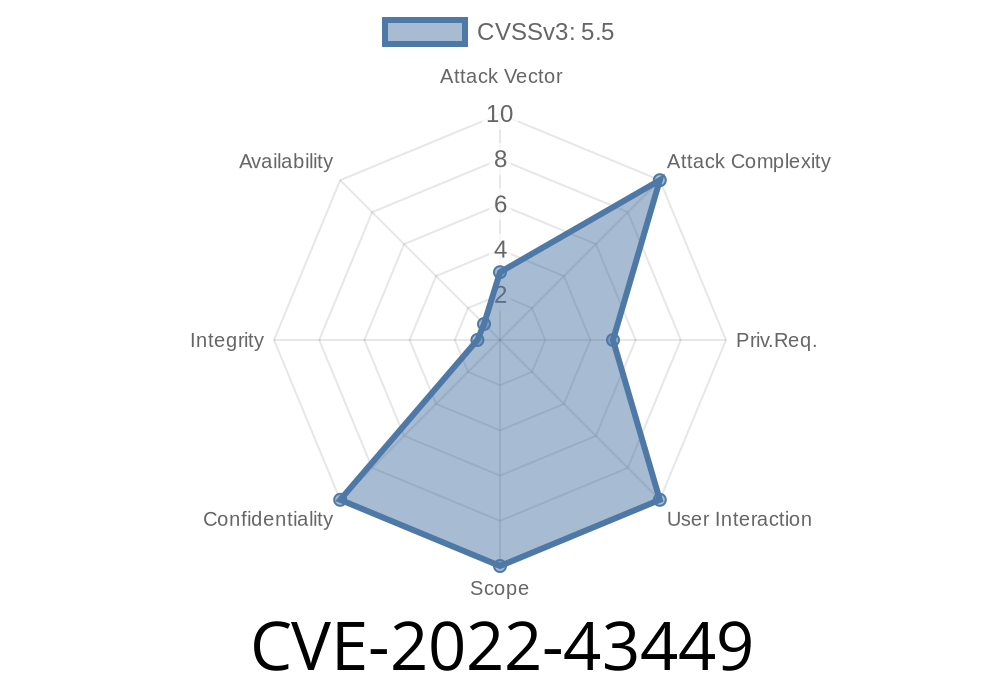
In late 2022, a serious security flaw, CVE-2022-43449, was publicly disclosed affecting OpenHarmony-v3.1.2 and earlier versions. This bug allows local attackers to access almost any file on the device due to a poorly protected component called download_server. The vulnerability could be exploited simply by installing a malicious app, making it a major risk for anyone using an affected device.
In this article, you’ll learn what makes this bug possible, see code examples to reproduce it, and explore mitigation strategies. You don’t need to be an expert — we’ll break it all down using easy-to-read language.
What Is OpenHarmony?
OpenHarmony is an open-source operating system designed for smart devices (think IoT, smart TVs, and even smartphones). Like Android, it’s highly modular, but that also means vulnerabilities can quickly spread across devices.
Privilege Required: Local (app installed by user)
- Impact: Any file accessible by the download_server service (UID 100) can be read and exfiltrated
Reference:
- https://www.openharmony.cn/security/updates/2022/11/11/CVE-2022-43449
- https://nvd.nist.gov/vuln/detail/CVE-2022-43449
How Does the Vulnerability Work?
The download_server is a system service responsible for file downloads. It runs with Android system privileges (UID 100), which provides access to sensitive data and system files.
The service doesn’t check if a requesting app is authorized to access a file.
- Given a file path, it just returns the file’s content, as long as that file is readable to the download_server process.
A malicious app simply talks to download_server, requests /data/system/users//accounts.db (for example), and gets its contents back!
Example Exploit (Proof of Concept)
*Disclaimer: This is for educational purposes only. Don’t use this information on systems you do not own.*
Suppose the service exposes an IPC method (likely via Binder interface) like this (pseudocode)
// pseudo-interface of download_server
interface IDownloadServer {
String downloadFile(String filePath);
}
Here’s a simplified sketch of the attacking code
// Normally you'd use reflection or AIDL to get the service binder
String secretFile = "/data/system/users//accounts.db"; // a sensitive file
// Example call to the download_server service
String fileContent = downloadServer.downloadFile(secretFile);
// Output the stolen content
Log.d("HackerApp", "Got secret data: " + fileContent);
Result:
The downloadFile method reads the file and returns its content, regardless of whether your app should have access or not.
Elevate their permissions by extracting and reusing system files.
Typically, these files should only be accessible by the OS, but *any* local app can get them this way.
Patch Reference
OpenHarmony Security Advisory:
OpenHarmony Security CVE-2022-43449 (official fix details)
Summary
CVE-2022-43449 is a critical local file disclosure bug in OpenHarmony OS, allowing any installed app to take over your data. If you’re using affected devices, update soon. If you make or sell devices using OpenHarmony, patch immediately and review your internal permission checks.
Stay safe, and always keep your smart devices updated!
References
1. OpenHarmony Official Advisory
2. NVD Entry CVE-2022-43449
3. OpenHarmony Website
*Exclusive analysis for learning only. Please act responsibly and always practice ethical security!*
Timeline
Published on: 11/03/2022 20:15:00 UTC
Last modified on: 11/07/2022 02:18:00 UTC