After updating the trusted_domains config option to a different value, ownCloud Server on 10.11 will no longer trust the domain when receiving password reset e-mails. This can be used to prevent users from resetting their own passwords on their own accounts. In order to exploit this vulnerability, an attacker would have to send an e-mail with malicious content to each of the user’s ownCloud Server contacts. This list can be quite large and can be done by sending e-mail messages to the e-mail addresses of the user’s family members and friends. The content of the malicious e-mail message would have to contain links to a password reset page that would be hosted on a server that is not on the trusted_domains list. This would force the user to click on the links in the e-mail and would result in a password reset request to the attacker’s ownCloud Server. The attacker would then have to host a password reset page on their ownCloud Server that would have the malicious password reset form. This could be done by using the hostnames of the user’s ownCloud Server contacts.
Prerequisites
1) Make sure the trusted_domains config option is set to a different value.
2) Set the hostnames for your ownCloud Server contacts in the e-mail settings of the Contact app.
3) Send a message without malicious content to each of your ownCloud Server contacts with links to your password reset page.
4) Use an attacker’s ownCloud Server account to send an e-mail message containing links to a password reset page on your ownCloud Server that would force the user to click on them and enter their password.
The attack vector will only be successful if the user enters their own password on this form, which is why it is important that you use a session cookie with a long expiration time, or even better, you use two-factor authentication.
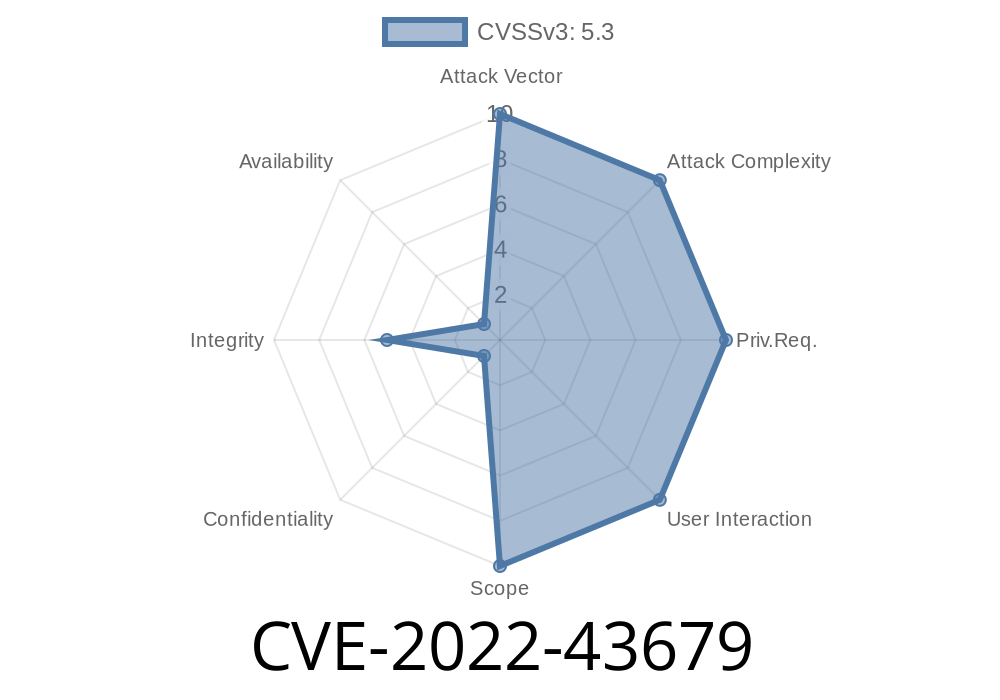
Vendor Response: Learn more about CVE-2022-43679
OwnCloud has already released a patch to fix this vulnerability. If you are running 10.11 and have not installed the patch, then you can contact the vendor for instructions on how to install the fix.
The importance of digital marketing spans across many different areas of business. It can be difficult to stay competitive in today's digitally-driven world where companies must compete with one another for online exposure. For this reason, it is important that businesses invest in their digital marketing strategy by using SEO and PPC advertising to connect with their target audience through creative advertisements.
How to Bypass OwnCloud’s Password Reset Protection
This vulnerability can be exploited by an attacker by sending malicious e-mail messages to each of the user’s ownCloud Server contacts. The content of the malicious e-mail message would have to contain links to a password reset page that would be hosted on a server that is not on the trusted_domains list. This would force the user to click on the links in the e-mail and would result in them logging into a malicious URL they believe they are visiting. The attacker would then have to host a password reset page on their ownCloud Server that would have the malicious password reset form. This could be done by using the hostnames of the user’s ownCloud Server contacts. Unfortunately, there is no way for an administrator to prevent this vulnerability from being exploited without disabling password reset protection or restricting access to requests for password resets from specific IP addresses.
Timeline
Published on: 11/10/2022 21:15:00 UTC
Last modified on: 11/15/2022 19:44:00 UTC