This type of XSS allows an attacker to execute arbitrary code on behalf of the user.
Impacted sites may appear to function normally, but users are encouraged to upgrade to one of the latest versions of concrete5 (9.2.0 or later) to mitigate the risk of this vulnerability. If a concrete5 installation was upgraded to a version of the software prior to 9.2.0, users are encouraged to upgrade their installation immediately to avoid any potential exposure due to this issue.
What is an XSS?
An XSS is a type of cross-site scripting vulnerability that occurs when a user enters input into one website, which gets processed and then sent back to the attacker's site.
The input is often web-based, but can also be in an email or a message. With this type of vulnerability, the attacker could execute any code on behalf of the victim.
Mitigation strategies for CVE-2022-43694
While concrete5's XSS filter is designed to mitigate the effects of this vulnerability, there are a few steps that can be taken to further reduce the risk of exploitation:
- Remove any use of untrusted input in input fields on your site
- Ensure all script tags are properly encoded
- Implement cross-site request forgery prevention.
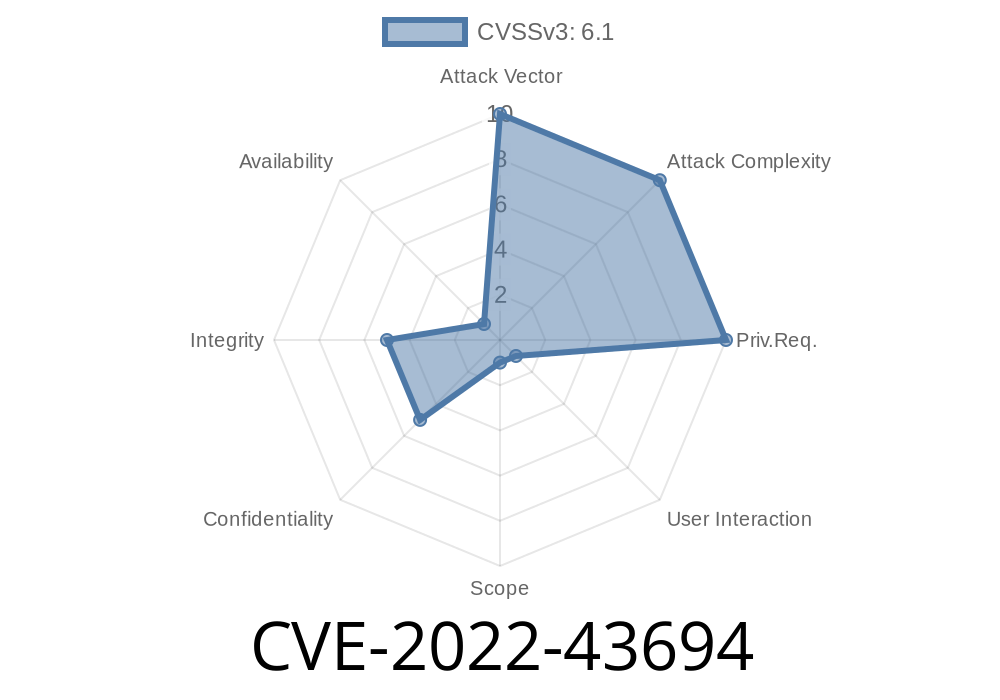
Vulnerability Details
The vulnerability is caused by a flaw in the way that concrete5 processes user-supplied data. This is most commonly found when concrete5 allows the input of HTML content during the editing process, but it can also be triggered via an XSS attack or through other methods. The vulnerability will allow an attacker to execute arbitrary code on behalf of the victim's account without requiring any credentials.
To exploit this issue, a malicious site should be created which contains html/javascript code that would cause concrete5 to process user-supplied data. This can be done by hosting a malicious web page and using AJAX requests to retrieve the vulnerable content from his console, or by using a website tool such as Burp Suite to craft a similar problem (for example, see Burp Suite's "XSS Payloads" section for related information).
The vulnerability can then be exploited by sending XSS payloads to the vulnerable site in order to trigger it. Once triggered, this will allow an attacker to execute arbitrary commands on behalf of the user that was originally targeted.
How do I know if my site is vulnerable?
To determine if your site is vulnerable, review the following:
- Do you use concrete5?
- If so, what version of the software do you have running on your site?
- Is a user visiting your website running an operating system with a supported browser?
Timeline
Published on: 11/14/2022 19:15:00 UTC
Last modified on: 11/16/2022 23:12:00 UTC
References
- https://github.com/concretecms/concretecms/releases/8.5.10
- https://documentation.concretecms.org/developers/introduction/version-history/913-release-notes
- https://documentation.concretecms.org/developers/introduction/version-history/8510-release-notes
- https://www.concretecms.org/about/project-news/security/concrete-cms-security-advisory-2022-10-31
- https://github.com/concretecms/concretecms/releases/9.1.3
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-43694