below:
/cgi-bin/add_kpi.php?action=Add&title=XSS&description=XSS
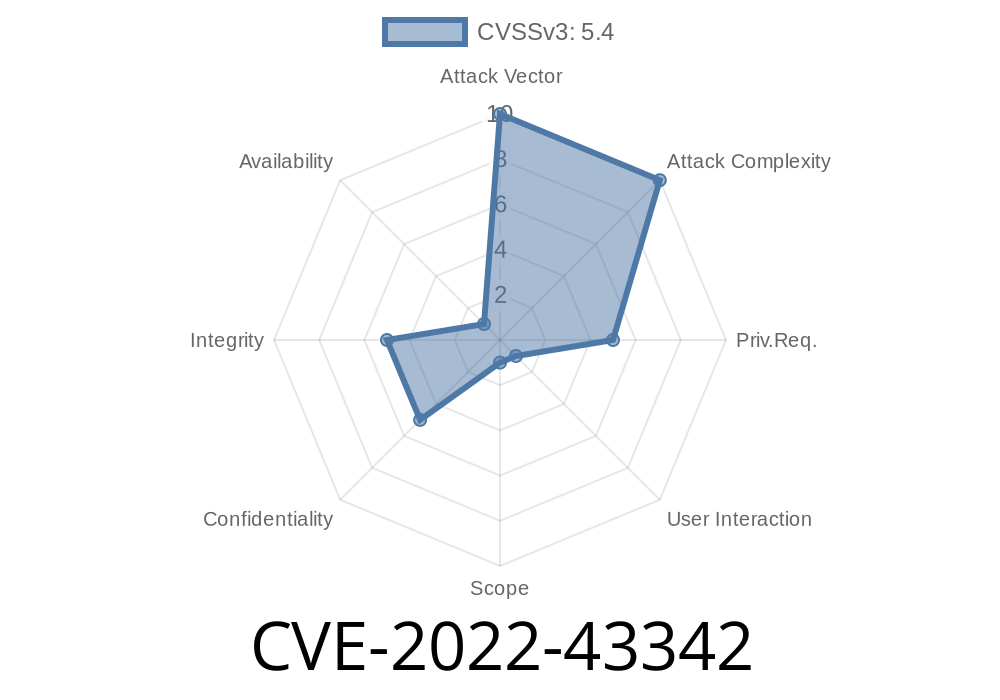
In this example, we are adding a new KPI value ‘XSS’ with a title of ‘XSS’ and a description of ‘XSS’. In order to exploit CVE-2022-43342, an attacker would need to submit a malicious payload via the Add function as shown in the example below:
/cgi-bin/add_kpi.php?action=Add&title=XSS&description=
Timeline
Published on: 11/14/2022 16:15:00 UTC
Last modified on: 11/16/2022 20:58:00 UTC