If you are running a version before 9.1.3, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin. If you are on 9.1.3, upgrade immediately. If you are on 8.5.10, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin. If you are on a version before 9.1.3, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin. A possible authentication bypass was discovered where the legacy_salt in concrete5 could be used to bypass authentication. This has been fixed in concrete5 9.1.3+ and 8.5.10+. If you are on a previous version, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin.
Summary
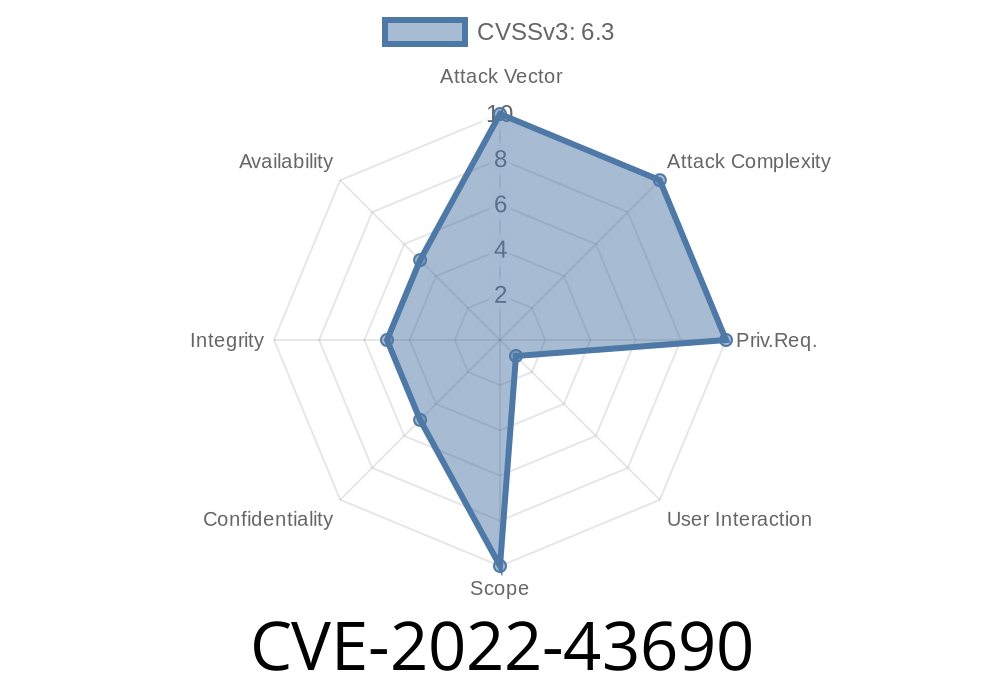
A possible authentication bypass was discovered where the legacy_salt in concrete5 could be used to bypass authentication. This has been fixed in concrete5 9.1.3+ and 8.5.10+. If you are on a previous version, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin.
What you need to know about concrete5 authentication bypass vulnerability
Version 9.1.3+ and 8.5.10+ are the only versions that currently have this vulnerability fixed. If you are on a version before 9.1.3, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5.
How to protect yourself from this vulnerability
If you are running a version before 9.1.3, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin. If you are on 9.1.3, upgrade immediately. If you are on 8.5.10, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin. If you are on a version before 9.1.3, update as soon as possible. We do not yet know if this vulnerability affects other versions of concrete5. Stay updated on the concrete5 security bulletin
A successful attack can be launched against your application without any user interaction or administrator action required to exploit it
Timeline
Published on: 11/14/2022 23:15:00 UTC
Last modified on: 11/17/2022 05:20:00 UTC
References
- https://github.com/concretecms/concretecms/releases/8.5.10
- https://documentation.concretecms.org/developers/introduction/version-history/913-release-notes
- https://documentation.concretecms.org/developers/introduction/version-history/8510-release-notes
- https://www.concretecms.org/about/project-news/security/concrete-cms-security-advisory-2022-10-31
- https://github.com/concretecms/concretecms/releases/9.1.3
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-43690